60%
Small businesses' will close after experiencing a data breach within 6 month according to Experian.
"Most businesses, in my experience, are ill-prepared to handle a cyber attack; very few even know where their data is backed up to or if their backups are even good..."
— Jackob S, CIO Consultant
Need To Secure Your Systems?
FACTS
Antivirus alone will not keep your business safe from a cyber attack.
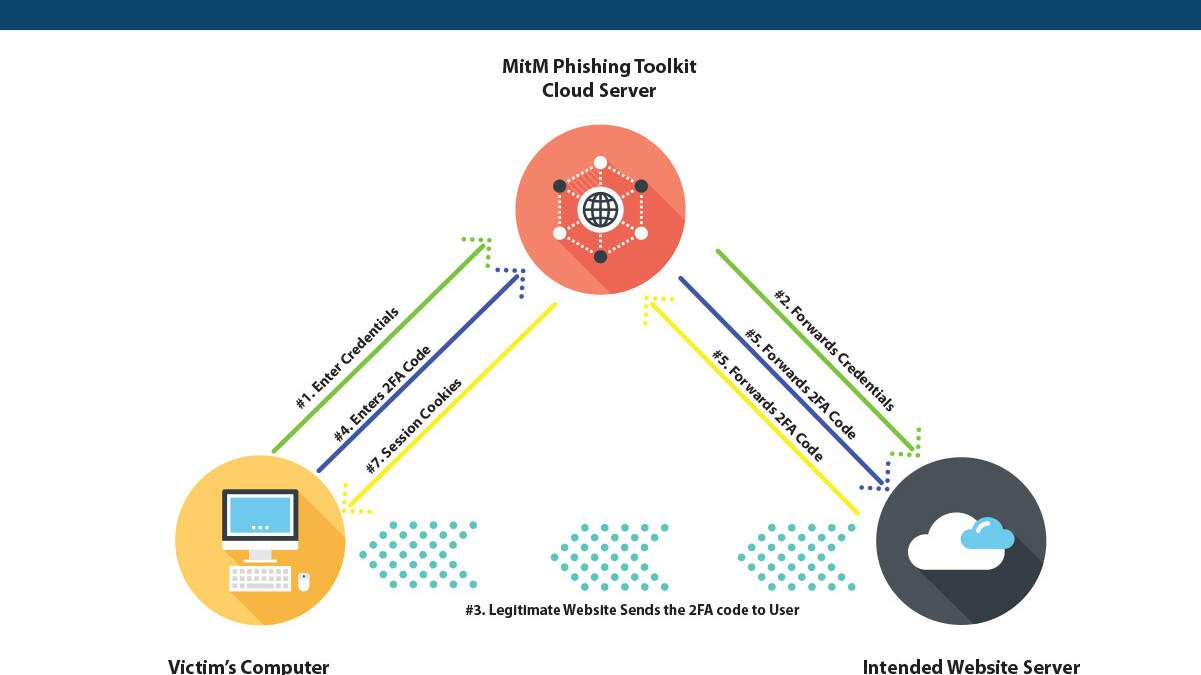
Most common cyber threats are socially engineered attacks such as phishing designed to steal passwords or install malware on your machine. Cyber criminals gain control of the infected machine and using windows features and legitimate programs infiltrate your network, steal data, and encrypt your systems. We put in place products, services, procedures, and strategy designed to prevent your organization falling victim the attacks such as:
PHISHING ATTACKS
Antivirus does not offer a robust cloud filter that scans emails prior to you receiving them in your mailbox. Office 365 alone does not offer an effective email spam filtering solution
ZERO-DAY MALWARE
Antivirus scans file signatures and compares them to previously known definitions of malicious code. Zero-Day is malware that does not have the definition yet and would go unnoticed by most Antivirus programs
RANSOMWARE
Ransomware could encrypt your system by using built-in Windows functionality like Bitlocker. Antivirus would not perceive this as a threat and allow the encryption to continue
BROWSER PLUGIN
Much of the malware like key loggers will get it’s way into a computer using a browser extension that if user is allowed to install would often times bypass most Antivirus solutions
ABNORMAL BEHAVIOR
Antivirus does not monitor data usage, such as what would be present if threat actors would be offloading your data to their server prior to encrypting it. (Data Breach)
OUTDATED ANTIVIRUS
Antivirus constantly updates for new threats as they emerge, so if your subscription runs out, or you ignore the update, it will render the antivirus less effective
GIVING YOU PEACE OF MIND IS WHAT WE DO!
ZERO TRUST
Limiting what the user can access and do to only the minimum permissions needed to perform their jobs. This includes not only file access but limiting what can be installed and ran on a computer
MONITORING BEHAVIOR
Once a user's typical work day is learned and set, we can use this as a baseline for the "norm." Our software then scans for or blocks activity that falls outside the "norm." All virus definitions and updates are centralized and standardized so that a user is not responsible to keep up with updates
CLOUD SERVICES PROTECTION
With cloud services becoming the new norm, keeping your cloud infrastructure protected is more important now than it has ever been. Putting in place safeguards to ensure your data, customer data, and your systems are protected is crucial to overall security of your organization. We eliminate threat vectors and reducing attack surface as part of keeping your cloud infrastructure secure.
EMAIL SPAM FILTERING
We incorporate machine learning AI cloud based spam filtering. This means in addition to your Office 365, it scrubs emails prior to delivering them to your mailbox. Greatly limiting your exposure to phishing attacks
BUSINESS CONTINUITY
Develop an action plan of how to mitigate damages and continue business function in case of a cyber attack. This comprehensive plan is designed to give you the peace of mind knowing that your business will continue to function after an attack. Part of the planning includes setting up and testing backup and restore systems. Developing a playbook with step by step plans of what employees should do in case of such an attack.
POLICY & PROCEDURES
We help developing a comprehensive cyber security policy and procedures for your company that will be at the core of keeping your organization protected from the employees themselves. Since most attacks are socially engineered ensuring your company has proper employee policy and procedures in place will help safeguard your systems.
"I am so happy I chose to go with Alphacis to manage our systems and security. I receive weekly reports, and know that my company is truly protected from external threats"
-Trent B. CEO
SCHEDULE A QUICK CALL TO SEE HOW ALPHACIS CAN PROTECT YOUR BUSINESS FROM CYBER THREAT

SPEAK WITH AN IT CONSULTANT. NOT A SALES GUY!
EXPLAIN YOUR BUSINESS TECHNOLOGY NEEDS
RECEIVE AN ESTIMATE WITH PRICING AND OUR SOLUTION BROKEN OUT IN DETAILS
NO PUSHY SALES GUYS OR FOLLOW UP SPAM MAIL
Latest News in Cyber Threats
Industry news, threats and highlights in the tech world.
IT vs OT Security Manufacturing: Critical Gap Analysis 2026
May 20, 2026
Article Summary • Who this is for: Manufacturing companies, plant managers, operations leaders, and IT directors responsible for securing industrial environments with connected IT and OT systems. Ideal for manufacturers running PLCs, SCADA systems, legacy equipment, or multi-site production operations. • The challenge: Most manufacturers have a dangerous security gap between corporate IT systems and operational technology (OT) networks. Poor segmentation, shared credentials, outdated…
How Hackers Target Small Businesses in 2026
May 18, 2026
Article Summary • Who this is for: Small business owners, CPA firms, law firms, healthcare practices, and professional service companies with 10–100 employees that rely on Microsoft 365, cloud apps, and employee-managed systems but lack enterprise-level cybersecurity resources. • The challenge: Cybercriminals are systematically targeting small businesses through phishing, credential theft, ransomware, and lateral network attacks because most companies lack proactive monitoring, MFA enforcement,…
2026 Air-Gapped Systems Cybersecurity Risks Explained
May 13, 2026
Article Summary • Who this is for: Manufacturing companies, industrial facilities, OT/SCADA managers, plant operators, and IT leaders responsible for securing air-gapped or isolated operational environments. • The challenge: Many organizations still believe physical isolation is enough to protect critical systems, but modern cyber threats now bypass air gaps through USB devices, insider threats, vendor access, and supply chain compromises. This creates major risks, including ransomware,…
Why Your IT Guy Isn’t Enough for Cybersecurity 2026
May 11, 2026
Article Summary • Who this is for: Small business owners, office managers, and operations leaders relying on a single internal IT person or basic MSP support to manage cybersecurity and IT operations. • The challenge: Traditional IT support is no longer enough to defend against modern cyber threats like ransomware, AI-driven phishing, compliance failures, and cloud security risks. Businesses without 24/7 monitoring, tested backups, and specialized security expertise face major downtime,…
How Hackers Access PLCs and Shut Down Production Lines
May 6, 2026
Article Summary • Who this is for: Manufacturing companies, plant managers, OT/IT leaders, and industrial operations teams that rely on PLCs, SCADA systems, and connected production environments to keep operations running. • The challenge: Cybercriminals are exploiting weak IT-to-OT segmentation, remote access tools, default credentials, and outdated PLC firmware to infiltrate production environments, causing downtime, ransomware incidents, operational disruption, and safety risks. • Key…
The $10K Mistake Small Businesses Make After Cyberattacks
May 4, 2026
Article Summary • Who this is for: Small business owners and operators in service-based or regulated industries, such as accounting, dental, healthcare, legal, finance, and local professional firms, who rely on backups but lack a formal cyber incident response plan. • The challenge: After a cyberattack, panic-driven recovery decisions, especially restoring infected backups, can trigger reinfection, longer downtime, compliance exposure, and $10,000+ in avoidable costs. • Key insights covered:…
2026 Cyber Insurance Requirements Small Business Owners
April 29, 2026
Article Summary • Who this is for: Small to mid-sized business owners, COOs, and IT decision-makers in regulated or data-sensitive industries (finance, healthcare, professional services) seeking cyber insurance approval • The challenge: 73% of SMBs fail cyber insurance assessments due to weak controls, missing documentation, and reactive security, leading to denied coverage, 100–300% premium increases, or full financial exposure to cyber incidents • Key insights covered: Cyber insurers now…
Manufacturing Downtime Cost Per Hour Guide
April 28, 2026
Article Summary • Who this is for: Manufacturing executives, plant managers, and operations leaders responsible for production uptime, efficiency, and profitability in mid-to-large industrial facilities • The challenge: Unplanned downtime is silently draining revenue at $22K–$300K+ per hour, with most companies underestimating true costs due to hidden factors like labor, restart delays, penalties, and IT-related disruptions • Key insights covered: True downtime cost includes production loss,…
Manufacturing IT Budget Planning: Balance Cost & Security
April 22, 2026
Article Summary • Who this is for: Manufacturing executives, plant managers, and CFOs responsible for IT budgeting, operations, and risk management in industrial environments • The challenge: IT is treated as a cost center, leading to underinvestment in cybersecurity, reactive spending, costly downtime (avg. $50K/hour), and exposure to rising OT cyber threats and compliance risks • Key insights covered: Balance IT and OT security with operations by allocating 15–20% of budget to cybersecurity…
Unsupported Systems in Manufacturing: Security Risks
April 14, 2026
Article Summary • Who this is for: Manufacturing owners, plant managers, and operations leaders running production environments with legacy or aging control systems • The challenge: Critical production systems are running on unsupported technology, creating major exposure to cyberattacks, compliance failures, and costly downtime that can exceed $50K+ per hour • Key insights covered: Unsupported systems become high-risk entry points with no security patches, making them prime targets for…
How Proactive IT Support Saves Small Businesses Thousands
April 13, 2026
Article Summary • Who this is for: Small business owners, decision-makers, and growing companies looking to reduce IT issues, control costs, and improve daily operations • The challenge: Reactive “break-fix” IT leads to frequent downtime, unpredictable expenses, and increased security risks that disrupt productivity and strain budgets • Key insights covered: The difference between proactive and reactive IT support, cost-saving benefits of managed services, 24/7 monitoring, preventive…
Cyber Resilience Strategy for Manufacturers 2026
April 9, 2026
Article Summary • Who this is for: Manufacturing leaders, operations managers, and business owners looking to protect production environments from modern cyber threats • The challenge: Traditional cybersecurity focuses only on prevention, while manufacturers face operational risks, legacy systems, and downtime costs that require a resilience-first strategy • Key insights covered: The difference between cybersecurity and cyber resilience, IT/OT security integration, network segmentation,…
FTC Safeguards Rule 2026: Avoid Costly Compliance Mistakes
April 7, 2026
Article Summary • Who this is for: Small business owners in financial-related industries (tax preparers, insurance agencies, auto dealers, mortgage brokers, and investment advisors) who must comply with the FTC Safeguards Rule requirements • The challenge: Many small businesses don’t realize they qualify as “financial institutions” under federal law and lack the documented security programs, encryption, access controls, and monitoring required for compliance • Key insights covered: Who must…
Manufacturing Ransomware Prevention Guide 2026
April 1, 2026
Article Summary • Who this is for: Manufacturing business owners and operations leaders who rely on connected production systems and want to prevent costly downtime caused by cyberattacks • The challenge: Ransomware increasingly targets manufacturing environments where IT and operational technology (OT) systems are connected, allowing attacks to halt production within hours • Key insights covered: Why manufacturers are prime ransomware targets, how attacks spread through factory networks, the…
Remote Work Security for Small Businesses: 2026 Guide
April 1, 2026
Article Summary • Who this is for: Small and mid-sized business owners managing remote or hybrid teams who want to protect operations, data, and productivity from unexpected disruptions • The challenge: Remote work environments introduce new cybersecurity risks, connectivity issues, and operational vulnerabilities that many businesses are unprepared to manage • Key insights covered: Common remote work disruption scenarios, remote workforce security risks, business continuity strategies,…
Managed IT for Manufacturing: Max Uptime in 2026
March 24, 2026
Article Summary • Who this is for: Manufacturing business owners, plant managers, and operations leaders looking to reduce costly production downtime and improve system reliability • The challenge: Unplanned downtime caused by IT failures, cybersecurity risks, aging infrastructure, and lack of 24/7 monitoring continues to disrupt production and increase operational costs • Key insights covered: Causes of manufacturing downtime, IT and OT monitoring strategies, proactive maintenance, industrial…
Cloud Migration ROI Guide for Small Businesses 2026
March 24, 2026
Article Summary • Who this is for: Small to mid-sized business owners and decision-makers looking to modernize IT systems, reduce operational costs, and enable secure remote work through cloud technology • The challenge: Many businesses struggle with aging servers, rising IT maintenance costs, limited scalability, and uncertainty about cloud migration risks, security, and real ROI • Key insights covered: Cloud migration benefits, common risks and how to avoid them, ROI calculations, migration…
Ransomware Protection for Small Businesses: 2026 Guide
March 20, 2026
Article Summary • Who this is for: Small to mid-sized business owners and decision-makers who want to protect their operations from rising ransomware threats without building an in-house cybersecurity team • The challenge: Ransomware attacks are increasingly targeting small businesses that lack advanced security systems, structured backup strategies, and clear incident response plans • Key insights covered: How ransomware attacks start, why SMBs are prime targets, the 3-2-1 backup rule,…
Legacy Software Cybersecurity Risks in Manufacturing
March 20, 2026
Article Summary • Who this is for: Manufacturing business owners, plant managers, and operations leaders relying on legacy systems to run production environments • The challenge: Outdated manufacturing software and unsupported operating systems create serious cybersecurity vulnerabilities, while upgrades feel risky, expensive, and disruptive to production • Key insights covered: How legacy systems expose factories to ransomware attacks, why unsupported software cannot be patched, common…
How to Protect PLCs and HMIs from Cyber Threats | 2026 Guide
March 13, 2026
Article Summary • Who this is for: Manufacturing leaders, plant managers, and industrial engineers responsible for protecting PLCs, HMIs, and operational technology (OT) systems that run production environments • The challenge: Modern manufacturing systems are increasingly connected to IT networks, remote vendors, and cloud platforms, exposing PLCs and HMIs to cyber threats they were never designed to defend against • Key insights covered: How cybercriminals target industrial control systems,…
7 Cybersecurity Mistakes Small Businesses Make (2026 Guide)
March 12, 2026
Article Summary • Who this is for: Small to mid-sized businesses that depend on reliable IT systems and want to reduce cybersecurity risks without managing complex security tools internally • The challenge: Many businesses operate with hidden security gaps such as weak passwords, outdated systems, and reactive IT support that leave them vulnerable to ransomware, data breaches, and costly downtime • Key insights covered: The seven most common cybersecurity mistakes affecting small businesses…
Manufacturing IT Downtime: Production & Revenue Loss
March 5, 2026
Article Summary • Who this is for: Manufacturing leaders, plant managers, and operations executives responsible for maintaining production uptime and operational efficiency • The challenge: Modern production lines rely heavily on interconnected IT systems like ERP, MES, and industrial control networks, meaning even small technology failures can halt operations and cause massive financial losses • Key insights covered: The real cost of manufacturing IT downtime, how production systems depend on…
Managed IT Services vs In-House IT: 2026 Guide
March 4, 2026
Article Summary • Who this is for: Small to mid-sized business owners and decision-makers evaluating whether to hire internal IT staff or partner with a managed IT provider • The challenge: Businesses struggle to balance IT costs, expertise, security, and scalability while ensuring reliable technology support for daily operations • Key insights covered: Real cost comparisons between in-house IT and managed services, expertise limitations of single IT staff, 24/7 security advantages, scalability…
2026 Guide to OT vs IT Security in Manufacturing
February 26, 2026
Article Summary • Who this is for: Manufacturing executives, plant managers, and operations leaders responsible for protecting both production systems and business networks • The challenge: IT and OT systems have different security priorities, but cyberattacks now target both—putting production uptime, safety, and revenue at serious risk • Key insights covered: Core differences between IT and OT security, why traditional IT tools fail in industrial environments, network segmentation best…
IT Downtime Costs Small Business: 2026 Guide & Calculator
February 25, 2026
Article Summary • Who this is for: Small to mid-sized business owners in Metro Atlanta relying on technology for daily operations • The challenge: IT outages are more expensive than most SMBs realize, with hidden productivity, compliance, and reputation costs • Key insights covered: Real hourly downtime costs by industry, hidden financial impacts, common causes of outages, and proactive prevention strategies • Your outcome: A clear understanding of your true downtime exposure — and actionable…
Why Cybercriminals Target Manufacturing Companies First
February 19, 2026
Article Summary • Who this is for: Manufacturing executives, plant managers, and operations leaders responsible for protecting production, intellectual property, and uptime • The challenge: Manufacturers face high downtime costs, IT/OT security gaps, and supply chain vulnerabilities that make them prime targets for ransomware and industrial cyberattacks • Key insights covered: Why factory ransomware is so profitable for attackers, the risks of IT and OT convergence, ICS security weaknesses,…
Small Business Cyberattacks 2026: Why SMBs Are #1 Targets
February 19, 2026
Article Summary • Who this is for: Small to mid-sized business owners who believe they’re “too small to be targeted” but rely heavily on digital systems, email, and customer data • The challenge: Cybercriminals are increasingly targeting SMBs with AI-powered attacks, ransomware, and phishing—while most small businesses lack enterprise-level security, monitoring, and response capabilities • Key insights covered: Why 43% of attacks now target small businesses, how AI and ransomware-as-a-service…
MSP Checklist: Securing Hybrid Remote Workforces
February 13, 2026
Article Summary • Who this is for: Small to mid-sized business owners in Metro Atlanta managing hybrid or remote teams and concerned about cybersecurity risks • The challenge: Hybrid work environments expand your attack surface, exposing business data to unsecured home networks, personal devices, and evolving cyber threats • Key insights covered: How to conduct a full security assessment, implement endpoint protection and VPNs, strengthen identity and access management, establish 24/7…
Hidden Costs of Outdated Technology & Unsupported Software
February 12, 2026
Article Summary • Who this is for: Small to mid-sized business owners in Metro Atlanta relying on aging hardware, legacy systems, or unsupported software to run daily operations • The challenge: Outdated technology quietly drains productivity, increases security risks, drives up maintenance costs, and exposes businesses to compliance violations—often costing far more than a proactive upgrade • Key insights covered: The real financial impact of downtime and inefficiency, cybersecurity risks tied…
SMB Compliance Guide: GDPR, CMMC & Beyond HIPAA/PCI (2026)
February 5, 2026
Article Summary • Who this is for: Small to mid-sized business owners in Metro Atlanta dealing with expanding compliance requirements beyond traditional HIPAA and PCI standards• The challenge: New regulations like GDPR and CMMC are creating complex compliance obligations that many SMBs don't fully understand• Key insights covered: How GDPR affects US businesses, CMMC requirements for defense contractors, state-level privacy laws, and practical compliance strategies• Your outcome: Clear…
NIST, CMMC, ISO Manufacturing IT Compliance Guide 2026
February 5, 2026
Article Summary Why cybersecurity compliance is no longer optional for manufacturers working with government or enterprise clients What NIST, CMMC, and ISO actually mean in plain language—and how each framework impacts your business Why CMMC compliance is mandatory for Department of Defense contracts and defense supply chains How non-compliance leads to lost contracts, regulatory penalties, and costly production downtime The real financial and operational risks of ignoring manufacturing IT…
SMB Technology Trends 2026 Impacting Your Bottom Line
January 29, 2026
Article Summary Why outdated IT strategies quietly drain revenue through downtime, inefficiency, and emergency fixes How AI adoption in 2026 helps SMBs reduce operating costs, improve response times, and boost conversions Why cybersecurity is now a non-negotiable investment as small businesses become prime attack targets How remote and hybrid work technology must evolve to maintain productivity without sacrificing security Why cloud-first and integrated tech stacks outperform traditional IT…
How to Keep CAD Workstations Fast & Secure
January 28, 2026
Article Summary • Why slow and unsecured CAD workstations silently drain productivity, revenue, and project timelines • How proper hardware optimization (CPU, GPU, RAM, and storage) dramatically improves CAD performance • The hidden financial and legal risks of poor CAD software license management • How file corruption happens in shared CAD environments—and how version control and backups prevent data loss • Why CAD workstations are prime cyber targets in 2026 and need layered security beyond…
Manufacturing Downtime Costs: IT Support ROI Guide 2026
January 22, 2026
Article Summary Why PLCs and HMIs represent a growing but often overlooked cybersecurity risk for manufacturers How legacy industrial control systems create vulnerabilities that traditional IT security cannot adequately protect Common attack vectors targeting manufacturing environments and the real-world impact of compromised production systems AlphaCIS’s layered, industry-specific cybersecurity approach is designed to protect manufacturing operations without disrupting uptime…
5 IT Myths Hurting Your Business More Than You Think
January 20, 2026
Article Summary Why small and mid-sized businesses are prime targets for cyberattacks—not “too small to matter” The hidden costs behind cloud solutions that make them more expensive than expected Why antivirus software alone no longer protects against modern cyber threats How DIY IT management often costs more in downtime, lost productivity, and risk The real financial impact of delaying system upgrades and relying on outdated technology Picture this: It's Monday morning, and your…
Manufacturing Cybersecurity: Secure PLCs & HMIs
January 13, 2026
Article Summary Why PLCs and HMIs represent a growing but often overlooked cybersecurity risk for manufacturers How legacy industrial control systems create vulnerabilities that traditional IT security cannot adequately protect Common attack vectors targeting manufacturing environments and the real-world impact of compromised production systems AlphaCIS’s layered, industry-specific cybersecurity approach is designed to protect manufacturing operations without disrupting uptime…
Small Business IT Future Metro Atlanta 2026
January 12, 2026
Article Summary Who this is for: Small business owners in Metro Atlanta planning their IT strategy for 2026 What’s changing: AI-driven IT support, stricter cybersecurity requirements, evolving cloud strategies, and smarter managed IT partnerships Key insights covered: How AI reduces downtime, why cybersecurity compliance is now mandatory, when hybrid cloud makes sense, and what a true managed IT partnership looks like The outcome: A clear roadmap to reduce IT risk, control costs, and…
Colonial Pipeline Cyberattack: Security Lessons 2025
January 6, 2026
Picture this: It's a quiet Friday evening in May 2021, and somewhere in Georgia, a fuel pipeline operator notices something strange on their computer screen. By Saturday morning, the largest fuel pipeline system in the United States had gone completely dark. Gas stations from Texas to New Jersey ran dry. Panic buying ensued. And all because of a single ransomware attack that exposed just how vulnerable our industrial systems really are. Inside the Cyberattack on Colonial Pipeline: What…
Your Employees: Biggest Cyber Risk & Best Defense
January 5, 2026
Picture this: It's Monday morning in your Metro Atlanta office, and your team is settling in with their coffee. Sarah from accounting clicks on what looks like an urgent invoice email. Within minutes, your entire network is locked down by ransomware. Sounds like a nightmare? For many business owners, this scenario is becoming an all-too-common reality. Here's the truth that might surprise you: your employees are your biggest cyber risk and your best defense against the growing tide of cyber…
Manufacturing Cyber Targets: Protect OT-IT Systems 2025
December 29, 2025
Picture this: It's 6 AM on a Tuesday, and the production manager at a major automotive parts manufacturer walks into what should be a bustling factory floor. Instead, they're greeted by silence. Every machine has stopped. Computer screens display the same chilling message: "Your files have been encrypted. Pay $2 million in Bitcoin to restore operations." This isn't science fiction; it's the new reality of why manufacturing plants are the new cyber targets: protecting OT and IT systems before…
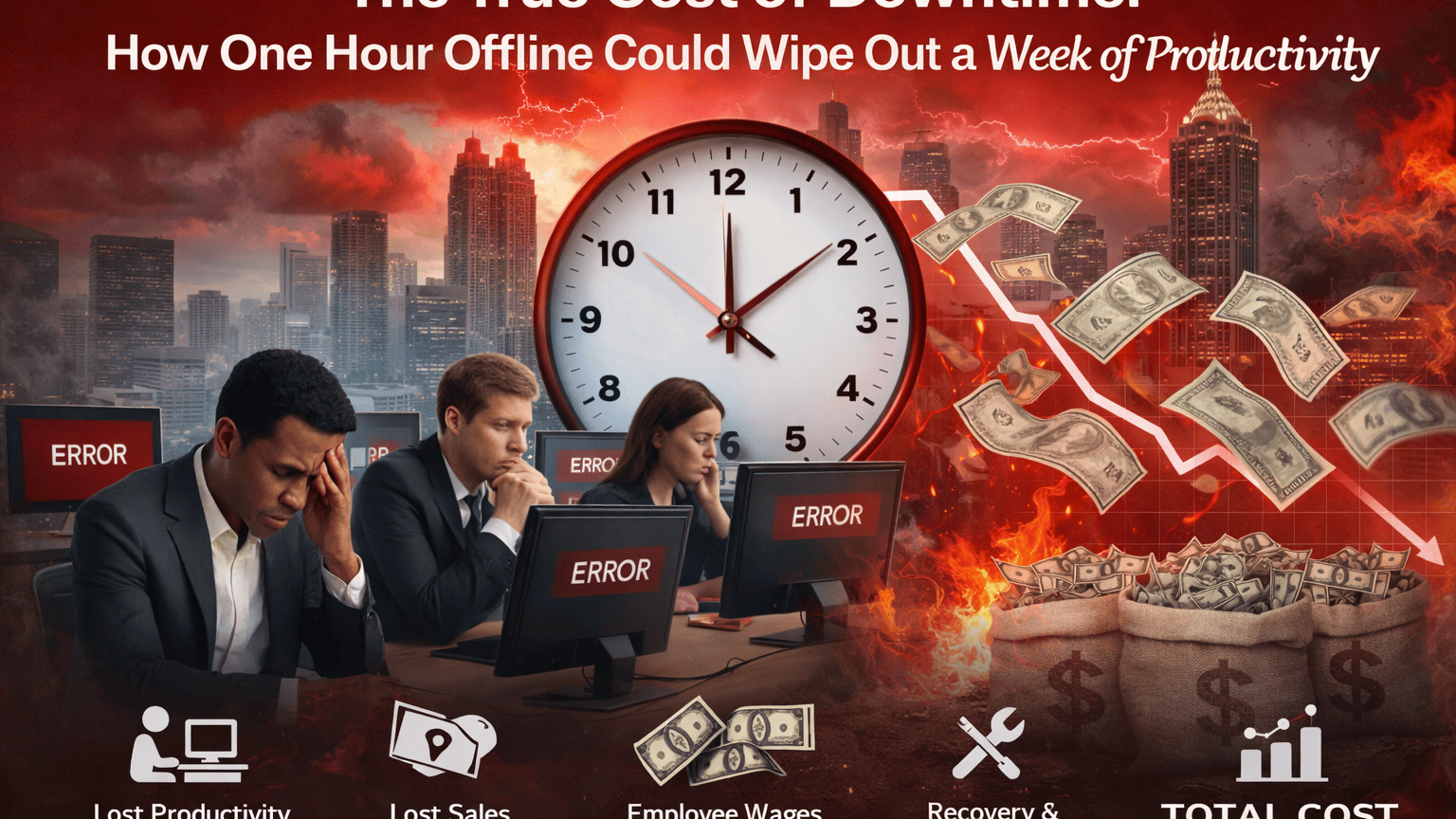
IT Downtime Costs Businesses More Than You Think
December 29, 2025
Picture this: It's 9 AM on a Tuesday in your Metro Atlanta office. Your team is caffeinated, motivated, and ready to tackle the day's biggest client presentation. Then it happens, your internet goes down. What seems like a minor hiccup quickly spirals into a nightmare that costs you not just one deal, but an entire week's worth of progress. The True Cost of Downtime: How One Hour Offline Could Wipe Out a Week of Productivity isn't just a catchy phrase; it's a harsh reality that thousands of…
2026 FTC Safeguards Rule: Metro Atlanta Compliance
December 20, 2025
Picture this: It's January 2026, and you're sitting in your Atlanta office, coffee in hand, when your phone rings. It's your attorney with news that makes your stomach drop – the FTC is investigating your business for non-compliance with the Safeguards Rule. What seemed like a distant deadline suddenly became your biggest nightmare. 2026 is Closer Than You Think: Preparing Your Business for the New FTC Safeguards Rule isn't just a catchy phrase – it's a wake-up call that could save your…
Managed IT vs In-House IT: 2025 Guide for Manufacturers
December 20, 2025
Picture this: You're running a successful medical practice in Buckhead when suddenly you receive a letter about a HIPAA audit. Or maybe you're operating a thriving retail business in Midtown, and your payment processor is demanding PCI compliance documentation. Perhaps you're a government contractor in Marietta, and someone just mentioned something called CMMC that could affect your contracts. Sound familiar? If you're feeling overwhelmed by the alphabet soup of compliance regulations, you're…
HIPAA, PCI & CMMC Compliance Guide for Metro Atlanta SMBs
December 11, 2025
Picture this: It's 3 AM on a Tuesday, and your production line just went down due to a network failure. Your lone IT guy is on vacation, and you're staring at thousands of dollars in lost revenue every hour. Sound familiar? This scenario plays out more often than you'd think for Metro Atlanta manufacturing companies, and it perfectly illustrates why the question of "Managed IT vs. In-House IT: What Works Best for Metro Atlanta Manufacturing Companies?" keeps executives up at night. As someone…
Why Cybercriminals Love Manufacturers: How to Stay Protected
December 3, 2025
Picture this: It's 3 AM on a Tuesday, and the production manager at a mid-sized automotive parts manufacturer gets a call that will haunt him for months. Their entire production line is down. Not because of a mechanical failure or supply chain issue, but because cybercriminals have encrypted every critical system and are demanding $2.3 million in Bitcoin. This isn't fiction; it's happening to manufacturers across the globe every single day. Why cybercriminals love manufacturers (and what you…
Facebook Cyberattacks Target Atlanta Businesses
December 3, 2025
Picture this: It's a Tuesday morning in Buckhead, and Sarah, the owner of a thriving marketing agency, receives a Facebook message from what appears to be a longtime client. The message seems urgent; they need to update their payment information immediately for an upcoming project. Within 20 minutes, Sarah's business bank account is compromised, and $50,000 disappears. Your Next Cyberattack Could Start on Facebook: The Rise of Social Engineering Scams in Atlanta isn't just a headline; it's the…
The Accidental IT Manager: Metro Atlanta Business Guide 2025
November 26, 2025
It’s 8:47 AM on a Tuesday in Buckhead. Sarah, your trusted office administrator of three years, is frantically Googling “why won’t the server connect to the internet” while answering calls from frustrated employees who can’t access their email. Sound familiar? The Accidental IT Manager: What Happens When Your Office Admin Becomes Your Tech Department is a scenario unfolding in countless Metro Atlanta businesses right now, and the consequences are more serious than many owners realize. What…
Manufacturing CFO Guide: Managed IT ROI & Cost Control 2025
November 26, 2025
Picture this: It's 3 AM, and your production line just went down. The ERP system crashed, taking your entire manufacturing operation offline. Every minute costs thousands of dollars in lost production, and your internal IT team is scrambling to find a solution. Meanwhile, your CFO is calculating the mounting losses and wondering if there's a better way to manage technology costs while preventing these disasters. This scenario plays out in manufacturing facilities across the globe, pushing smart…
Why Manufacturers Need Manufacturing Tech Partners Over MSPs
November 13, 2025
Picture this: It's 3 AM, and your production line just went down. Your current MSP's response? "We'll have someone look at it during business hours." Meanwhile, every minute of downtime costs you thousands of dollars and potentially damages relationships with key customers. This scenario plays out in manufacturing facilities across the country every day, and it's exactly why traditional managed service providers (MSPs) often fall short in the manufacturing sector. The truth is, manufacturing…
Why Good Employees Click Bad Links: Cybersecurity Psychology
November 11, 2025
Picture this: Sarah, your most trusted accountant, arrives at the office Monday morning with her usual coffee and determination to tackle the week ahead. She's been with your Atlanta-based company for eight years, never missed a deadline, and has a spotless record. At 9:47 AM, she receives what appears to be an urgent email from "IT Support" requesting that she verify her login credentials due to a security update. Without hesitation, she clicks the link and enters her information. Within…
The Hidden Gaps in Your Cybersecurity Plan
November 1, 2025
In the world of cybersecurity, confidence can be a trap. Too many businesses believe that because they haven’t yet experienced a breach, they must be doing something right. Firewalls are in place, antivirus is running, backups are automated, what could go wrong, right? But here’s the reality: in 2025, cyber threats aren’t breaking in through the front door anymore. They’re walking straight through the gaps created by complacency, outdated systems, and untested defenses. The illusion of…
Unsupported Software Risks in Atlanta Manufacturing
October 30, 2025
Across Atlanta’s manufacturing plants, millions of dollars in revenue depend on machines powered by outdated software. Many of these systems have not received a security update in years, quietly becoming hackers’ favorite entry points. It’s a growing issue. Unsupported software is now one of the top causes of industrial cyber incidents in the Southeast. Companies pour resources into physical security and employee awareness, yet overlook the outdated systems running the very equipment that keeps…
Industrial IoT Without IT Oversight: Prevention Guide 2025
October 20, 2025
Picture this: It's 3 AM on a Tuesday, and your entire production line has ground to a halt. The smart sensors you installed six months ago to boost efficiency are now completely offline, and nobody knows why. Your IT team is scrambling to figure out what went wrong, but here's the kicker they weren't involved in the IoT deployment from the start. Sound familiar? If you're a manufacturing leader who's been tempted to fast-track IoT implementation without proper IT oversight, you're not alone.…
IT Budgeting 2025: Atlanta Small Business Cost-Cutting Guide
October 20, 2025
Picture this: It's Monday morning, and you're staring at your company's IT expenses from last month. The number makes your coffee taste bitter. Between software licenses, hardware repairs, and that emergency server fix that costs more than your car payment, you're wondering if there's a better way to manage your technology budget without sacrificing the tools your team needs to succeed. You're not alone. I've worked with dozens of Atlanta small businesses over the past decade, and the story is…
IT Compliance for Metro Atlanta SMBs Made Simple
October 15, 2025
Picture this: You're sitting in your Buckhead office at 9 PM, staring at a stack of compliance documents that might as well be written in ancient Greek. Your healthcare practice just landed a major contract, but the client wants proof of HIPAA compliance. Your manufacturing company is eyeing a government contract, but CMMC requirements seem impossible to navigate. Sound familiar? If you're a Metro Atlanta business owner, you're not alone in feeling overwhelmed by IT compliance requirements.…
Modern Manufacturing Runs on Information
October 12, 2025
Picture this: It's 3 AM at a major automotive plant, and an assembly line suddenly stops. In the old days, this would mean hours of downtime, frantic phone calls, and massive losses. But today? The plant's information systems had already predicted this failure three days ago. Maintenance was scheduled, parts were ordered, and the "breakdown" became a planned 15-minute swap that actually improves overall efficiency. This isn't science fiction, it's the reality of modern manufacturing in 2025.…
Downtime Silent Tax: Calculate Your True Business Costs 2025
September 27, 2025
Picture this: It's Monday morning, and you walk into your office with your coffee in hand, ready to tackle the week ahead. But instead of the usual hum of productivity, you're greeted by frustrated employees staring at blank screens, phones ringing off the hook with angry customers, and that sinking feeling in your stomach as you realize your systems are down. Again. If this scenario sounds familiar, you're not alone. Downtime is like a silent tax that most small businesses pay without even…
When Your IT Lags, Your Assembly Line Does Too
September 20, 2025
Picture this: It's 2:30 AM on a Tuesday, and your production floor supervisor is frantically calling you. The entire assembly line has ground to a halt because the manufacturing execution system (MES) crashed. Workers are standing idle, machines are silent, and every minute of downtime is costing your company thousands of dollars. Sound familiar? If you're in manufacturing, you've probably lived this nightmare more than once. In today's hyper-connected industrial landscape, your IT…
How One Weak Password Can Halt a Production Line
September 12, 2025
Picture this: It's 3:47 AM on a Tuesday. Your manufacturing plant should be humming along at peak efficiency, cranking out products to meet this week's delivery deadlines. Instead, every machine sits silent. Your production control systems are locked down. A ransom demand flashes across every computer screen. The culprit? An employee's password was "Password123", and now your entire operation is vulnerable to cybercriminals. This isn't science fiction. It's the harsh reality facing…
Most Manufacturers’ Bottleneck Isn’t Machines, It’s IT
September 5, 2025
Picture this: You walk into a state-of-the-art manufacturing facility. Gleaming machines hum with precision, robotic arms dance in perfect choreography, and production lines move with clockwork efficiency. Yet somehow, orders are delayed, inventory is mismanaged, and productivity targets remain frustratingly out of reach. Sound familiar? You're not alone. If this scenario sounds familiar, you're not alone. Manufacturing companies today face an unprecedented digital transformation challenge;…
Top 5 IT Challenges Manufacturers Face (How to Solve Them)
August 29, 2025
Picture this: It's 3 AM, and your production line grinds to a halt because your aging ERP system just crashed. Again. Your plant manager is frantically calling the IT team, but they're already dealing with a cybersecurity incident that started two hours ago. Meanwhile, your competitors are racing ahead with smart factories and AI-powered operations while you're still struggling to get basic systems to talk to each other. If this scenario sounds familiar, you're not alone. Manufacturing…
What Is EDR? Endpoint Detection Response Guide 2025
August 21, 2025
You walk into the office like any other morning, coffee in hand, ready to start the day. A couple of your employees are already there, but something’s off. One of them says their computer isn’t working. Another says the same. You walk over to take a look. On the screen is a black background with a red message:“Your files have been encrypted. You have 72 hours to pay or your data will be lost forever.” You check a few more computers. It’s not just one. It’s all of them. Your accounting system is…
IT Compliance Made Simple: A Small Business Guide
August 6, 2025
IT Compliance Doesn't Have to Be Scary: A Small Business Guide Picture this: It's 2 AM, and you're lying awake, wondering if your small business is one data breach away from disaster. You've heard horror stories about compliance violations that cost companies thousands in fines, but every time you try to research IT compliance, you're met with a wall of technical jargon that makes your head spin. Sound familiar? You're not alone. I've worked with hundreds of small business owners who thought IT…
The Real Reason Your Employees Click on Phishing Emails
August 5, 2025
The Real Reason Your Employees Click on Phishing Emails (and How to Stop It) Picture this: Your most trusted employee, Sarah from accounting, just clicked on what looked like an urgent email from the CEO. Within minutes, your company's financial data is compromised, and you're staring at a potential $4.45 million loss, the average cost of a data breach in 2024. If you think this scenario is far-fetched, think again. 95% of successful cyberattacks start with a phishing email, and it's not just…
5 Reasons to Outsource IT Support Beyond Cost Savings
July 30, 2025
5 Reasons to Outsource Your IT Support in 2025 Picture this: It's 3 AM on a Tuesday, and your server crashes. Your entire team can't access critical files, emails are down, and you have a major client presentation in five hours. Sound familiar? If you're a business owner in Metro Atlanta, you've probably faced this nightmare scenario or something equally frustrating. Perhaps it was the time your "IT guy" went on vacation just when your payment system decided to take a break, too. Or maybe it…
What the FTC Safeguards Rule Means for Small Businesses
July 23, 2025
What the FTC Safeguards Rule Means for Your Business This Year (and Why Ignoring It Could Cost You More Than Just Fines) "Wait, the FTC can fine me now?" If your business collects or stores customer financial info, even something as simple as a Social Security number or a credit application, you could be on the hook for more than you think in 2025. And no, this isn’t just a big bank or Fortune 500 issue anymore. Thanks to the updated FTC Safeguards Rule, a surprising number of small businesses…
Why Cyber Insurance Claims Are Getting Denied in 2025
July 15, 2025
Why Cyber Insurance Providers Are Denying Claims in 2025 and How to Avoid It So, you got cyber insurance. You even paid a little extra for the “better” policy. Now you can sleep at night, right? Not so fast. In 2025, more small businesses in Metro Atlanta are learning the hard way that having cyber insurance doesn’t guarantee a payout. Claim denials are rising sharply, and most business owners don’t realize what’s missing until after the breach happens. Let’s break down what’s changing, why…
Ransomware Is Targeting Atlanta SMBs in 2025
July 8, 2025
The New Ransomware Reality: How Small Businesses in Atlanta Are Becoming Prime Targets It used to be that ransomware attacks were something you only heard about in the news. Big hospitals. Fortune 500s. Some company in Europe you’ve never heard of. But not anymore. In 2025, ransomware has gone local. And small businesses in Metro Atlanta are smack in the bullseye. Wait, Why Us? Great question. Here’s the thing: Cybercriminals have figured out that small and mid-sized businesses (SMBs) often…
Why Antivirus Isn’t Enough for SMBs in 2025
July 1, 2025
Why Antivirus Isn’t Enough in 2025: The Layers of Cybersecurity Metro Atlanta SMBs Need A few years ago, installing antivirus software seemed sufficient. You'd buy a license, let it scan your systems for viruses, and call it a day. But today’s threats don’t play by yesterday’s rules, and for Metro Atlanta's small and mid-sized businesses (SMBs), relying on antivirus alone is like locking your front door but leaving the windows wide open. The Evolving Threat Landscape Cybercriminals aren’t just…
Georgia’s 2025 Data Laws Every SMB Must Know
June 23, 2025
How Local Regulations Are Changing the Way You Manage Data What Metro Atlanta SMBs in Healthcare, Finance, and Government Contracting Need to Know in 2025 In today’s digital world, data is more than just information; it’s currency. However, with rising cybersecurity risks and an increasing number of regulations, small and mid-sized businesses (SMBs) in Metro Atlanta are under pressure to reassess how they manage, store, and protect their data. Whether you run a local clinic, an accounting firm,…
Top 7 IT Mistakes SMBs Make During Growth Spurts
June 17, 2025
Top 7 IT Mistakes Small Businesses Make During Growth Spurts (and How to Avoid Them) Rapid growth is every small business owner’s dream but without the right IT foundation, that dream can quickly become a costly nightmare. As your business scales, your technology must scale with it. Unfortunately, many small to mid-sized businesses in Metro Atlanta make the same IT missteps during these exciting transitions. Here are the top seven mistakes growing businesses make, and more importantly, how you…
Why Metro Atlanta SMBs Are Migrating to the Cloud
June 10, 2025
Cloud Migration Isn’t Just for Big Corporations: Why Metro Atlanta SMBs Are Making the Switch When people hear "cloud migration," they often think of massive corporations with unlimited IT budgets. But across Metro Atlanta, small and mid-sized businesses (SMBs) are increasingly moving to the cloud. They're doing it not just to keep up but to stay ahead. The Myth: Cloud Migration Is Only for Big Companies Many business owners still believe cloud services are expensive, complex, and designed only…
Is Your Business Ready to Go Remote Tomorrow?
June 3, 2025
What If Your Entire Office Had to Go Remote… Tomorrow? Why Metro Atlanta SMBs Need a Remote Work Readiness Plan Before the Next Emergency Hits On a typical Monday morning, a power outage swept through parts of Metro Atlanta. No warning, no ETA on restoration. At a small marketing agency in Peachtree Corners, the team found themselves unable to access files, respond to client emails, or even make calls. By noon, the owner made the call: “Everyone works from home.” The scramble began because…
Metro Atlanta SMBs: New Top Target for Cyberattacks
May 27, 2025
Budget Smarter, Not Harder: How Metro Atlanta SMBs Can Cut IT Costs Without Cutting Corners On a warm morning in Decatur, Carla, the owner of a local bakery, unlocked her storefront and opened her laptop to check orders. Instead of customer emails and supplier invoices, she was met with a blinking message: “Your files have been encrypted. Pay $4,000 in Bitcoin to restore access.” Her heart sank. What began as a typical Friday spiraled into chaos. A ransomware attack had paralyzed Carla’s…
Cybersecurity Myths Every Business Must Avoid
May 20, 2025
5 Cybersecurity Myths That Could Put Your Metro Atlanta Business at Risk Picture this: A small business owner in Roswell, Georgia, locks up his shop one evening, confident that his company is "too small" to attract any serious cybercriminal attention. Yet the next morning, his systems are locked, client information is compromised, and he is staring down a five-figure ransom demand. The belief that cybersecurity threats only target "the big guys" is not only outdated; it is dangerous. In Metro…
New IT Compliance Updates for 2025 in Georgia
May 13, 2025
New Compliance Requirements in Georgia: What Metro Atlanta Businesses Need to Know for 2025 As we move through 2025, Metro Atlanta businesses are facing a wave of new compliance requirements that demand attention. From federal mandates to updates in state-level regulations, staying ahead is critical not only for avoiding fines but also for protecting your business reputation. Let's walk through the key changes and what you need to do to stay compliant. Corporate Transparency Act (CTA)…
Cyber Insurance: 2025 Changes Metro Atlanta Must Know
April 30, 2025
Cyber Insurance: 2025 Changes Metro Atlanta Must Know In the heart of Metro Atlanta, a midsized marketing firm in Decatur thought they were prepared for anything. They had invested in cybersecurity insurance years ago, paying premiums without fail. But when a sophisticated phishing scam led to a major data breach in February 2025, their insurance claim was shockingly denied. The reason? Their cybersecurity practices had not kept pace with evolving policy requirements. They missed a crucial…
The Rise in Cyber Attacks in Metro Atlanta
April 22, 2025
Cyber Attacks Are Surging Is Your Metro Atlanta Business Prepared? Do you feel like you're constantly hearing about another company falling victim to a cyber attack? You're not imagining things. Cyber crime is no longer a distant concern it’s happening right here in Metro Atlanta and affecting businesses just like yours. From data breaches that expose sensitive client information to ransomware attacks that freeze your operations until a hefty payment is made, cyber threats have become the…
What Hackers Hope You Never Discover About Your IT Systems
April 7, 2025
What Hackers Hope You Never Discover About Your IT Systems Would You Leave Your Front Door Unlocked During a Crime Spree? Then Why Leave Your Business Vulnerable Online? Imagine watching the evening news and hearing that burglars are targeting homes right in your neighborhood. Would you go to bed with your front door wide open? Of course not. But many businesses are doing exactly that with their digital infrastructure—leaving vulnerabilities unaddressed, hoping they won’t become the next…
Phishing Attacks Tripled Last Year- Here’s What You’re Missing
April 1, 2025
Phishing Attacks Tripled Last Year- Here’s What You’re Missing Have you ever wondered how many phishing attempts your employees face every day? It’s probably more than you think. In fact, recent cybersecurity reports show that the number of employees clicking on phishing links TRIPLED over the last year. That’s a massive jump—and it’s costing businesses more than just a few headaches. From financial losses to data breaches and damaged reputations, phishing is one of the most dangerous threats…
Prompt Your Computer To Do Your Work – Copilot Wave 2
March 17, 2025
Maximizing Your Business Efficiency with Copilot Wave 2 Artificial intelligence (AI) is no longer a futuristic concept—it’s already reshaping the way businesses operate. One of the standout AI tools leading this transformation is Microsoft Copilot, a smart assistant integrated into Microsoft 365 applications. With the latest advancements in Copilot’s Wave 2 update, businesses now have access to enhanced features designed to increase productivity, improve collaboration, and make data-driven…
Here is What To Consider When Returning Back To Office
March 6, 2025
Is Your Business Ready for a Return to Office? Here’s What You Need to Consider The way we work has evolved dramatically over the past few years, hasn’t it? The global pandemic didn’t just introduce remote work—it accelerated a shift in workplace culture that many businesses were already contemplating. Now, as we move forward, companies are divided: Should they bring employees back to the office full-time, embrace hybrid models, or continue supporting remote work? For some businesses, returning…
Can Your Backups Survive a Modern Cyberattack?
February 27, 2025
Can Your Backups Survive a Modern Cyberattack? Picture this: Your company is humming along smoothly when, out of nowhere, everything screeches to a halt. Your critical files—customer records, financial data, project plans—are locked tight, held hostage by cybercriminals. They’re demanding a hefty ransom, payable in untraceable cryptocurrency, just to give you a slim chance of getting your data back. Even if you cough up the cash, there’s no promise they’ll deliver. Your business is paralyzed,…
Hackers’ Latest Trick: How Corrupted Files Bypass Security
February 18, 2025
Hackers’ Latest Trick: How Corrupted Files Bypass Security You’re scanning your inbox, and you spot an important email with a Word document attached. Maybe it’s an invoice from a vendor, a request from a colleague, or an update from a supplier. It looks legitimate, so you open it without a second thought… And just like that, you’ve fallen into a cybercriminal’s trap. This scenario is exactly what hackers are hoping for, and they’re using increasingly sophisticated tactics to bypass even the…
One Huge Mistake Your Employees Are Making…
February 11, 2025
One Mistake Your Employees Are Making That Could Cost You Everything Let me ask you something: Do you lock your front door when you leave home? Of course, you do. But what if you came back to find a window left wide open? Suddenly, that locked door doesn’t mean much, does it? Now, think about your business. You’ve likely invested in cybersecurity—strong passwords, firewalls, and the latest software updates. But what if your employees are unknowingly leaving digital “windows” open? It’s not…
Is Your Business Technology Ready for the Future?
January 17, 2025
Is Your Business Technology Ready for the Future? How do you feel about the technology you use in your business? Confident? A recent study revealed that 90% of business leaders believe their IT systems are "best in class" today. But here’s the catch: what about tomorrow? The same study uncovered some alarming insights about the state of business IT: Only 39% of business leaders feel their current IT systems are truly future-ready. 64% worry that their technology is becoming outdated.…
New Malware “annoys” you into handing over your credentials
November 5, 2024
New Malware "annoys" you into handing over your credentials You and your team might already be familiar with basic online security—watching out for phishing scams, avoiding suspicious downloads, and never clicking on strange links. But here’s the twist: as fast as we catch on to these threats, cybercriminals evolve even faster. Their latest tactic is sneaky, stealthy, and designed to manipulate you into giving up your Google login details without a second thought. Let’s talk about…
The Hidden Backup Disaster No One’s Talking About!
October 21, 2024
The Hidden Backup Disaster No One’s Talking About! Losing access to your business’s data – even temporarily – can feel like a nightmare straight out of a horror movie. In today's fast-paced business world, downtime and data loss can cripple operations, damage customer trust, and cause significant financial losses. Fortunately, data backup tools exist to create copies of your critical information and store them securely. Should anything go wrong, these backups can be used to restore your files…
Protect Your Atlanta Construction Business from Cyber Attack
September 18, 2024
Attention Atlanta Construction Business Owners: Hackers Are Targeting Your Accounting Systems—Here’s How to Protect Your Business Cybercriminals are increasingly targeting the Foundation accounting software used by many construction companies, including those in Atlanta, to infiltrate business networks through weak passwords and exposed servers. If your business relies on Foundation for managing accounting, payroll, or job costing, it’s critical to act now to protect your data. What’s…
One Simple Step That Could Prevent a Devastating Data Breach
September 10, 2024
One Simple Step That Could Prevent a Devastating Data Breach Microsoft has recently announced a significant change in their security protocols—soon, all Azure sign-ins will require multi-factor authentication (MFA) to enhance user protection. While this update specifically affects users of Microsoft Azure, their cloud computing platform, it's a signal that all businesses, whether they use Azure or not, should take note. Why? Because MFA is one of the most straightforward and highly effective…
Edge’s AI Copilot: Write Better, Faster
August 26, 2024
Edge’s AI Copilot: Write Better, Faster Microsoft is introducing an innovative feature in its Edge browser that’s bound to revolutionize the way you and your employees handle day-to-day tasks. Enter ‘Draft with Copilot,’ a cutting-edge AI-powered tool that can generate text on any topic with just a few clicks, saving you time and streamlining your workflow. Imagine you’re working on a complex report and need to draft a summary. Instead of wrestling with writer’s block, you can use ‘Draft with…
Last Call: Upgrade Windows 11 by October 8th!
August 16, 2024
Last Call: Upgrade Windows 11 by October 8th! If you’re currently using Windows 11, it's crucial to be aware of an upcoming deadline set by Microsoft. The tech giant has announced that all users must upgrade to Windows 11 version 23H2 by October 8th, 2024. After this date, older versions of Windows 11 will no longer receive essential security updates, putting your systems—and potentially your entire business—at significant risk. Why Is This Update So Important? This deadline isn't just…
Beware: Malware Lurking in Chrome Extensions!
July 19, 2024
Beware: Malware Lurking in Chrome Extensions! Google Chrome is a popular choice for businesses due to its extensive range of extensions that enhance productivity and browsing experience. From blocking ads to managing tasks, Chrome extensions are essential tools. However, their widespread use also presents significant risks. The Hidden Dangers of Extensions Chrome extensions can be incredibly beneficial, but they also pose potential threats. Just like downloading apps on your phone, adding…
How To Guide: Get Employees to Report Cyber Issues
June 25, 2024
How To Guide: Get Employees to Report Cyber Issues Getting your team to report security issues quickly is something that’s important for your business… but maybe something that might not have crossed your mind before. You might think that with so many security tech tools, you're covered. But guess what? Your employees are your first line of defense, and they’re irreplaceable when it comes to spotting and reporting security threats. Imagine this: One of your employees receives a…
CDK Global Hack: How to migrate to another DMS
June 22, 2024
Navigating DMS Migration: A Smooth Transition from CDK Global In the wake of the recent cybersecurity breach at CDK Global, many dealerships are reassessing their reliance on this Dealer Management System (DMS). The incident has underscored the importance of robust data security and operational reliability. Transitioning to a new DMS can safeguard your dealership from future disruptions. At AlphaCIS, we specialize in guiding dealerships through seamless DMS migrations. Here’s an in-depth guide…
Team Copilot: Your New AI Partner for Better Teamwork
June 14, 2024
Team Copilot: Your New AI Partner for Better Teamwork Ever wish your team had a smart assistant to keep everything on track? Meet Team Copilot, the newest AI-powered tool from Microsoft that’s about to change the way your team works together. Scheduled for release later this year, it’s part of Microsoft’s growing suite of AI tools designed to boost productivity, but this time with a focus on teamwork. What Is Team Copilot? Think of Team Copilot as your team’s digital collaborator. If you’re…
Secure Your Small Business with Biometrics and Passkeys
June 5, 2024
Secure Your Small Business with Biometrics and Passkeys In today's digital age, safeguarding our data, whether it's business secrets or personal information, is paramount. Traditionally, passwords have been the primary method of securing sensitive information. Are Passwords Still Effective? Recent reports reveal that despite the increasing awareness of data privacy and security, many people continue to rely on passwords, with only a small percentage adopting biometrics like…
Atlanta Accountants: Secure Client Data with FTC Rules!
May 23, 2024
Understanding the FTC Safeguards Rule and Its Impact on Accounting Firms in Metro Atlanta In the bustling business environment of Metro Atlanta, accounting firms face unique challenges in protecting customer data. To help address these challenges, the Federal Trade Commission (FTC) introduced the Safeguards Rule in 2003. This rule provides a robust framework for financial institutions, including accounting firms, to secure customer information. Here’s what accounting firms in Metro Atlanta need…
Why Atlanta Businesses Choose Microsoft 365 Over G-Workspace
May 19, 2024
Why Atlanta Businesses Choose Microsoft 365 Over G-Workspace No matter what your business does, a portion of your workforce needs a productivity and collaboration suite to get work done. This essential set of tools, once known as an office suite (with Microsoft Office dominating the market), has significantly evolved over the past decade. Cloud services have steadily taken over, and businesses have increasingly demanded more collaborative capabilities. Google Suite emerged and eventually…
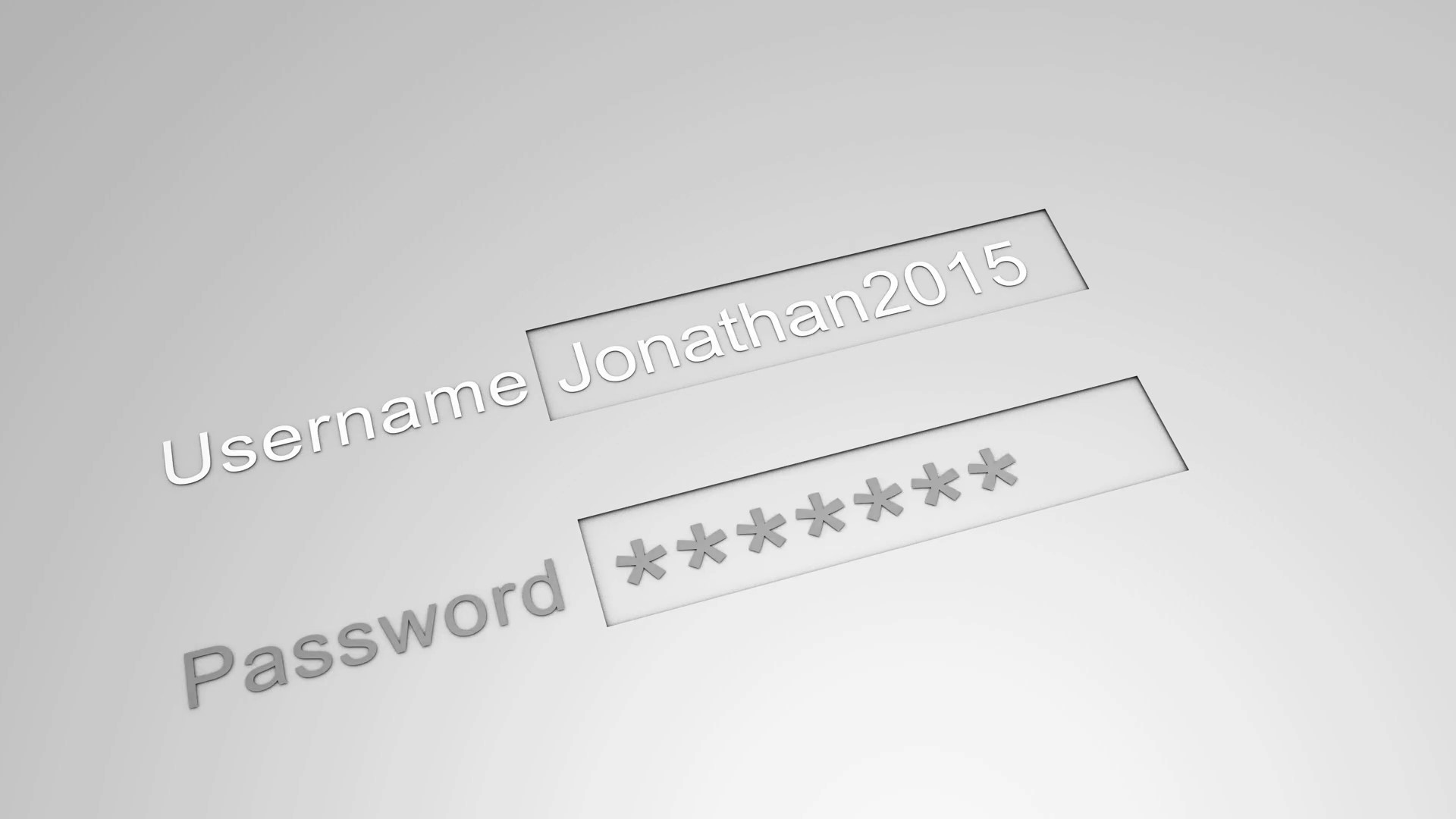
Tired of Password Overload? Discover the Ultimate Hack!
May 13, 2024
Tired of Password Overload? Discover the Ultimate Hack! Feeling like you’re in a never-ending circus act trying to manage all your passwords? You’re definitely not alone. Recent reports show that about 1 in 4 of us are in the same boat, struggling with the sheer number of passwords we need to keep track of. But it’s not just the quantity that’s a problem—it’s also the security risks that come along with it. Let’s be real, most of us aren’t cyber security wizards. We often end up with weak,…
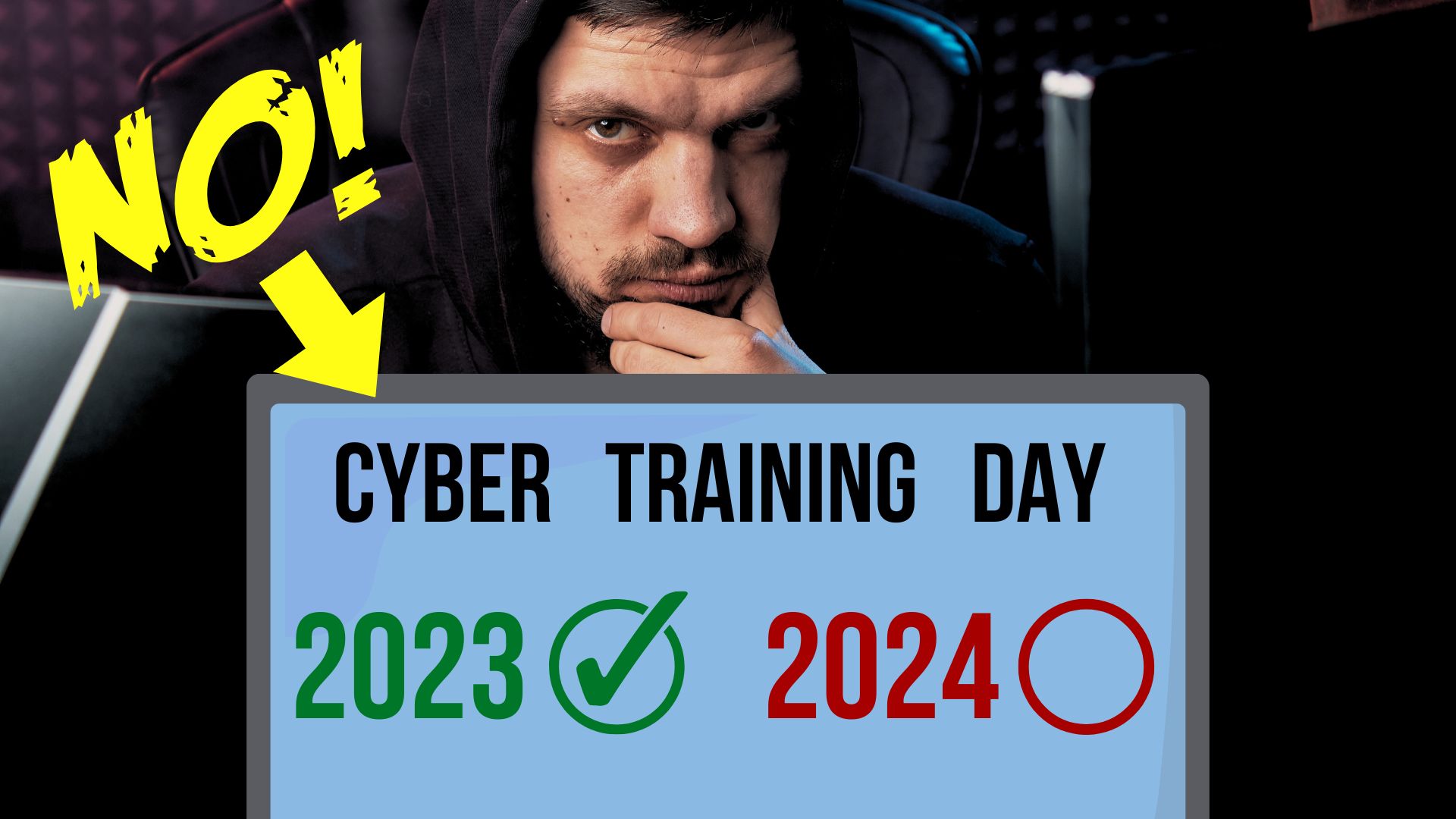
Why Atlanta Businesses Need More Than Annual Cybersecurity Training
May 7, 2024
Why Atlanta Businesses Need More Than Annual Cybersecurity Training Hey Atlanta! With our city fast becoming a bustling tech hub, it's more important than ever to ensure our local businesses are up to speed on cyber threats. As cyber attacks continue to rise nationally, Atlanta companies need to be proactive in safeguarding their data. But here’s the catch: the standard once-a-year cybersecurity training isn’t quite cutting it. Traditionally, these annual trainings have been marked on the…
Newest Copilot: A Game-Changer for MSFT Teams Productivity
April 25, 2024
If you're interested in streamlining your team's productivity, Microsoft Teams' latest updates to Copilot might catch your attention. During a bustling Teams meeting, capturing every idea can be a challenge, even for the quickest note-taker. Copilot addresses this by transcribing conversations and analyzing live chats to highlight key points, ensuring nothing important slips through the cracks. The new features extend beyond just note-taking. Copilot now allows users to retract a sent chat…
Atlanta Businesses: The Risk of Malware is on the Rise!
April 19, 2024
Attention Metro Atlanta Businesses: The Risk of Malware is on the Rise! Let's dive into an urgent and crucial topic for today's business landscape: Malware threats. It's not the best news, but it's essential to be informed. Malware attacks are increasingly targeting small and medium-sized businesses (SMBs) in our area, and the consequences can be severe. This means it's more important than ever to understand how to protect your enterprise. So, what is malware? Imagine malware as the digital…
Supercharge Productivity with These Microsoft Edge Hacks
April 14, 2024
Supercharge Your Productivity with These Microsoft Edge Hacks As a busy business owner or manager, you're always on the lookout for ways to streamline your workflow and get more done. While your web browser may seem like just a tool for accessing the internet, Microsoft Edge on Windows 11 is packed with features that can truly supercharge your productivity. Let me share five of my favorite Microsoft Edge tricks that will have you working smarter, not harder. Split Screen for…
These 4 methods will save thousands in case of a data breach
April 16, 2023
These 4 methods will save thousands in case of a data breach! No business wants to experience a data breach - it's like a digital nightmare come to life. Unfortunately, with today's cyber landscape, it's increasingly difficult to avoid them altogether. In fact, according to IBM Security's 2022 Cost of a Data Breach Report, a staggering 83% of organizations have suffered more than one data breach. Data breaches can hurt a business in many ways - from the immediate cost of remediation to lost…
Healthcare & Dental
March 20, 2023
ACIS can manage your complete IT environment from network, endpoint EHR systems and security. We help transition EHR systems and provide security to ensure your practice is HIPAA compliant and your patient data is protected
Dealerships & Automotive
March 20, 2023
Our support for dealerships include working with multiple Dealer Management Software (DMS) vendors, offering fast response times to problems in an industry literarily where time equals money. Our goal is to ensure sales and finance people never miss a beat
Manufacturing & Engineering
March 20, 2023
ACIS has been addressing the technical needs of manufacturing and engineering companies across many different sectors. Our expertise in this field is unrivaled and we have earned a strong reputation as a leader in providing quality support services.
Accounting & CPA
March 20, 2023
We understand the business and cyclical pattern Accounting and CPA firms face such as during tax season and quarterly return times. We make sure to offer 24-7 help desk support to our Accounting/CPA clients during this time
Change this right away in your org: LastPass breach lessons
March 3, 2023
Change this right away in your org: LastPass breach lessons LastPass had a major breach where thousands of accounts had their information exposed Spear phishing was involved Engineer who had encryption keys had his computer compromised Using a keylogger hackers gained access to LastPass AWS servers Below are steps that you can take to prevent this from happening in your business Let's take a lesson from LastPass. If you have not heard yet, there was a major breach last year where encrypted…
These easy steps will secure your mobile devices
February 24, 2023
These easy steps will secure your mobile devices Cybersecurity experts revealed a shocking statistic recently. Malware attacks had amplified by an astonishing 500% during the opening months of 2022. This is particularly concerning considering many people still haven't taken any steps to safeguard their smartphones. For years now, the power of mobile phones has grown exponentially, to the point where they can do many of the same things as a computer. Despite this fact, people have been known to…
Protecting Your Business: Simple Guide to Endpoint Security
January 27, 2023
Summary Companies of all sizes have a variety of endpoints, such as computers, mobile devices and servers. Endpoint security is necessary to protect against malicious attacks from hackers. 64% of organizations have experienced one or more compromising endpoint attacks. Solutions for addressing password vulnerabilities include training employees, MFA and biometrics Stop malware infection before OS boot Regularly update endpoint security software and firmware Use modern device…
Easy cybersecurity guide: increase security, lower overhead
January 20, 2023
Answering these cybersecurity questions correctly will lower your insurance rate and make your business more secure Do you have a formal Cybersec policy for all employees and is it enforced? Is multifactor authentication enforced companywide? Do you have a formal Disaster Recovery Plan? Who has elevated permission or Administrator access to the system? How are passwords safeguarded? Are you running a company-wide advanced threat detection and protection, and can you prove…
Easy way you can prep your business technology (IT) for 2023
January 4, 2023
Easy way you can prep your business technology (IT) for 2023

This process will protect your business from ex-employees
December 9, 2022
This process will protect your business from ex-employees Every employee in the modern workplace creates a digital footprint. This starts as soon as they're hired, with a company email address and application logins. They may even update their LinkedIn page to show their connection to your company. When an employee leaves a company, it's important to go through a process of, "decoupling" them from the company's technology assets. This digital offboarding is vital to cybersecurity. To avoid…
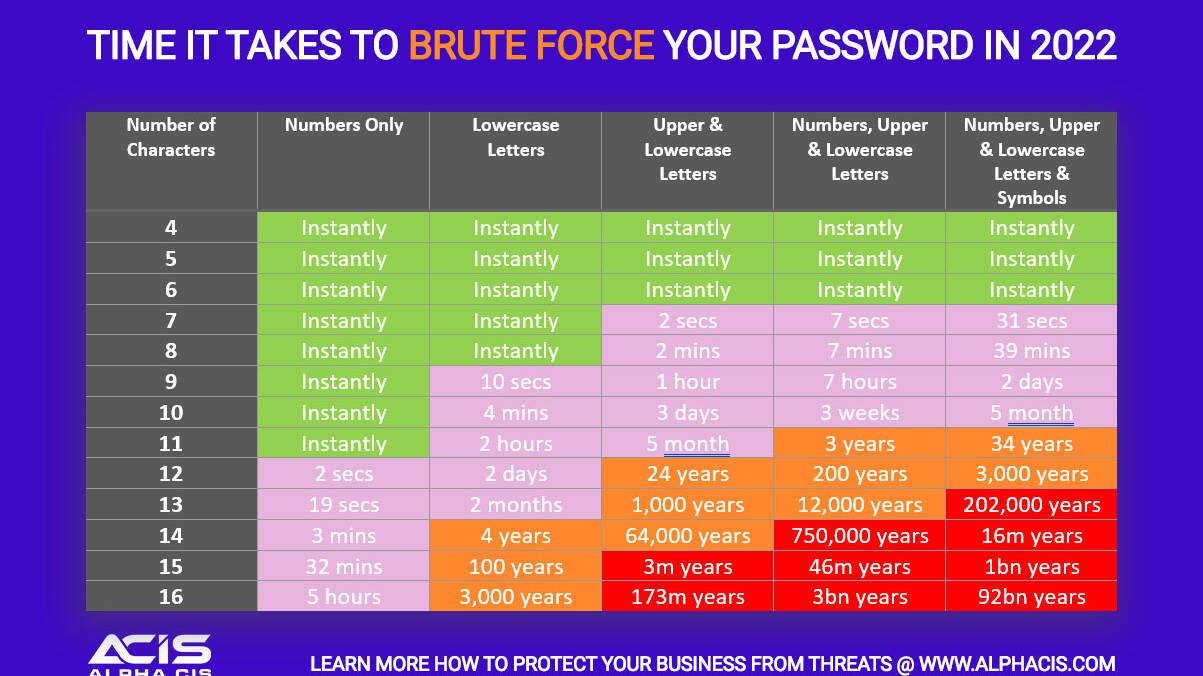
Easy tricks anyone can use to memorize complex passwords
November 22, 2022
Easy tricks anyone can use to memorize complex passwords Why you shouldn't follow the minimum password strength requirements! A password is normally one, (and sometimes the only wall), preventing an attacker from gaining access to your systems or data. Most of what are considered strong passwords require: 8 characters One Capital One Lower Case Number Symbol Here is an interesting fact, a password of this complexity can be cracked in 48 minutes, using a couple of the latest graphic cards.…
5 Mistakes Companies are Making in the Digital Workplace
October 20, 2022
5 Mistakes Companies are Making in the Digital Workplace Employees are increasingly working remotely, and as a result, companies are struggling to keep up with the changing landscape of the digital workplace. From unauthorized app use to remote work-related stress, we will discuss 5 mistakes companies are making in the digital workplace. The pandemic has forced companies worldwide to change the way they operate. No longer can everyone work in the office like before; many organizations had to…
6 easy IT policies all companies should implement right away
September 21, 2022
6 easy IT policies all companies should implement right away! Many small businesses make the mistake of skipping over policies. They believe that formalities are not necessary. They will simply inform staff what is expected when it comes up, believing this to be sufficient. However, this attitude might lead to problems for small and mid-sized business owners. Employees are not mind readers; they may misinterpret your intentions. If you don't have any rules in place, you risk being in a bad…
6 Technologies You Shouldn’t Use Anymore. Checkout #5!!
September 19, 2022
6 Technologies You Shouldn't Use Anymore. The pace at which technology develops is unquestionably rapid. Tools that were once must-haves, such as Internet Explorer and Adobe Flash, become antiquated. New tools take the place of old ones. Vulnerabilities in outdated technology can leave computers and networks open to breaches and malware infections. While older technology may still operate properly on your systems, this does not imply it is safe to use. Software and hardware that are no longer…
Employee Left- How to secure Wi-Fi from previous employee
August 15, 2022
Employee Left- How to secure Wi-Fi from previous employee Did you know that if someone has the password, they have complete access to your network? In general, I see that these passwords seldom change. Employees come and go, but the Wi-Fi password at most businesses is solid and unchanging for many years. Generally speaking, the way 99% of the networks are setup are as follows: You have your LAN - (physical network of firewall and switches) Internal Wi-Fi - A network that extends the physical…
This free Microsoft tool massively increased my productivity
July 20, 2022
This free Microsoft tool massively increased my productivity
If you are like me, you probably ditched your 2 monitor setup for an ultra wide, or perhaps 2 ultrawide. If you did jump on this trend then you quickly realized that you have a lot more real-estate to manage and organize when working with multiple windows on our computer. With ultrawide screen monitor, you probably already know that lining up 3 windows next to each other can be a task that takes time from your productivity.
Get any old unsupported printer to work with Windows 11
July 9, 2022
Get any old unsupported printer to work with Windows 11 We have all been there, when you have to get rid of your good printer because it's no longer supported by the new version of Windows. Now, this is frustrating if it’s a home printer that can be replaced for a few hundred bucks, but what if it’s a large printer that is worth $5,000 that is no longer supported. This is something that a lot of businesses are struggling with, as they don't want to spend the money on a new printer when their…
How to get your Managed IT Services for free
June 16, 2022
How to get your Managed IT Services for free There's no doubt that running a business is expensive. From the cost of goods and services, to the price of office space and employee salaries, there are a lot of expenses associated with keeping a company up and running. Bills, such as cable, internet, and telephones can sometimes add hundreds, if not thousands of dollars, depending on the location to your bottom line. One of our client’s has been using a traditional bonded T1 service through…
Who needs managed IT services(MSP)? Not this guy…
June 2, 2022
Who needs managed services? Not this guy... "Why do I need to pay for an MSP? It's not like my computer breaks often..." Typically, what I hear from clients, is that they that look at an MSP as just another utility bill, like your phone or internet. It's really much more than just another overhead expense. A good MSP relieves you, your management, and your staff, from the technical aspect of your business. It allows everyone to focus on their jobs, knowing that supporting technology will work…
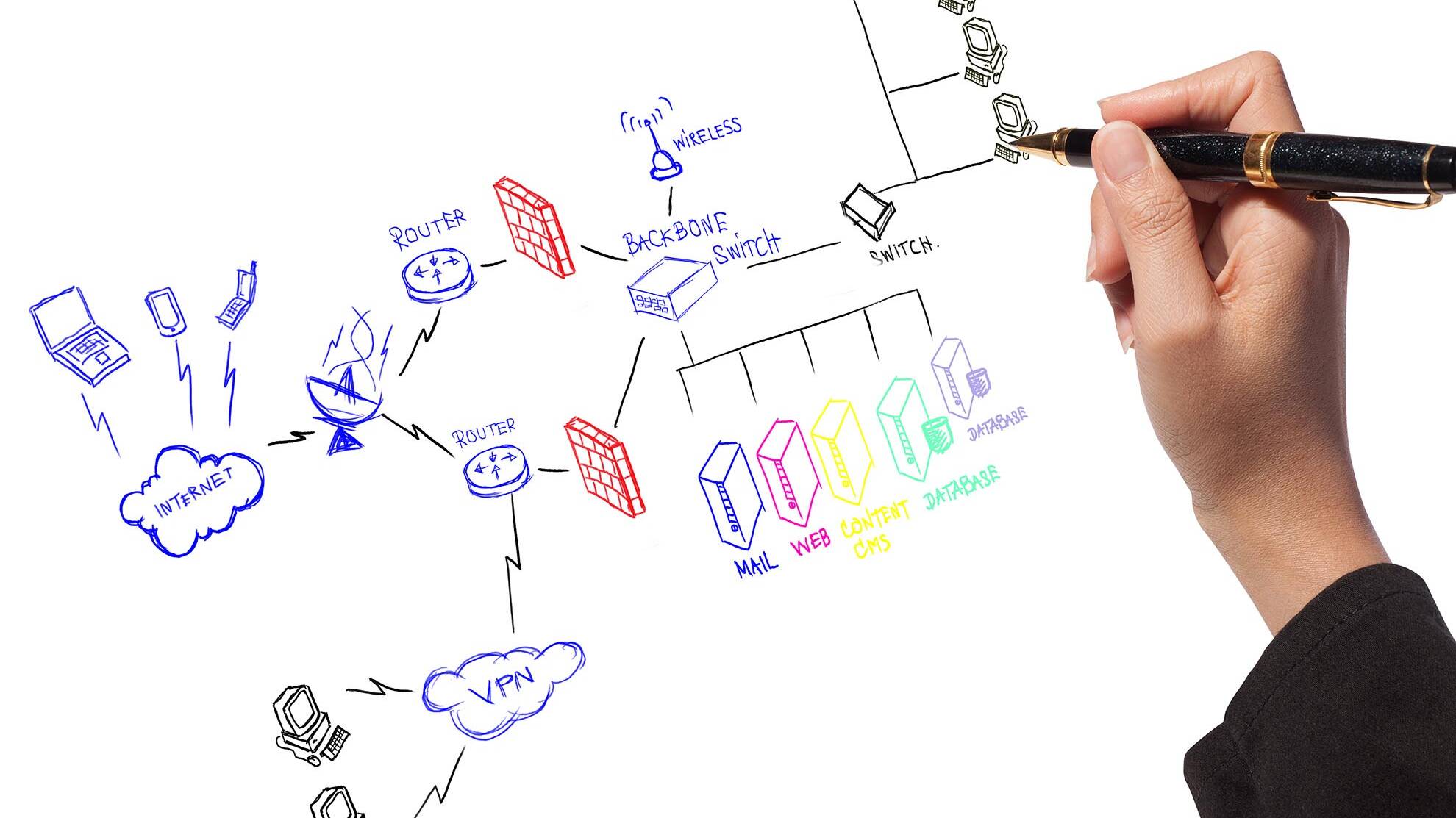
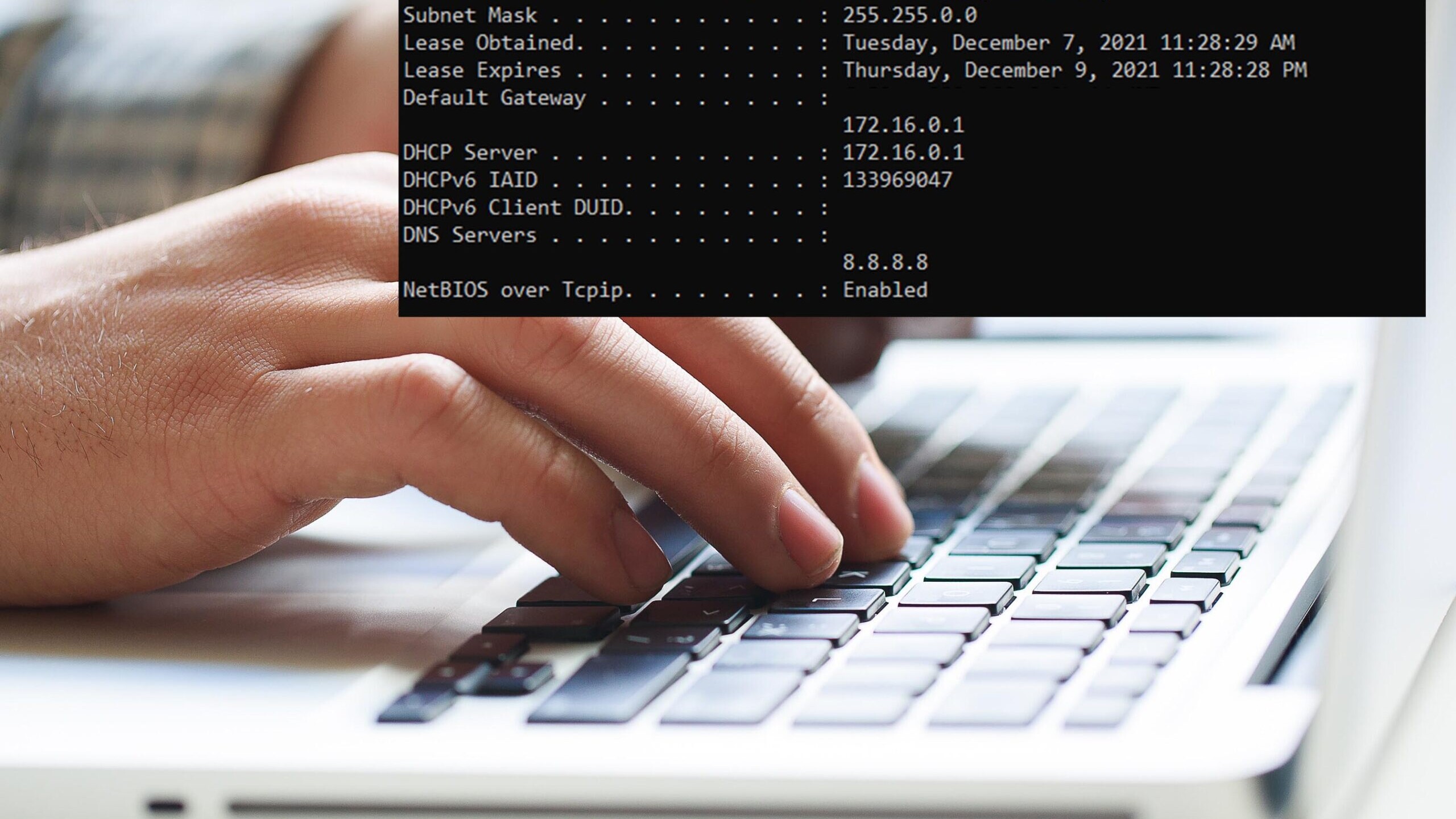
How to quickly setup your office network the correct way
May 11, 2022
How to quickly setup your office network the correct way So, you are setting up your office network, where do you begin? Depending on the size of your office, you will need different hardware and software. But there are some basic things that all office networks need in order to function properly. In this article, I will break down the hardware that will make setting up the local office network a breeze. Lets start with the basics and explain how a typical network is configured.…
How to quickly secure your network from rogue IoT devices
May 6, 2022
The easy way to secure you IoT devices and systems Internet of Things (IoT) devices are constantly growing in popularity and use, from smart thermostats to connected security cameras. While these devices provide useful features and convenience for users, they also pose a significant risk to the security of your network if not properly configured. What is an IoT device? IoT devices are physical devices that are connected to the internet and can collect, exchange, and use data. In…
Separate duties for employees or end up like this…
April 21, 2022
Separate duties for employees or end up like this... With war in Ukraine raging on, the cyber warfare between the Russians and the West continues to see an increase in Russian cybercrime. We deal with a lot of clients that employ external developers for specific projects. What we frequently discover is that these external developers and internal operations have little separations of responsibility. For example: Here is an illustration of something we just experienced with a customer. They are…
10 Ways you can fight against Russia’s cyberattacks
April 12, 2022
10 Ways you can fight against Russia's cyberattacks I had the pleasure of attending the Tech Execs Summit in Forsyth. They brought several speakers that had a lot of insight into how and why Russia's cyberwar is impacting local businesses. We are no longer threatened by the one man show that just got lucky and was able to hack into your system and get $500 in ransom out of you. These hacking organizations are ran as a business in Russia, as in they have office space, they have employees, they…
5 things: When selecting best IT Services Co. in Alpharetta
March 28, 2022
5 things: When selecting best IT Services Co. in Alpharetta This post will discuss the factors to consider while selecting an MSP for your business. Choosing an MSP is a big step in deciding to outsource or enhance your IT needs, and there are many things to think about when it comes to how it fits with your company's goals. Let's assume you're a firm of 20 employees in Alpharetta, Georgia. You previously utilized an "IT Person," to take care of day to day fixes here and there, but as your…
Data breach the new extortion method: backups are not enough
March 12, 2022
Data breach the new extortion method: backups are not enough

What to do NOW as war in Ukraine increases cybercrime
March 8, 2022
What to do NOW as war in Ukraine increases cybercrime As the war in Ukraine keeps escalating, many more cyber-crime groups are starting to emerge as a result. Why do you think this is happening? In places around the world that don’t have many opportunities to make money legitimately turn to crime to provide for their families Now let's fast forward to what is happening in Russia. Crippling sanctions have devalued the Rubel, and many vendors, companies, and industries are turning their backs on…
Top 3 cybersecurity trends to prepare for in 2022
February 21, 2022
With the COVID pandemic mostly behind us, we are faced with the reality that the workplace has forever been changed. Security is on the top minds of most business owners and CIO’s out there. Here are the new trends that we will see more of in the coming year. Location Independent Security is no longer relying on a centralized firewall Let’s rewind back to 2019, every employee comes into the office, they login to their desktop computer that was assigned to them, they work until 5pm, then, they…
What makes a good network map, and why you should care
February 17, 2022
What makes a good network map, and why you should care Do you have a network map? Chances are that if you work in networking, you do. Or did you know what a network map was before reading this article? The term is used very often and hardly anyone knows what it means. This article is intended to give an explanation of what a network map is, and why you should have one. First of all, what is a network map? A network map is a visual representation of your current and planned topology – the layout…
What John did to lose his data storing it in the wrong place
February 13, 2022
What John did to lose his data storing it in the wrong place I’ve worked with many clients in different industries; however, what I noticed is always common in majority of the businesses that we take on as clients is the lack of uniformity and processes. This includes how data is stored, handled, and transmitted. The lack of standardization creates a huge problem when it comes to keeping up with backups, ensuring there is even a backup, and also causes problems when training new employees on…
Before & after the cybersecurity training
February 7, 2022
Before & after the cybersecurity training Let's pose a scenario: Your top client receives an email from you that sounds awfully suspicious, it may go like, "Hey, I sent you the document you requested. Click this link to download the PDF." If your clients are smart, they would quickly reply to you if they think something is strange about the email. They would want to confirm if you actually sent the email. Imagine what would happen if your mailbox was either spoofed or compromised. Attackers…
3 steps to safeguard your Network Attached Storage (NAS)
February 2, 2022
Network Attached Storage (NAS) devices can be great resources on your network when it comes to centralized storage accessible to all devices on the network. The issue is that this centralized entity may be accessed from outside the network.
This past week, QNAP NAS devices have been targeted by a .deadbolt ransomware. Owners will wake up to find their data has been locked with a .deadbolt extension and ransom demands of $1,100 in bitcoin are being made so that they may unlock their data.
Security settings to change right away on your Macs
January 28, 2022
Security settings to change right away on your Macs Apple users are still just at risk of phishing attacks as any other user on any device. Although Macs come with XProtest and Gatekeeper designed to keep users safe, socially engineered attacks still don't prevent end users from handing over their credentials. If you are using your Mac for work, here are some of the things I recommend users to do on their Mac computers right away. Best practice Mac security settings to implement right away…
Quick Disaster Recovery plan to implement now for 2022
January 24, 2022
Quick Disaster Recovery plan to implement now for 2022 You have heard the words Business Continuity and Disaster Recovery being thrown around; however, I know a fiery earthquake or the great flood might not be the top of your concern. Sadly, a disaster in today's world comes in the form of cybercrime. According to TMC.net, 50% of companies that experience a cyber attack go out of business within 6 months of the attack. This is not surprising when you consider the number of preventable data…
How hackers are getting around Microsoft Defender
January 18, 2022
How hackers are getting around Microsoft Defender Microsoft presents Windows Defender as a one-solution fits all, however as we learned that is certainly not the case in the cybersecurity world. Cybersecurity should be tailored towards a particular business, there is rarely one size fits all approach here. Microsoft Defender lets users add locations or network locations to the list of excluded areas to be scanned for malware/viruses. Users commonly add folders and paths to Microsoft Defender in…
How to sell Cybersecurity by partnering instead of selling
January 11, 2022
How to sell Cybersecurity by partnering instead of selling Here is the deal, the threat actors don't care for the size of the business you have. An example can be, a small software development company that does work for larger firms. Having their clients’ data leaked can be detrimental to them. They might not have millions to pay in ransom, but the threat actors don't really care. They are perfectly fine collecting $5,000 from you and 1000’s of others. So, when I speak with a client about their…
Are you sending your credentials to a MitM without knowing it?
December 30, 2021
Are you sending your credentials to MitM without knowing it? About a month ago, we reported that some phishing kits had added the capability of intercepting SMS-based 2FA tokens. Since then, we decided to look for more such tools and found a whopping 1200+ web-based phishing kits in our research, which are capable of intercepting 2FA when it is used by unsuspecting users. These toolkits enable any wimpy "hacker" to utilize the MitM (Man-in-the-Middle) attacks. After many major tech companies…
Security settings you need to change right away for 2022
December 27, 2021
Security settings you need to change right away for 2022 Often times we think of security solutions as just an antivirus and you are done. At least that's what most business owners assume it takes to secure their systems. But outside of only installing and running an antivirus solution there are policy that windows by default allows. Depending on the environment, I like to make sure that our client's systems are as secure as they can be without breaking their software and work flow. Sometimes…
Why you should care about the Log4J vulnerability
December 21, 2021
Why you should care about the Log4J vulnerability Apache is an HTTP server that is open-source, cross platform and represents about 33% of all websites on the internet and countless applications that utilize parts of it. Log4J is a Java logging library used by the Apache server and many of those applications. A vulnerability was recently discovered in Log4J that could allow an attacker to execute malicious code on the target system. The vulnerability specifically affects versions 2.x and 3.x of…
How to quickly pass a PCI compliance scan
December 17, 2021
How to quickly pass a PCI compliance scan The Payment Card Industry Data Security Standard (PCI DSS) is a set of regulations that businesses need to follow in order to protect sensitive credit card and personal information. It can be hard for small business owners who don't know how the PCI DSS works, but there are some steps you can take to get compliant quickly and easily. In this blog post, we will discuss what it takes to become compliant with the standards and why you should care about…
Tricks to diagnose and restore your internet connection
December 10, 2021
Tricks to diagnose internet connection from your seat I ask this question on interviews when checking to see if a technician knows basic networking, and you would be surprised how many do not! I will help you out without getting technical, explaining how packets are sent, and how IP addresses work. This is a tutorial with real life situations and a step by step process you can take to solve it. So, you come into the office and you are greeted with the following error stating there is no…
James received a message, “what’s this link you sent me??”
December 7, 2021
James received a message, "What's this link you sent me??" James received a reply back from his co-worker telling him that he sent them a drobox link that looked suspicious. The next day another person complained to James telling him he sent them a google doc that is asking to login and they just wanted to clarify what it was. James quickly realized someone got a hold of his company email password and has been sending spam out of his mailbox. He quickly did what he thought was the most…
These 2 simple things could save your business from a cyberattack
December 6, 2021
These 2 simple things could save your business from a cyberattack It's interesting when I hear from CEO's and business owners the usual "We are not big enough to get hacked," or "Why would anyone want to target us?" What I always tell our clients is that the threat actors don't care what you do, they don't care how much money you make, all they care about is that you make it, all they care about is that you have an open system, or you fell prey to a phishing, or spear phishing attack, and they…
MSP tips for SMB – Enterprise backup on budget for your organization
November 29, 2021
MSP tips for SMB - Enterprise backup on budget for your organization Some may think when selecting a Managed Services Provider MSP, that we have access to some magic secrete sauce programs, or develop things in house to help secure or backup or manage your systems. We use the same software available to most business owners! Keep in mind I am in no way shape or form getting paid by any of these companies or services that I talk about below, so I just want to make it clear that this is strictly…
How do you migrate to Office 365? Smoothly…
November 26, 2021
How do you migrate to Office 365? Smoothly... If you are on a different hosted platform of exchange, it takes careful planning, staging, and execution and communication with end users. Understanding the environment and gathering as much information as possible is the first critical step. This ensures no surprises happen later or you come to a step where you aren't sure how to proceed. We must first answer some questions prior to migration Are we only moving email boxes or other office…
Still not on Office 365? Here is a good reason to switch…
November 23, 2021
Still not on Office 365? Here is a good reason to switch... Reasons why you should migrate to Office 365 if you are still on another platform. By now I don’t have to explain the benefits of exchange email and why its much better than SMTP and POP3. What is Exchange or Office 365 email? Let's just put it this way, if you want a centralized location for your emails that you are accessing with multiple devices, your cell phone, computer, tablet etc. All emails read on any device will be kept and…
8 things to do in case your systems have been breached
November 19, 2021
8 things to do in case your systems have been breached Finding out that your company has been the latest unwitting victim of a ransomware attack capable of restricting computer systems and encrypting data if a ransom is not paid to cybercriminals would be a nightmare for many corporations. There is no such thing as a magic wand that can make a ransomware assault disappear without some down time, sweating, and getting your IT team involved in restoring systems. 1. Do Not open the ransom…
Quickly check the Dark Web for your leaked credentials… without checking the Dark Web
November 16, 2021
Quickly check the Dark Web for your leaked credentials… without checking the Dark Web Ever wonder if your most used username and password is floating out there in the dark web, but don't want to install a Tor browser, start visiting questionable underground websites, downloading data dumps by hacking groups and spending hours running queries to find your username and password present in these databases? You are in luck because Google did all the hard legwork for you. Chrome is a…
So you think 2FA is protecting you… That’s cute
November 8, 2021
So you think 2FA is protecting you... That's cute The phone rings, a voice on the other end states, "Welcome to Chase Fraud protection department, we have recently receive a charge from E Constants online retailer for $74.32. If this was not you, please press 1." A few seconds later the phone buzzes and it's a text message from 227895 number which is the same number you always receive the verification code from. You quickly type it in to confirm that it is in fact you. The voice continues:…
What your “IT Guy” won’t tell you. MIGHT hurt you…
November 3, 2021
What your “IT Guy” won’t tell you. MIGHT hurt you… I'm sure there's more than one IT person who's reading this wondering what they've done to be scrutinized. But here it goes.... Things that are common with "IT Guys" I will first list out some of the concerns that you should think about, and then we can dive deeper into them… Single Point of Failure Poor Documentation Security Risk Can't be the” Jack of all Trades” Single Point of Failure I can't stress enough how important this point…
If you have Office 365, you should utilize Azure AD to protect your firm for free!
November 2, 2021
If you have Office 365, you should utilize Azure AD to protect your firm Office 365 is Microsoft's cloud productivity suite, with comparable features to Google's G Suite. It includes online versions from many of the most-used Office applications, including Word, Excel, and PowerPoint. A basic version of Azure AD is included FREE of charge with your Office 365 subscription! One compelling feature of Office 365, that your firm may not know about, is Azure Active Directory (Azure AD),…
The biggest cybersecurity threat in 2021 and 2022 affecting all businesses
November 1, 2021
What is the biggest cybersecurity threat to businesses in 2021 and 2022 that affects all businesses The types of cyber attacks that pose the most serious threat vary depending on the business. There are many different kinds of attacks that hackers might launch, including phishing attempts, ransomware, distributed denial-of-service (DDoS), and more. However, not all threats are created equal. For example, a ransomware attack is usually much more harmful than a DDoS attack because ransomware…
What is the cost for managed IT services in Atlanta?
October 28, 2021
What is the cost for managed IT services in Atlanta? What is the cost for managed IT services in Atlanta in 2023? The answer to this question varies depending on the companies and services they offer. Most MSPs will sound the same when it comes to the service and their promises however; every offering is different and you will be hard pressed to find two MSPs that use the same tools in their offerings stack. An offerings stack is basically the technology your MSP uses to deliver their…
What 5 minutes of interruption can do to your workflow
October 21, 2021
What 5 Minutes of Interruption Can Do To Your Workflow I think it’s safe to say that everyone agrees, time is money. Interruption in our tasks can add up very quickly. For example, a study done at The University of California by Gloria Mark, says that it takes about 25 minutes to return to the original task after an interruption. There are multiple studies that also confirm, distractions don't just eat up time during the distraction, they completely derail any sort of productivity for almost 30…
How Invisible IT Costs Add up fast & How to Calculate Them
October 20, 2021
How invisible IT costs add up quickly and how to calculate them When you hear Managed Service Providers (MSP) companies talk about saving you money, making things more efficient etc., etc., (insert more IT jargon here). What does this all mean? Hiring an IT support provider costs companies money right? So how do they claim to solve world problems and save your business money? Let's start by defining what an MSP is, the promises that MSPs make, how they plan to save you money, and how to tell…
How Lisa had her paycheck stolen – Phishing Attack
October 14, 2021
How Lisa had her paycheck stolen - Phishing Attack Here is how Lisa had her paycheck stolen. Lets walk through the events leading up to it and how it actually happened! BECKY FROM HR Received an email from an employee named Lisa requesting to change her paycheck to be deposited into a different bank account. Becky sent a reply with an attached document labeled “ACH Bank Change Form” to change the bank where the money is going to be transferred into this Friday for payroll. She received an email…
Retrofit your computer with biometric for $80
October 8, 2021
In the spirit of October Security month. We have used biometrics to unlock our phones, pay at the grocery stores, log in to our bank accounts for many years now. It only makes sense that this level of security makes it into mainstream day-to-day use on our desktops and laptops. Although many devices already include this feature such as a fingerprint reader, Yubicon now offers a retrofit for older devices to utilize biometrics instead of passwords. Check out this $80 USB key that doubles as a…
What it was like for a CPA firm to survive a cyberattack
October 5, 2021
What it was like for a CPA firm to survive a cyberattack I met Joe at a networking event, he is a CPA and owns his own Public Accounting Firm. Over time we became friends and I assisted his MSP (Managed Services Provider) on several IT projects. He employs 12-15 accountants depending on the time of the year. One Friday, Joe noticed that his systems were running a little slow. Being that it was a Friday afternoon, and having had dinner plans in a few hours with his family and a few friends, he…
Skip the line! Install Windows 11 and don’t wait for automatic update!
October 5, 2021
Outside of a controversial Start Menu, windows 11 appears to be mostly familiar to everyone. You can checkout the new features from Microsoft. However if you don't want to wait until the new update arrives to your computer as an automatic update. Don't worry, just head over to Microsoft and download the new update. This link will take you straight to MS page where you can download the update for FREE! You can create installation media like a USB drive or create an ISO. Really easy. If you are…
Network closet cleanup. How to save money & organize data closet
September 30, 2021
Network closet cleanup. How to save money & organize data closet If your data closets look like a rats nest with unorganized unlabeled wires everywhere, congrats, you are in with the majority! Most of our clients that we come across have a similar issue. Its easy for multiple vendors, your staff and everyone else having their hand in the network closet. No one really wants to fix it since its viewed as an unnecessary and expensive endeavor to…
Microsoft Explains why Windows 11 will be soo much faster!
September 15, 2021
This 12 min video explains all the features of upcoming Windows 11 and what will make it soo much faster than windows 10. Its pretty impressive that microsoft listened to the feedback of the beta tester program and made the suggested improvements. The real interesting feature is how you will no longer put your computer to sleep / power it down. It will work similar to what your phone does when it is not touched for a few min. The screen will turn off and the only thing that will remain powered…
Stop ransomware with these TWO steps
September 15, 2021
Stop ransomware with these TWO steps In a world where you can sign up as Ransomware As A Service its no surprise that its soo profitable and soo lucrative that everyone must take the steps to ensure they are protected, because everyone is a target. Windows 10 and 11 comes with many security features that you might not know about that can help in protecting your systems. Although 3rd party AntiVirus solution is advisable, taking these simple TWO steps can further increase the security of your…
500,000 Fortinet VPN Credentials Just Got Leaked
September 10, 2021
500,000 Fortinet VPN Credentials Got Leaked on Hackers Forum The list of Fortinet VPN credentials was released by a malicious actor known as "Orange," who is the administrator of the recently launched RAMP hacking forum and a past leader of the Babuk Ransomware initiative. Almost 500,000 Fortinet VPN login names and passwords that were scraped in an exploit on multiple devices a year ago. Orange split off to form RAMP and is now thought to be a representative of the new Groove ransomware…
Read this before you hire an IT support company…
August 18, 2021
CLICK PLAY TO LISTEN TO THIS ARTICLE [audio src="https://www.alphacis.com/wp-content/uploads/2021/08/Murf-7.mp3" /] When your business needs to move beyond what you can DIY on your own, it might be time to start thinking about outsourcing your IT. Every company has a different set of needs and various levels of expertise that is needed. You should evaluate which outsourcing service is best for your organization to minimize risk and overhead. This article will talk about the things to consider when evaluating a…
Remove NAS from Active Directory (AD) Right Away!
August 6, 2021
If you are able to connect to your Network Attached Storage Device with your Active Directory credentials it might be a good idea to change the way your NAS authenticates. Ransomware attacks on the rise its hard to think of a work environment where inside the network should be thought of as unsecure space. Unfortunately with social engineered attacks, such as phishing and new exploits being found daily it’s the reality in 2021. Once the hackers gain access to the network, they can encrypt local…
Do This Now to Reduce Cyber Insurance Policy Costs
July 21, 2021
When it comes to insurance reducing exposures is what underwriters generally focus on to determine the premium costs: Are you storing sensitive data? Are you running credit cards through your terminals? Is your staff trained in security? Do you run backup software and do you test these backups periodically? Are you using firewalls and AV software and is it up to date and managed? Do you have a 3rd party company or internal employees that specialize in managed your network and security?……
Why Your Business Will Need Next Generation Firewall (NGFW)
July 10, 2021
What is a next-generation firewall (NGFW)? A next-generation firewall (NGFW) is a network security appliance capable of inspecting traffic at the protocol level. An NGFW can enable companies to block unauthorized access, prevent malware from entering the network and securely accelerate business applications. This takes things one step further with not just inspecting packets going in and out of the network, but breaks things down further depending on the applications. What is the difference…
ALL CPA firms should register .CPA Domain while it’s still available!
July 5, 2021
AICPA launched a new CPA-specific top level domain (TLD) that will help you build trust and reach your clients in a more secure way. This verification process ensures that only those who meet certain requirements can register for this TLD, which adds another safeguard and level of trust for potential clients. If your practice hasn't jumped on getting their .CPA domain yet I suggest you do this right away. Unlike .com .net .org or many others that anyone can register for, .CPA MUST in fact be a…
Cybercriminals Are Now Targeting CPA and Accounting Firms ?
June 29, 2021
Cybercriminals Are Now Targeting CPA and Accounting Firms Reasons for targeting accounting firms is almost obvious. Consider if you are trying to get sensitive information such as bank accounts, access to retirement and investment accounts, social security and EIN numbers. What industry would you turn to as a hacker ? The answer is clear, ✅ CPA and accounting firms. Unfortunately, too many of these firms have much of this sensitive client information sitting on a network drive or local…
5 Ways Dealerships Can Save Money On I.T. Costs
June 16, 2021
1. Stick with one vendor for managing I.T. Think of services with a major cable company or Internet provider. It’s always cheaper when you bundle multiple services, like internet and T.V., and/or phone. This concept is also true when it comes to selecting an I.T. services vendor. Much like a Dr., you would not want a brain surgeon operating on your heart. This is also true when it comes to IT providers as well. An I.T. company that dabbles in 20 different industries more than likely…
Do these 3 things right now to prevent ransomware on your systems!
June 9, 2021
Do these 3 things right now to prevent ransomware on your systems! Quick and simple, ransomware works by encrypting your hard drive and any device connected to your computers. This makes all of your files inaccessible and you will see text documents in every folder with instructions on how to pay the ransom to get your files decrypted. A fun fact about ransomware is that in 2020 the attacks increased by 130%. If you break down that number, 81% of the total infected are enterprises, and 62% of…
Fire your IT guy if they do any of these things…
June 7, 2021
Why you should fire your IT guy Over time things change, people change, and your organization's needs change as well. Here are some of the things to look out for with your current IT guy. Complacency Number one reason to fire your IT guy is complacency. Just like politicians holding the same public office position for 20+ years, they get use to the easy life! Doing things “the way they have always been done” is one of the easiest ways to spot complacency! “The way things have been…