Article Summary
• Who this is for: Manufacturing owners, plant managers, and operations leaders running production environments with legacy or aging control systems
• The challenge: Critical production systems are running on unsupported technology, creating major exposure to cyberattacks, compliance failures, and costly downtime that can exceed $50K+ per hour
• Key insights covered:
- Unsupported systems become high-risk entry points with no security patches, making them prime targets for ransomware and operational disruption
- Downtime, compliance penalties, and denied insurance claims create a compounding financial impact far beyond IT costs
- Legacy systems persist due to cost, integration complexity, and production risk—but delaying upgrades increases long-term liability
- Strategic mitigation (segmentation, monitoring, phased upgrades) reduces risk without requiring full system replacement upfront
• Your outcome: Gain a clear, prioritized path to reduce operational risk, protect production uptime, and modernize systems strategically—without disrupting operations or overspending
Unsupported systems in manufacturing create significant business liability through security vulnerabilities, compliance violations, and operational disruptions that can cost companies millions in downtime and regulatory penalties. These legacy systems, while often critical to production, no longer receive security patches or vendor support, making them prime targets for cyberattacks and creating cascading risks throughout manufacturing operations.
Key Takeaways
• Security vulnerabilities multiply rapidly once vendor support ends, with no patches available for newly discovered threats
• Compliance violations can result in hefty fines and lost certifications when outdated systems can’t meet current regulatory standards
• Downtime costs escalate quickly – manufacturing downtime can cost $50,000+ per hour depending on industry and production scale
• Cyber attackers specifically target legacy systems because they’re easier to exploit and often have broader network access
• Insurance coverage may be denied for incidents involving known unsupported systems, leaving companies financially exposed
• Integration challenges increase as newer systems can’t communicate effectively with outdated platforms
• Strategic modernization approaches can reduce risk without requiring complete system overhauls
• Network segmentation and monitoring provide interim protection while planning long-term upgrades
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
What Makes Systems “Unsupported” in Manufacturing Environments
A system becomes unsupported when its vendor stops providing security updates, technical support, or compatibility maintenance. For manufacturing companies, this typically occurs with older versions of industrial control systems, human-machine interfaces (HMIs), and specialized production software that may have run reliably for years.
Common unsupported systems in manufacturing include:
- Windows XP or Windows 7 machines controlling production equipment
- Legacy programmable logic controllers (PLCs) from discontinued product lines
- Older versions of manufacturing execution systems (MES) and enterprise resource planning (ERP) software
- Specialized machine control software that vendors no longer maintain
- Industrial databases running on outdated platforms
The challenge is that these systems often control critical production processes and may be deeply integrated with expensive machinery. Unlike office computers that can be easily replaced, manufacturing systems require careful coordination with production schedules and significant capital investment to upgrade.
Key warning signs your systems may be approaching end-of-support:
- Vendor announcements about product lifecycle changes
- Difficulty finding compatible hardware replacements
- Security patches are becoming less frequent before stopping entirely
- Technical support requiring premium fees or becoming unavailable
Why Manufacturers Continue Relying on Outdated Technology
Manufacturing companies often maintain unsupported systems longer than other industries due to unique operational constraints and financial considerations. The “if it’s not broken, don’t fix it” mentality makes sense when production uptime directly impacts revenue and customer commitments.
Budget constraints play a major role. Upgrading manufacturing systems often requires significant capital expenditure, not just for software licensing but for compatible hardware, system integration, employee training, and potential production downtime during transitions. Small to mid-sized manufacturers may struggle to justify these costs when current systems appear to function adequately.
Production scheduling creates additional complexity. Unlike office environments, where computers can be updated during lunch breaks, manufacturing system upgrades often require coordinated shutdowns that impact delivery schedules and customer commitments. This operational reality pushes many companies to delay necessary updates until they become critical.
Integration dependencies make changes risky. Manufacturing systems are often interconnected in ways that weren’t fully documented when originally installed. Companies worry that upgrading one component might break connections to other critical systems, potentially causing extended downtime that far exceeds the cost of maintaining older technology.
However, this short-term thinking creates long-term liability that can ultimately cost far more than proactive modernization. The unsupported systems risks manufacturing companies face compound over time, making delayed action increasingly expensive and dangerous.

Major Security Vulnerabilities That Threaten Manufacturing Operations
Unsupported systems become security time bombs because they stop receiving patches for newly discovered vulnerabilities. In manufacturing environments, these security gaps create particularly dangerous risks because production systems often have elevated network privileges and direct control over physical processes.
Cybercriminals specifically target manufacturing companies because industrial systems typically have weaker security controls than traditional IT infrastructure. Legacy manufacturing systems were often designed for reliability and ease of use rather than security, assuming they would operate in isolated environments that no longer exist.
Common attack vectors against unsupported manufacturing systems include:
- Ransomware that encrypts production data and control systems
- Remote access trojans that allow attackers to manipulate production processes
- Data theft targeting proprietary manufacturing processes and customer information
- Supply chain attacks that use compromised manufacturing systems as entry points to customer networks
The consequences extend beyond typical data breaches. When attackers compromise manufacturing systems, they can disrupt production, damage equipment, compromise product quality, or even create safety hazards for workers and end users.
Real operational impacts of security breaches:
- Production lines shut down while systems are rebuilt and verified
- Quality control processes compromised, requiring product recalls or additional testing
- Customer data exposed, leading to notification requirements and potential lawsuits
- Intellectual property stolen, including proprietary processes and product designs
Manufacturing companies also face unique compliance requirements that unsupported systems often can’t meet, creating additional liability beyond direct security risks.
Compliance Violations and Insurance Coverage Gaps
Regulatory compliance becomes increasingly difficult with unsupported systems as standards evolve but legacy platforms can’t be updated to meet new requirements. This creates a growing gap between what regulations require and what older systems can deliver.
Industries with strict compliance requirements face particular challenges:
- Medical device manufacturing must meet FDA cybersecurity guidelines
- Automotive manufacturers need to comply with supply chain security standards
- Food and beverage companies face FDA and USDA data integrity requirements
- Chemical manufacturers must meet environmental and safety reporting standards
Insurance companies are becoming more selective about covering incidents involving known unsupported systems. Many policies now include specific exclusions for losses resulting from unpatched systems or require companies to maintain current security standards as a condition of coverage.
This means that a security incident involving unsupported systems could result in both regulatory fines and insurance claim denials, creating a double financial impact that could threaten business viability. Companies may find themselves personally liable for costs they assumed would be covered by insurance.
Compliance documentation becomes problematic when systems can’t generate required audit trails or security reports. Unsupported systems may lack the logging capabilities or data formats that regulators expect, making it difficult to demonstrate compliance even when processes are actually following required procedures.

Real Operational Impact: Downtime and Revenue Loss
The financial impact of unsupported systems extends far beyond IT costs when these systems fail or require emergency replacement. Manufacturing downtime creates cascading costs that affect customer relationships, employee productivity, and overall business reputation.
Downtime costs in manufacturing typically include:
- Direct production losses based on hourly output value
- Employee wages for idle workers during system outages
- Rush charges for emergency technical support and replacement parts
- Expedited shipping costs to meet delayed customer commitments
- Potential penalty payments for missed delivery deadlines
The urgency factor multiplies costs significantly. When unsupported systems fail unexpectedly, companies have limited options for quick resolution. Vendor support may be unavailable or extremely expensive, replacement parts may be discontinued, and alternative solutions require hasty implementation without proper planning.
Customer relationships suffer when production commitments can’t be met. Manufacturing companies often operate on tight delivery schedules where delays trigger penalty clauses or lost future business. The reputational damage from unreliable delivery can persist long after technical issues are resolved.
Quality control becomes compromised when backup systems or manual processes replace automated controls during outages. This can lead to product defects, increased waste, or additional testing requirements that extend the impact beyond the initial system failure.
Smart manufacturers recognize that the cost of proactive modernization is typically much lower than the cost of reactive crisis management when unsupported systems inevitably fail.
Why Attackers Specifically Target Legacy Manufacturing Systems
Cybercriminals view unsupported manufacturing systems as attractive targets because they combine high-value assets with relatively weak security controls. These systems often control expensive equipment and valuable intellectual property while lacking the security monitoring and access controls found in modern IT environments.
Legacy systems are easier to exploit because their vulnerabilities are well-documented, and no patches are available to fix them. Attackers can use publicly available exploit tools that work reliably against known system weaknesses, reducing the technical skill required for successful attacks.
Manufacturing systems often have excessive network privileges that allow attackers to move laterally through company networks once they gain initial access. Legacy systems may have administrative rights or direct connections to other critical systems that were originally designed for operational convenience rather than security.
The physical impact potential makes manufacturing attractive to certain attackers. Unlike purely digital systems, compromised manufacturing equipment can cause physical damage, safety hazards, or environmental incidents that create additional leverage for extortion or create broader disruption for political purposes.
Intellectual property theft represents long-term value for attackers who can steal proprietary manufacturing processes, product designs, or customer lists. This information can be sold to competitors or used to establish competing operations in countries with weak intellectual property enforcement.
Manufacturing companies must recognize that their unsupported systems make them targets not just for opportunistic attacks but for sophisticated threat actors who specifically seek to exploit industrial vulnerabilities.
Strategic Risk Mitigation Without Complete System Overhauls
Smart manufacturers can significantly reduce unsupported systems risks manufacturing operations face without requiring immediate complete system replacement. A strategic approach focuses on the highest-risk areas first while building toward long-term modernization goals.
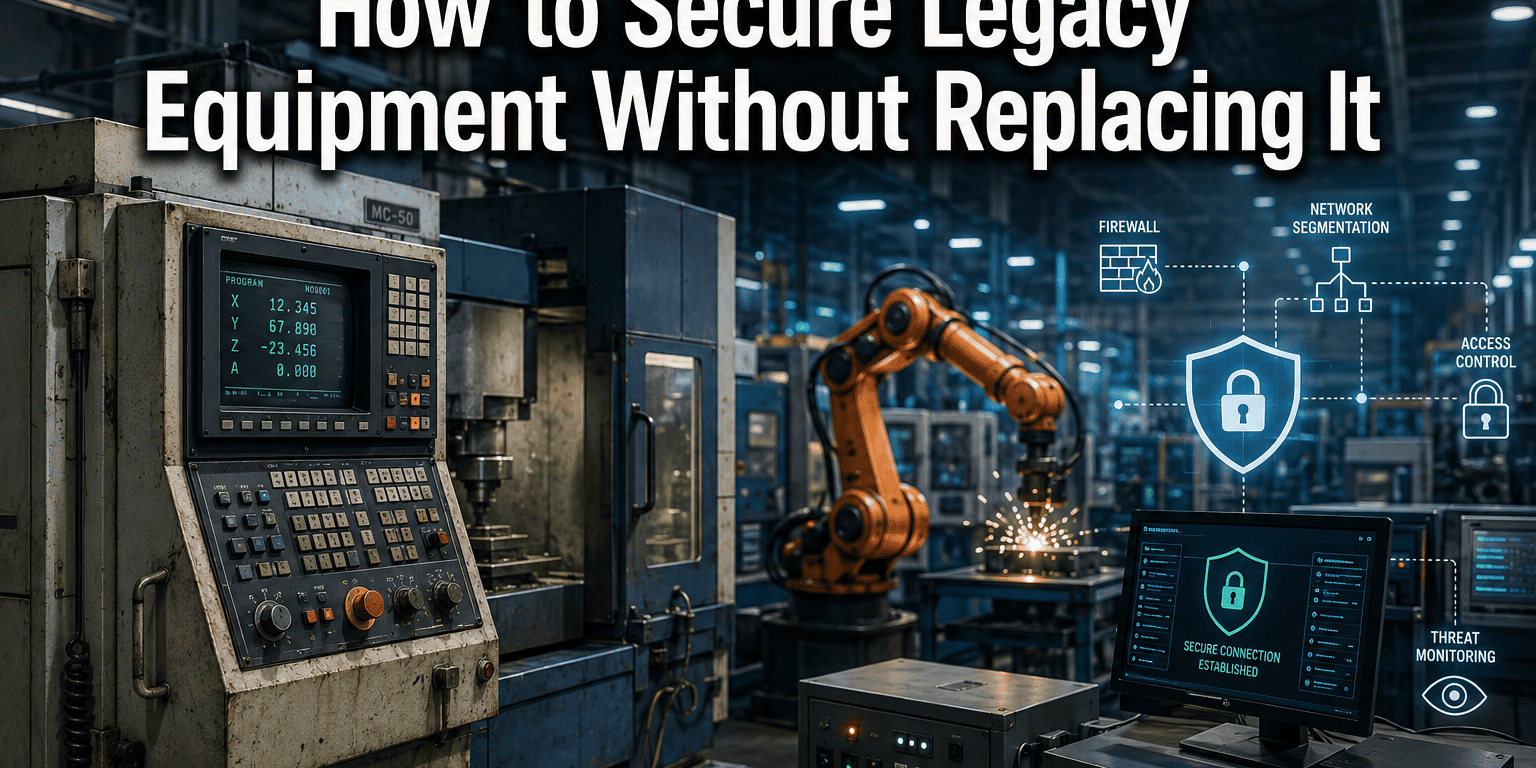
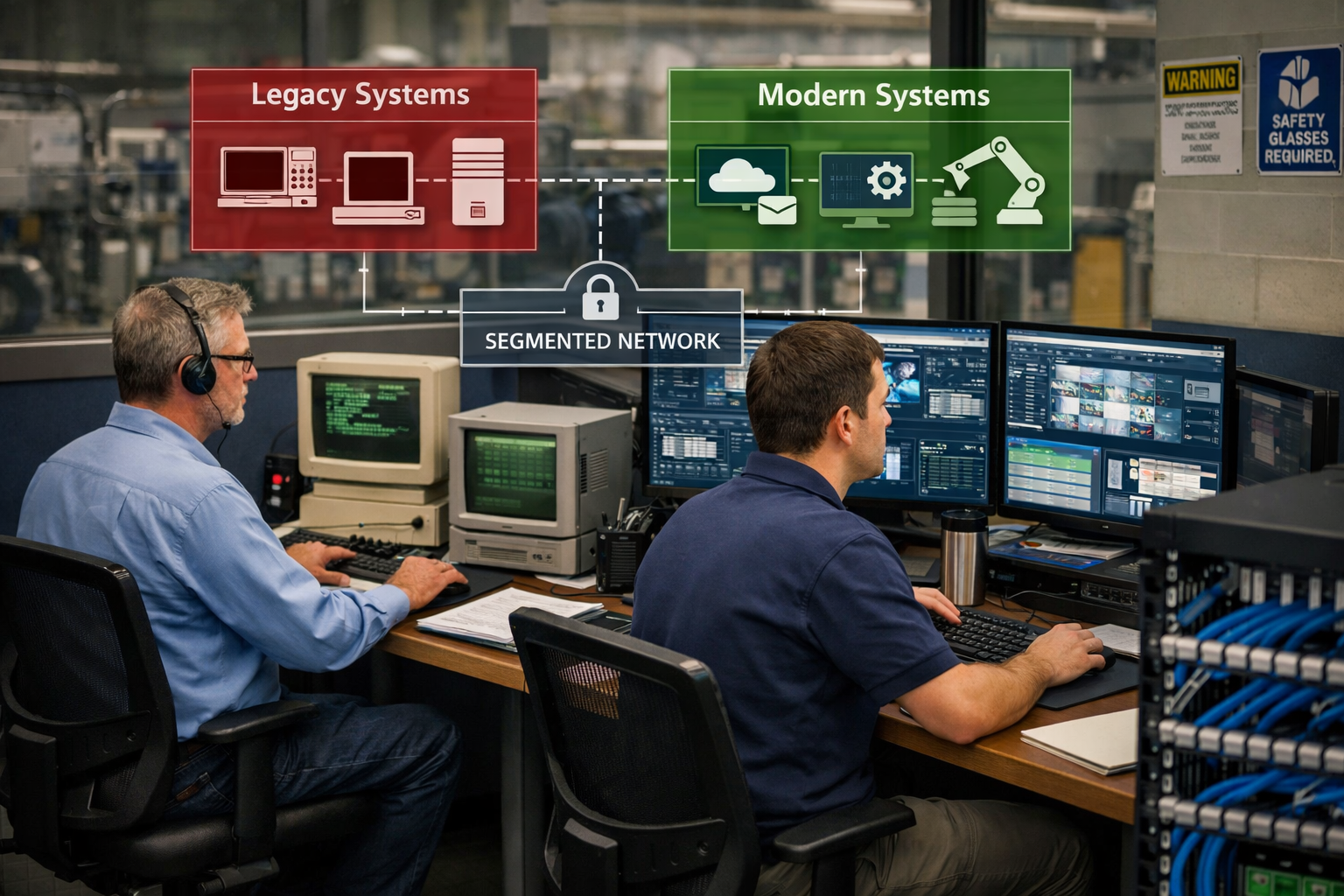
Network segmentation provides immediate risk reduction by isolating legacy systems from broader network access. This limits attackers’ ability to use compromised legacy systems as stepping stones to other critical infrastructure while maintaining necessary operational connectivity.
Enhanced monitoring compensates for missing security features in legacy systems by providing visibility into unusual activity or unauthorized access attempts. Modern monitoring tools can often integrate with older systems to provide security oversight without requiring system modifications.
Virtual patching solutions can provide interim protection for known vulnerabilities in unsupported systems by filtering malicious traffic before it reaches vulnerable services. This approach works particularly well for systems that must remain operational but can’t be directly updated.
Gradual modernization strategies spread costs over time while reducing risk incrementally. Companies can prioritize upgrades based on risk assessment, business impact, and available budget rather than attempting comprehensive replacement projects that strain resources and increase implementation risk.
Key steps for strategic risk mitigation:
- Conduct a comprehensive inventory of all systems and their support status
- Assess business impact and security risk for each unsupported system
- Implement network segmentation to isolate high-risk legacy systems
- Deploy monitoring and logging for systems that can’t be immediately upgraded
- Develop a phased modernization timeline based on risk priorities and budget constraints
- Establish incident response procedures specific to legacy system failures
This approach allows companies to maintain operational stability while systematically reducing the unsupported systems risks manufacturing operations face over time.
Building Long-Term System Upgrade and Modernization Strategy
Successful manufacturing modernization requires careful planning that balances operational needs, budget constraints, and risk reduction goals. Companies that approach upgrades strategically can avoid the crisis-driven decisions that often lead to expensive emergency replacements and extended downtime.
Start with a comprehensive asset inventory and risk assessment. Document all systems, their support status, business criticality, and interdependencies. This foundation enables informed decision-making about upgrade priorities and helps identify opportunities for consolidation or integration improvements.
Develop realistic timeline and budget projections that account for both direct system costs and operational impacts like training, downtime, and integration work. Spreading upgrades over multiple budget cycles makes large modernization projects more manageable while providing flexibility to adjust plans based on changing business needs.
Consider cloud and hybrid solutions that can reduce on-premises infrastructure requirements while providing better scalability and automatic updates. Modern manufacturing platforms often offer cloud connectivity options that maintain local control for critical processes while enabling remote monitoring and management capabilities.
Plan for staff training and change management to ensure the successful adoption of new systems. The best technology investments fail when employees can’t effectively use new capabilities or resist changes to established workflows.
Establish vendor relationships and support contracts before you need emergency assistance. Having trusted partners who understand your operations and can provide same-day support creates peace of mind and reduces the risk of extended downtime when issues arise.
Key elements of a successful modernization strategy:
- Phased implementation that maintains operational continuity
- Redundancy and fallback procedures during transition periods
- Integration testing in non-production environments before deployment
- Documentation and training programs for new systems and procedures
- Ongoing maintenance and support arrangements with reliable partners
The goal is to create a sustainable technology environment that supports business growth while minimizing operational risk and providing the peace of mind that comes from knowing your systems are secure and compliant.
Manufacturing System Risk Assessment
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free ConsultationFrequently Asked Questions
How do I know if my manufacturing systems are unsupported?
Check with your software vendors about support lifecycle dates, look for systems that haven’t received updates in over a year, and watch for vendor announcements about product discontinuation. Systems running Windows XP, Windows 7, or very old versions of industrial software are likely unsupported.
Can I keep using unsupported systems if they’re isolated from the internet?
While air-gapped systems have reduced risk, they’re not completely safe. Attacks can still occur through USB devices, maintenance laptops, or other connected systems. Complete isolation also limits beneficial capabilities like remote monitoring and support.
What’s the typical cost difference between proactive upgrades and emergency replacement?
Emergency replacements often cost 3-5 times more than planned upgrades due to rush charges, limited vendor options, expedited shipping, and production downtime. Proactive planning allows for better vendor negotiations and coordinated implementation schedules.
How long does it take to modernize manufacturing systems?
Timeline varies based on system complexity and business requirements, but typical projects range from 3-18 months for complete modernization. Phased approaches can provide risk reduction benefits much sooner while spreading costs over time.
Will my insurance cover incidents involving unsupported systems?
Many insurance policies now exclude coverage for losses involving known unpatched or unsupported systems. Review your policy language carefully and discuss coverage requirements with your insurance provider before incidents occur.
What’s the biggest mistake companies make with legacy system management?
Waiting until systems fail before taking action. This creates crises where companies have limited options, higher costs, and greater business disruption than proactive modernization approaches.
How do I justify modernization costs to management?
Focus on business risk rather than technical features. Calculate potential downtime costs, compliance penalties, and insurance gaps, then compare these risks to modernization investment. Emphasize that proactive upgrades cost less than reactive crisis management.
Can I upgrade systems gradually without disrupting production?
Yes, with proper planning. Network segmentation, parallel system deployment, and phased cutover strategies can minimize production impact. Working with experienced partners who understand manufacturing operations is crucial for successful transitions.
What should I look for in a modernization partner?
Choose partners with specific manufacturing experience, 24/7 support capabilities, and proven track records with similar companies. Look for industry expertise, personalized service approaches, and straightforward pricing that fits your budget planning needs.
How often should I reassess my systems for support status?
Conduct formal assessments annually, but monitor vendor announcements quarterly. Technology lifecycles are shortening, so staying proactive about support status helps avoid surprise end-of-life announcements that create urgent upgrade requirements.
What’s the first step if I have multiple unsupported systems?
Start with a comprehensive inventory and risk assessment to prioritize which systems pose the greatest business liability. Focus on systems that are both unsupported and business-critical, then develop a phased approach based on risk levels and available budget.
Are cloud-based manufacturing systems more secure than on-premises?
Modern cloud platforms typically offer better security controls and automatic updates than aging on-premises systems, but the best approach depends on your specific requirements. Hybrid solutions often provide a good balance between local control and cloud benefits.
Conclusion
The unsupported systems risks manufacturing companies face represent serious business liability that extends far beyond IT concerns. These legacy platforms create cascading vulnerabilities that threaten production continuity, regulatory compliance, financial stability, and competitive position in increasingly connected industrial environments.
The evidence is clear: companies that take proactive approaches to modernization fare better than those that wait for crises to force expensive emergency responses. Strategic planning allows for better vendor relationships, coordinated implementation schedules, and cost management that makes necessary upgrades more financially manageable.
However, successful modernization doesn’t require immediate complete system overhauls that strain budgets and disrupt operations. Smart manufacturers can significantly reduce risk through network segmentation, enhanced monitoring, and phased upgrade strategies that maintain operational stability while systematically addressing the most critical vulnerabilities.
The key is recognizing that maintaining unsupported systems isn’t actually the conservative choice – it’s a growing gamble with increasingly poor odds. Each day these systems remain in production without security updates or vendor support, the risk of costly incidents grows while the options for graceful resolution diminish.
Your next steps should include:
- Conducting a comprehensive inventory of all systems and their support status
- Assessing business impact and security risk for each unsupported system
- Implementing immediate risk reduction measures like network segmentation and monitoring
- Developing a realistic modernization timeline based on risk priorities and budget constraints
- Establishing relationships with trusted partners who can provide reliable support and guidance
Don’t wait for a security incident or system failure to force your hand. The peace of mind that comes from knowing your manufacturing systems are secure, compliant, and properly supported is worth the investment in proactive modernization.
If you’re concerned about unsupported systems in your manufacturing environment, consider scheduling a comprehensive risk assessment with experienced partners who understand both the technical challenges and business realities of industrial modernization. The right approach can eliminate IT headaches while positioning your company for sustainable growth and competitive advantage.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity