Article Summary
• Who this is for: Small business owners in financial-related industries (tax preparers, insurance agencies, auto dealers, mortgage brokers, and investment advisors) who must comply with the FTC Safeguards Rule requirements
• The challenge: Many small businesses don’t realize they qualify as “financial institutions” under federal law and lack the documented security programs, encryption, access controls, and monitoring required for compliance
• Key insights covered: Who must comply, the six core pillars of the Safeguards Rule, common compliance mistakes, vendor oversight requirements, encryption standards, and how managed IT services support ongoing compliance
• Your outcome: A clear understanding of your compliance obligations—and how partnering with AlphaCIS can help you implement a structured, secure, and audit-ready cybersecurity program without disrupting daily operations

Quick Answer
The FTC Safeguards Rule requires financial institutions and businesses handling customer financial data to implement comprehensive information security programs. Small businesses, including tax preparers, insurance agencies, auto dealers, and mortgage brokers, must comply with specific cybersecurity requirements, including written security programs, risk assessments, access controls, encryption, and incident response plans.
Key Takeaways
• Many small businesses qualify – Tax preparers, insurance agents, auto dealers, and mortgage brokers must comply
• Written security program required – You need documented policies and procedures for data protection
• Risk assessments are mandatory – Regular evaluations of your cybersecurity vulnerabilities
• Employee access controls – Strict limits on who can access customer financial information
• Encryption is non-negotiable – Customer data must be encrypted both in transit and at rest
• Vendor oversight essential – You’re responsible for third-party security practices
• Incident response planning – Documented procedures for handling data breaches
• Regular monitoring required – Ongoing surveillance of your information systems
• Penalties are significant – Non-compliance can result in substantial fines and legal action
• Professional help recommended – Most small businesses benefit from managed IT security services
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation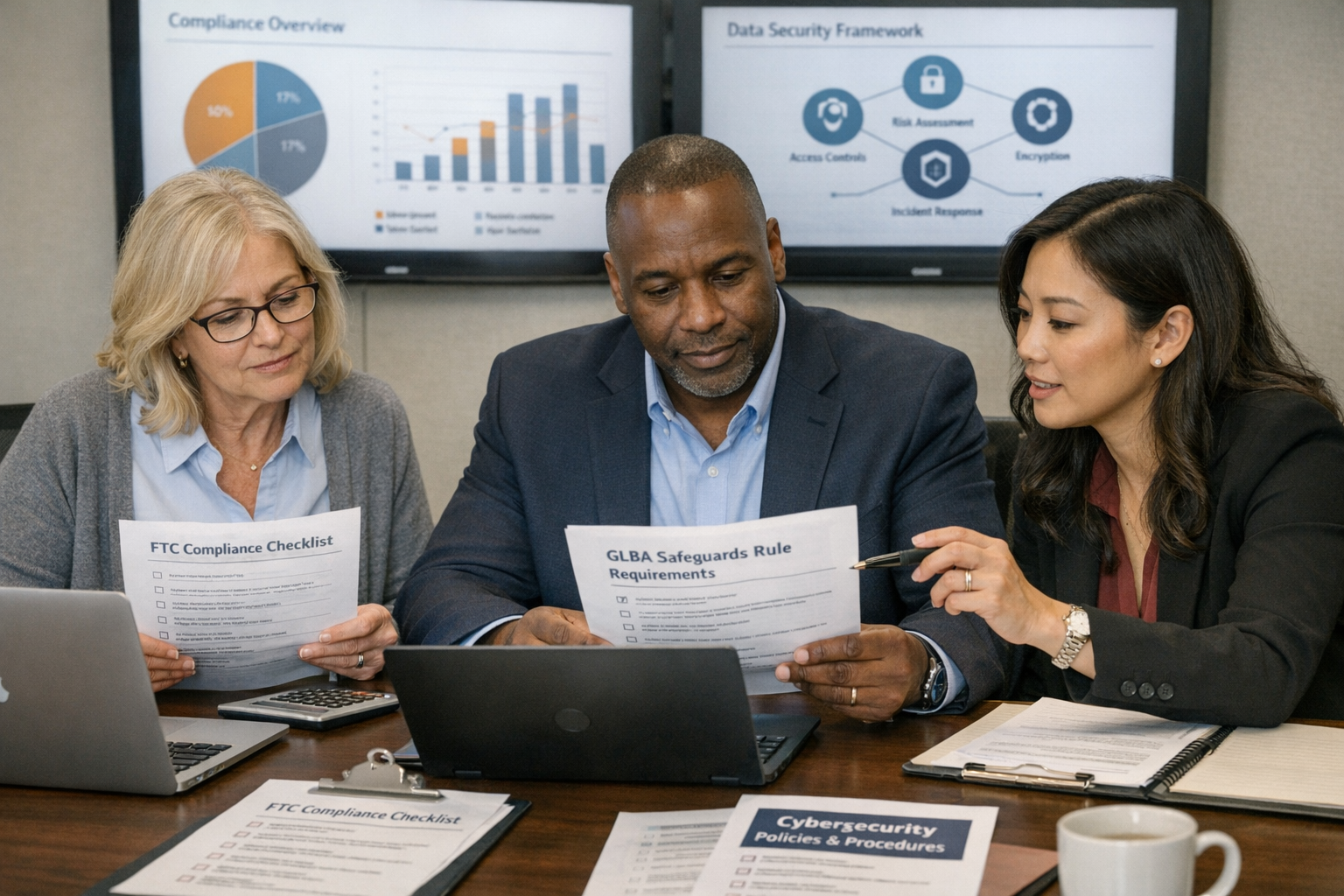
A local tax preparation firm in Atlanta discovered they were subject to the FTC Safeguards Rule just weeks before tax season. Like many small business owners, they had no idea that preparing tax returns for clients made them a “financial institution” under federal law. The scramble to achieve compliance nearly shut down their busiest season.
This scenario plays out across thousands of small businesses every year. The FTC Safeguards Rule for small businesses isn’t just for banks and credit unions; it applies to many everyday businesses that handle customer financial information. Understanding the FTC Safeguards Rule compliance can mean the difference between smooth operations and costly penalties.
What Is the FTC Safeguards Rule and Why Should Small Businesses Care?
The FTC Safeguards Rule stems from the Gramm-Leach-Bliley Act (GLBA) and requires businesses to protect customer financial information through comprehensive cybersecurity measures. The rule underwent major updates in 2021, significantly expanding requirements for small business data protection compliance.
Under this regulation, covered businesses must establish and maintain an information security program that protects customer financial data from unauthorized access. This isn’t a suggestion – it’s a legal requirement with real consequences for non-compliance.
The rule recognizes that customer data protection law must evolve with modern cyber threats. What worked for data security in 2000 simply isn’t adequate for today’s threat landscape. That’s why the updated requirements focus on proactive security measures rather than reactive responses.
For small businesses, this means you can’t simply hope your basic antivirus software and password protection will suffice. You need a systematic approach to cybersecurity that meets specific federal standards.
Who Must Comply with FTC Data Security Requirements?
Many small business owners assume the Safeguards Rule only applies to traditional banks. That’s a costly misconception. The rule covers any business that is “significantly engaged” in financial activities.
Businesses that must comply include:
• Tax preparation services – Even seasonal preparers handling individual returns
• Insurance agencies and brokers – including independent agents selling policies
• Auto dealerships – When financing or leasing vehicles to customers
• Mortgage brokers and lenders – Including small residential lending operations
• Investment advisors – Managing client portfolios or providing financial advice
• Credit counseling services – Helping consumers manage debt or credit issues
• Check cashing businesses – Including small neighborhood operations
• Payday lenders – Short-term lending services
• Real estate settlement services – Title companies and closing agents
The key test is whether your business regularly handles customer financial information as part of providing financial products or services. If you collect Social Security numbers, bank account details, credit information, or tax data from customers, you likely fall under the rule.
Common misconceptions about coverage:
Many small businesses think they’re exempt because they’re “too small” or because they use third-party software. Size doesn’t matter for compliance – a solo tax preparer has the same obligations as a large firm. Using cloud-based software doesn’t transfer your compliance responsibility to the vendor.
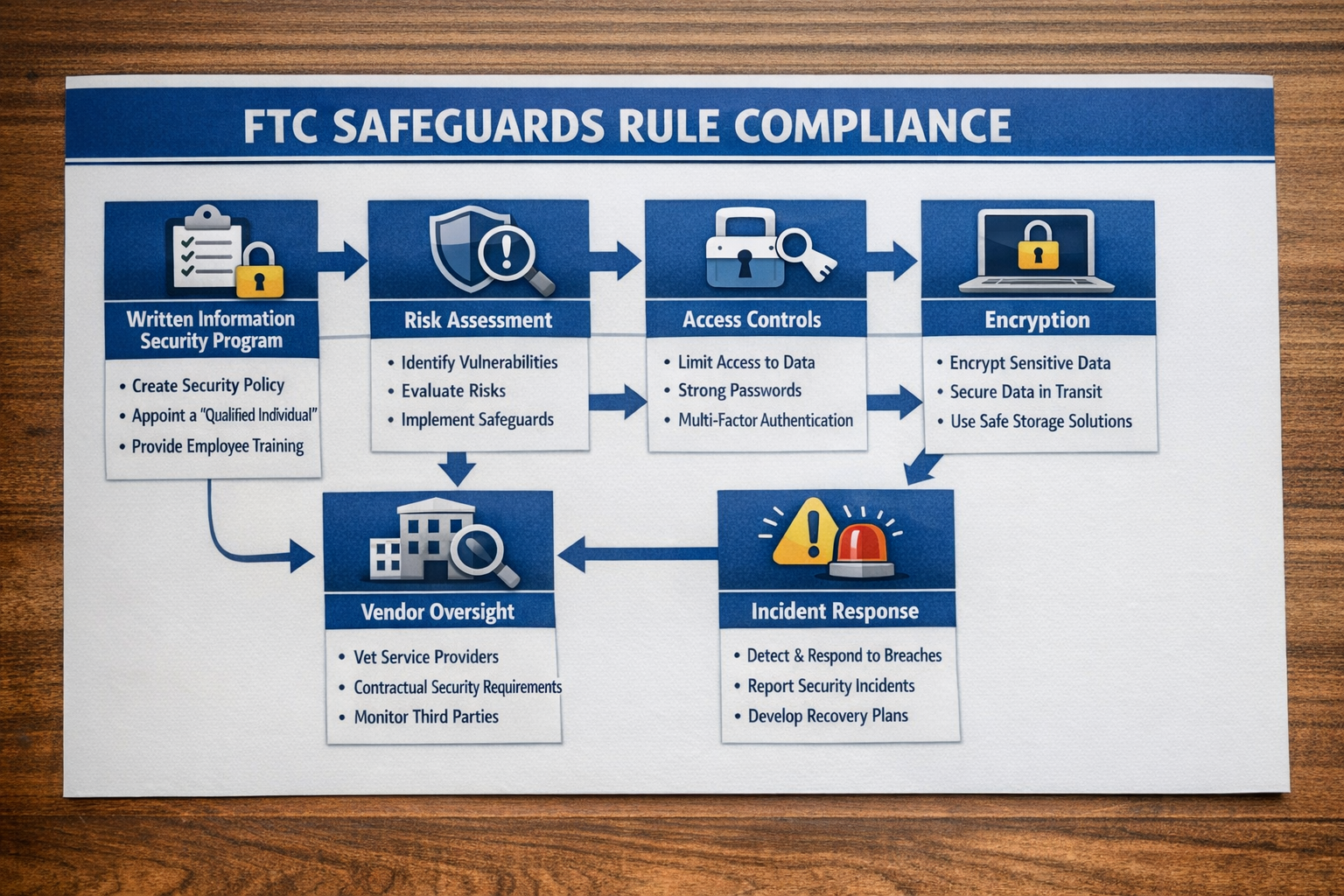
Essential FTC Cybersecurity Requirements: Breaking Down the Six Pillars
The updated Safeguards Rule establishes six core requirements that form the foundation of a compliant information security program. Each pillar addresses a critical aspect of modern cybersecurity for small businesses.
1. Written Information Security Program
You must create and maintain a comprehensive written security program that documents your approach to protecting customer information. This isn’t a one-page policy – it’s a detailed roadmap for your entire cybersecurity strategy.
Your written program must include:
• Clear security objectives and scope
• Designated security personnel responsibilities
• Risk assessment procedures and schedules
• Safeguards for each identified risk
• Regular program testing and monitoring procedures
• Incident response and breach notification plans
The program should be tailored to your specific business operations, not a generic template downloaded from the internet. A tax preparation service will have different risks and requirements than an auto dealership.
2. Risk Assessment and Management
Regular risk assessments form the backbone of effective compliance and cybersecurity SMB operations. You must identify and evaluate threats to customer information across all business operations.
Required assessment areas:
• Employee access to customer information systems
• Information system vulnerabilities and security gaps
• Physical security of offices and data storage areas
• Third-party vendor security practices and data access
• Network security and internet-connected devices
• Data backup and recovery capabilities
Risk assessments aren’t one-time exercises. You must conduct them regularly and whenever significant changes occur to your business operations or technology systems.
3. Access Controls and Authentication
Controlling who can access customer financial information is fundamental to safeguarding customer information, according to FTC requirements. You must implement strict access controls based on business needs and job responsibilities.
Key access control requirements:
• Multi-factor authentication for all systems containing customer data
• Role-based access limits employees to information needed for their job functions
• Regular access reviews to remove unnecessary permissions
• Secure authentication for all user accounts and administrative access
• Automatic session timeouts for inactive users
Many small businesses struggle with access controls because they’re used to informal, trust-based systems. However, compliance requires documented, enforceable access policies regardless of business size.
4. Data Encryption Standards
Encryption protects customer information both when stored on your systems and when transmitted over networks. The rule requires encryption of customer information both at rest and in transit.
Encryption requirements include:
• Data at rest – Information stored on computers, servers, and backup systems
• Data in transit – Information sent via email, uploaded to cloud services, or transmitted over networks
• Mobile devices – Laptops, tablets, and smartphones containing customer data
• Removable media – USB drives, external hard drives, and portable storage devices
For small businesses, this often means upgrading older systems that lack built-in encryption capabilities. The investment in encrypted storage and secure transmission methods is essential for compliance.
5. Vendor Management and Oversight
If you use third-party vendors who have access to customer information, you’re responsible for ensuring they meet the same security standards you do. This creates a compliance chain that extends beyond your direct operations.
Vendor oversight requirements:
• Due diligence before selecting vendors with data access
• Written agreements requiring vendors to implement appropriate safeguards
• Regular monitoring of vendor security practices and compliance
• Incident notification requirements for vendor-related security events
Common vendor relationships for small businesses include cloud storage providers, payroll processors, accounting software companies, and IT support services. Each relationship requires careful evaluation and ongoing oversight.
6. Incident Response and Breach Planning
When security incidents occur, you must have documented procedures for response, containment, and notification. Incident response planning helps minimize damage and ensures compliance with breach notification requirements.
Essential incident response elements:
• Detection procedures for identifying potential security incidents
• Response team with clearly defined roles and responsibilities
• Containment strategies to limit the scope of security breaches
• Investigation protocols for determining the cause and extent of incidents
• Notification procedures for customers, regulators, and law enforcement
• Recovery plans for restoring normal business operations

Common FTC Compliance Mistakes Small Businesses Make
Even well-intentioned small businesses often stumble when implementing Safeguards Rule compliance. Understanding these common pitfalls can help you avoid costly mistakes and compliance gaps.
Mistake 1: Treating Compliance as a One-Time Project
Many businesses approach FTC compliance like a checkbox exercise – create some policies, implement basic security measures, and consider the job done. This approach virtually guarantees compliance failures over time.
Why this fails: The Safeguards Rule requires ongoing monitoring, regular risk assessments, and continuous program updates. Cybersecurity threats evolve constantly, and your security program must evolve with them.
Better approach: Treat compliance as an ongoing business process with regular reviews, updates, and improvements. Schedule quarterly compliance reviews and annual program assessments.
Mistake 2: Assuming Cloud Services Handle All Security
Small businesses often believe that using cloud-based software automatically ensures compliance. While cloud services can enhance security, they don’t transfer your compliance obligations.
The reality: You remain responsible for ensuring your cloud vendors meet Safeguards Rule requirements. You must evaluate their security practices, require appropriate contractual protections, and monitor their compliance.
What to do: Conduct due diligence on all cloud vendors, require security certifications, and include specific security requirements in vendor contracts.
Mistake 3: Overlooking Employee Training and Access Management
Many small businesses focus heavily on technical security measures while neglecting human factors. Employees often represent the greatest security risk and the most important line of defense.
Common employee-related risks:
• Using weak passwords or sharing login credentials
• Accessing customer data from unsecured personal devices
• Falling victim to phishing attacks or social engineering
• Leaving customer information visible or accessible to unauthorized individuals
Essential employee safeguards:
• Regular cybersecurity training for all staff members
• Clear policies about acceptable use of business systems
• Secure procedures for handling customer information
• Regular access reviews and permission updates
Mistake 4: Inadequate Vendor Due Diligence
Small businesses often select vendors based primarily on cost and convenience, giving insufficient attention to security practices. This creates compliance vulnerabilities that can result in significant penalties.
Due diligence requirements:
• Review vendor security certifications and compliance documentation
• Evaluate vendor incident response and breach notification procedures
• Require contractual commitments to maintain appropriate safeguards
• Establish ongoing monitoring and review processes
Mistake 5: Incomplete Risk Assessments
Many small businesses conduct superficial risk assessments that miss critical vulnerabilities. Effective risk assessment requires systematic evaluation of all business processes and technology systems.
Comprehensive risk assessment includes:
• Physical security of business locations and data storage areas
• Network security and internet-connected devices
• Employee access controls and authentication procedures
• Third-party vendor relationships and data sharing arrangements
• Data backup and disaster recovery capabilities
• Incident detection and response capabilities
Simple FTC Compliance Checklist for Small Businesses
Use this practical checklist to evaluate your current compliance status and identify areas needing attention. Each item represents a core requirement under the Safeguards Rule.
Written Information Security Program
- Comprehensive written security program documented and current
- Designated qualified individual responsible for the security program
- Board or senior management oversight and approval
- Regular program reviews and updates are scheduled
- Employee roles and responsibilities are clearly defined
Risk Assessment and Management
- Initial comprehensive risk assessment completed
- A regular risk assessment schedule has been established and followed
- All business locations and operations are included in the assessment
- Third-party vendor risks evaluated and documented
- Risk mitigation strategies implemented for identified threats
Access Controls and Authentication
- Multi-factor authentication implemented for all customer data access
- Role-based access controls limiting employee permissions
- Regular access reviews conducted and documented
- Secure authentication is required for all user accounts
- Automatic session timeouts configured for inactive users
Data Encryption and Protection
- Customer data is encrypted at rest on all storage systems
- Customer data is encrypted in transit for all transmissions
- Mobile devices and laptops with customer data encrypted
- Secure disposal procedures for devices containing customer information
- Regular testing of encryption systems and procedures
Vendor Management and Oversight
- Due diligence was conducted for all vendors with customer data access
- Written agreements requiring appropriate vendor safeguards
- Regular monitoring and review of vendor security practices
- Incident notification requirements included in vendor contracts
- Vendor compliance documentation reviewed and current
Incident Response and Monitoring
- Written incident response plan developed and tested
- Continuous monitoring systems implemented for security threats
- Response team identified with clear roles and responsibilities
- Breach notification procedures documented and ready
- Regular testing and updating of incident response procedures
How Managed IT Services Support FTC Safeguards Rule Compliance
Most small businesses lack the internal expertise and resources to effectively implement and maintain Safeguards Rule compliance. This is where partnering with experienced managed IT providers becomes invaluable for achieving peace of mind.
Technical Expertise and Industry Knowledge
Managed IT providers bring specialized cybersecurity knowledge that most small businesses can’t develop internally. They understand the technical requirements of the Safeguards Rule and stay current with evolving compliance standards.
Key technical capabilities:
• Implementation of enterprise-grade security tools and monitoring systems
• Configuration of proper encryption for data at rest and in transit
• Setup and management of multi-factor authentication systems
• Regular security assessments and vulnerability testing
• 24/7 monitoring of security systems and threat detection
Ongoing Compliance Management
Compliance isn’t a destination – it’s an ongoing journey that requires constant attention and updates. Reliable partners provide the consistent oversight needed to maintain compliance over time.
Ongoing compliance services:
• Regular risk assessments and security program updates
• Continuous monitoring of security systems and threat landscape
• Vendor management and due diligence support
• Employee training and security awareness programs
• Incident response planning and breach management support
Cost-Effective Security Solutions
Building internal cybersecurity capabilities can be prohibitively expensive for small businesses. Managed IT services provide access to enterprise-level security tools and expertise at a fraction of the cost of internal development.
Economic advantages:
• Shared costs across multiple clients reduce individual expenses
• Access to premium security tools without large capital investments
• Predictable monthly costs instead of unpredictable security incidents
• Reduced risk of costly compliance violations and penalties
Proactive Solutions and Same-Day Support
The best managed IT providers focus on preventing security incidents rather than simply responding to them. This proactive approach aligns perfectly with Safeguards Rule requirements for ongoing monitoring and risk management.
Proactive security benefits:
• Early detection and prevention of security threats
• Regular system updates and security patch management
• Continuous improvement of security posture and compliance status
• Rapid response to emerging threats and vulnerabilities
When evaluating managed IT providers, look for those with specific experience in financial services compliance and FTC Safeguards Rule requirements. Ask about their approach to risk assessment, incident response, and ongoing compliance monitoring.
Preparing for FTC Audits and Enforcement Actions
The FTC actively enforces Safeguards Rule compliance through audits, investigations, and enforcement actions. Small businesses that fail to meet requirements face significant penalties and potential business disruption.
Understanding FTC Enforcement Priorities
The FTC focuses its enforcement efforts on businesses that demonstrate clear compliance failures or that experience data breaches exposing customer information. However, any covered business can be subject to audit regardless of size or compliance history.
Common enforcement triggers:
• Data breaches involving customer financial information
• Consumer complaints about data security practices
• Referrals from other regulatory agencies or law enforcement
• Random compliance audits and industry sweeps
Audit Preparation Strategies
Being audit-ready requires maintaining comprehensive documentation of your compliance efforts and security program implementation. This documentation serves as evidence of good faith compliance efforts.
Essential audit documentation:
• Current written information security program with recent updates
• Risk assessment reports and mitigation strategies
• Employee training records and security awareness documentation
• Vendor agreements and due diligence records
• Incident response plans and testing documentation
• Security monitoring logs and system configuration records
Working with Legal and Compliance Professionals
When facing FTC enforcement actions, small businesses need experienced legal representation familiar with Safeguards Rule requirements and enforcement procedures. Early engagement with qualified attorneys can significantly improve outcomes.
Legal support considerations:
• Experience with FTC enforcement and financial services compliance
• Understanding of small business operational constraints and resources
• Ability to negotiate reasonable compliance agreements and timelines
• Support for developing and implementing compliance improvement plans
Conclusion
The FTC Safeguards Rule represents a fundamental shift in how small businesses must approach cybersecurity and customer data protection. While the requirements may seem daunting, they’re designed to protect both businesses and consumers from the growing threat of cybercrime.
Success with the FTC Safeguards Rule compliance requires more than just implementing security tools – it demands a comprehensive approach that includes written policies, regular risk assessments, employee training, vendor oversight, and ongoing monitoring. Most small businesses find that partnering with experienced managed IT providers offers the most practical path to achieving and maintaining compliance.
The cost of compliance is high, but the cost of non-compliance is far greater. Beyond potential FTC penalties, businesses face risks including data breaches, customer lawsuits, reputation damage, and operational disruption. Investing in proper compliance measures provides essential peace of mind and protects your business’s long-term viability.
Don’t wait for an enforcement action or security incident to address your compliance obligations. Start with a comprehensive assessment of your current security posture and develop a realistic timeline for achieving full compliance. Remember, the goal isn’t just meeting minimum requirements – it’s building a robust security program that protects your customers and your business.
Ready to ensure your business meets the FTC Safeguards Rule requirements? Contact AlphaCIS for a comprehensive compliance assessment and learn how our personalized service and industry expertise can eliminate your IT headaches while keeping you secure and compliant.
FAQ
Q: How do I know if my small business is covered by the FTC Safeguards Rule?
A: You’re covered if your business is “significantly engaged” in financial activities, including tax preparation, insurance sales, auto financing, mortgage services, investment advice, or credit counseling. The rule applies regardless of business size.
Q: What are the penalties for non-compliance with the Safeguards Rule?
A: The FTC can impose civil penalties up to $46,517 per violation per day, along with cease and desist orders, compliance monitoring, and other enforcement actions. Penalties can quickly become financially devastating for small businesses.
Q: Can I use templates or generic policies to meet the written program requirement?
A: No, your written information security program must be tailored to your specific business operations, risks, and technology systems. Generic templates don’t meet the rule’s requirements for comprehensive, business-specific security programs.
Q: How often must I conduct risk assessments?
A: The rule requires regular risk assessments but doesn’t specify exact timing. Most compliance experts recommend annual comprehensive assessments with quarterly reviews and immediate assessments after significant business or technology changes.
Q: Am I responsible for my vendors’ compliance with the Safeguards Rule?
A: Yes, you must ensure that any vendor with access to customer information implements appropriate safeguards. This includes conducting due diligence, requiring contractual security commitments, and ongoing monitoring of vendor practices.
Q: What constitutes “customer information” under the rule?
A: Customer information includes any personally identifiable financial information, such as names with account numbers, Social Security numbers, credit information, income data, or any information collected in connection with providing financial services.
Q: Do I need multi-factor authentication for all business systems?
A: Multi-factor authentication is required for any information system that maintains customer information. This includes computers, servers, cloud applications, and mobile devices used to access or store customer data.
Q: How quickly must I report security incidents to customers and regulators?
A: The Safeguards Rule doesn’t specify notification timing, but you must have written incident response procedures. State breach notification laws may require customer notification within specific timeframes, typically 30-90 days.
Q: Can small businesses get extensions or exemptions from Safeguards Rule requirements?
A: No, there are no size-based exemptions or extensions. All covered businesses must comply with the full requirements regardless of size, resources, or operational complexity.
Q: What’s the difference between the FTC Safeguards Rule and state data protection laws?
A: The FTC Safeguards Rule specifically applies to financial institutions and focuses on customer financial information. You may also be subject to state data breach notification laws and industry-specific regulations that have additional or different requirements.
Q: How can I verify that my current security measures meet Safeguards Rule requirements?
A: Conduct a comprehensive compliance assessment comparing your current practices against the six core requirements. Most small businesses benefit from professional compliance audits to identify gaps and develop improvement plans.
Q: What should I do if I discover my business should have been complying but hasn’t been?
A: Immediately begin implementing compliance measures, starting with the most critical requirements like access controls and encryption. Document your compliance efforts and consider working with legal counsel if you’ve experienced any security incidents.
FTC Safeguards Rule Compliance Checker
Assess your small business compliance with FTC data security requirements
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity



