Article Summary
• Who this is for: Manufacturing companies, industrial facilities, OT/SCADA managers, plant operators, and IT leaders responsible for securing air-gapped or isolated operational environments.
• The challenge: Many organizations still believe physical isolation is enough to protect critical systems, but modern cyber threats now bypass air gaps through USB devices, insider threats, vendor access, and supply chain compromises. This creates major risks, including ransomware, operational downtime, production disruption, compliance violations, and intellectual property theft.
• Key insights covered:
- Air gaps alone no longer provide reliable protection against modern attack methods like infected USBs, compromised vendors, and insider threats.
- Legacy OT systems were not designed for today’s cybersecurity threats and often lack visibility, authentication, and monitoring capabilities.
- Zero Trust, network segmentation, device control, and continuous OT monitoring provide stronger, layered protection than traditional isolation.
- Real-world attacks like Stuxnet and power grid breaches prove that isolated environments are still highly vulnerable when operational processes and human factors are exploited.
- A modern OT security strategy must combine proactive monitoring, access controls, vendor management, and incident response planning to reduce risk.
• Your outcome: Readers will understand why traditional air-gap strategies fail in modern industrial environments and gain a practical roadmap for implementing layered OT cybersecurity controls that reduce operational risk, improve compliance, and protect critical systems from costly cyber incidents.
Quick Answer
Air-gapped systems are no longer safe because modern attackers have developed sophisticated methods to breach physical isolation barriers. While these systems remain disconnected from networks, cybercriminals now exploit USB devices, insider threats, compromised vendor access, and supply chain vulnerabilities to infiltrate supposedly secure environments. Manufacturing and industrial facilities relying solely on air gaps for protection face significant air-gapped systems cybersecurity risks that traditional isolation cannot address.
Key Takeaways
• Air gaps create false security – Physical isolation doesn’t stop determined attackers with modern techniques
• USB devices are attack highways – Infected removable media easily bypass air-gap protections
• Insider threats exploit trust – Malicious or compromised employees can introduce threats directly
• Vendor access creates vulnerabilities – Maintenance and support activities open attack windows
• Supply chain compromises happen early – Malware can be embedded before systems reach your facility
• Legacy OT systems lack defenses – Older industrial equipment wasn’t designed for modern threats
• Layered security is essential – Network segmentation, device control, and monitoring provide better protection
• Zero trust principles apply – Verify everything, even in “isolated” environments
• Continuous monitoring detects breaches – Real-time visibility catches attacks that bypass air gaps
• Proactive solutions prevent incidents – Modern OT security requires active defense, not passive isolation
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
What Are Air-Gapped Systems and Why Were They Considered Secure?
Air-gapped systems are completely isolated from external networks, including the internet and internal corporate networks. These systems have no physical or wireless connection to other networks, creating what was once considered an impenetrable security barrier.
Manufacturing facilities, power plants, and critical infrastructure have relied on air gaps for decades. The logic seemed bulletproof: if there’s no network connection, hackers can’t reach your systems remotely. This approach worked well when cyber threats were primarily network-based and industrial systems rarely needed external connectivity.
Traditional air-gap security assumed three things:
- Physical isolation prevents remote attacks
- Limited access points reduce the attack surface
- Operational technology (OT) environments remain separate from IT networks
However, this security model was built for a simpler time. Modern air-gapped systems’ cybersecurity risks have evolved far beyond what physical isolation can address, making this approach dangerously outdated for today’s threat landscape.
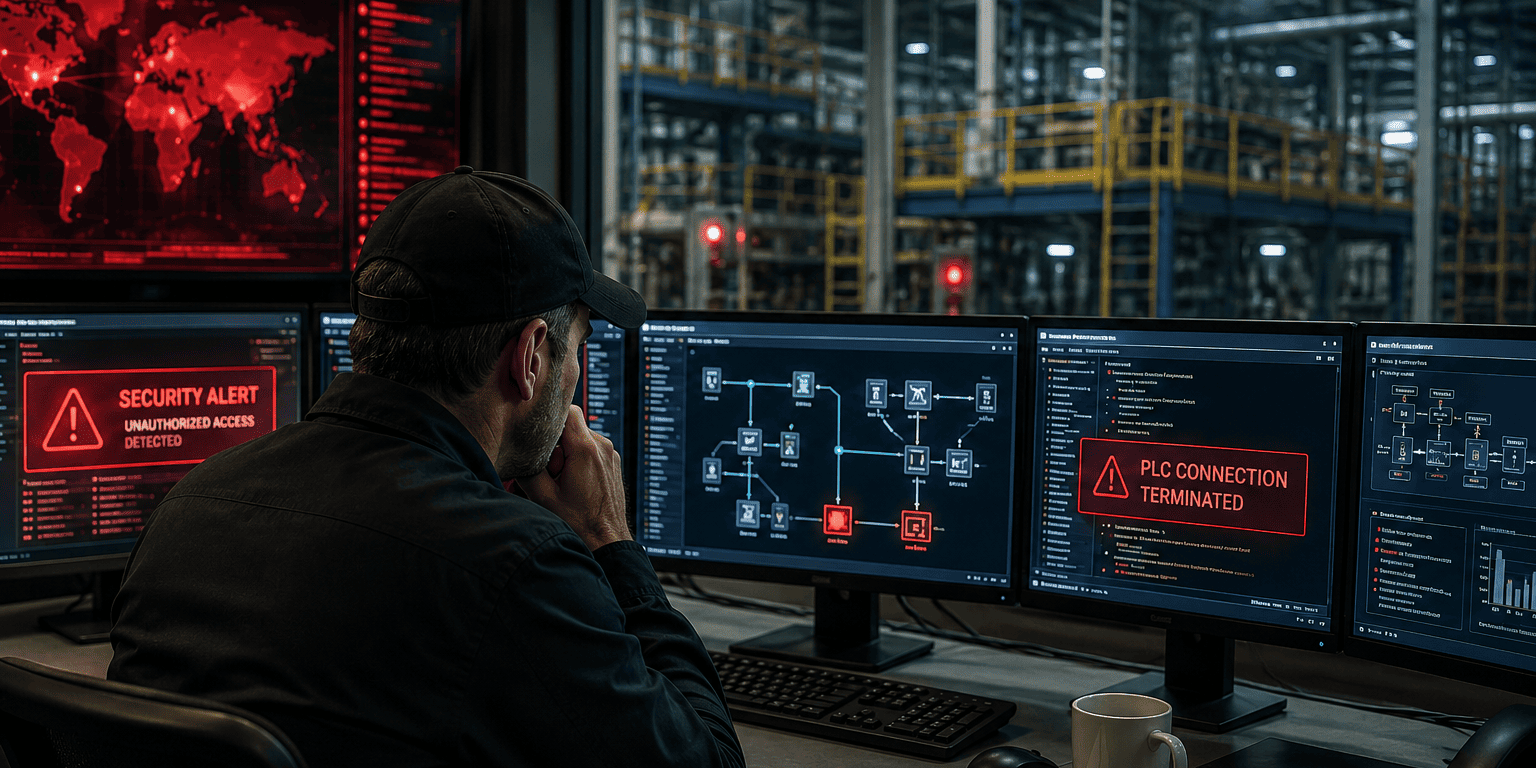
How Modern Attackers Bypass Air-Gapped Protection
The reality is that determined attackers have developed multiple methods to breach air-gapped systems. These techniques don’t require network access; they exploit the human and physical elements that air gaps can’t eliminate.
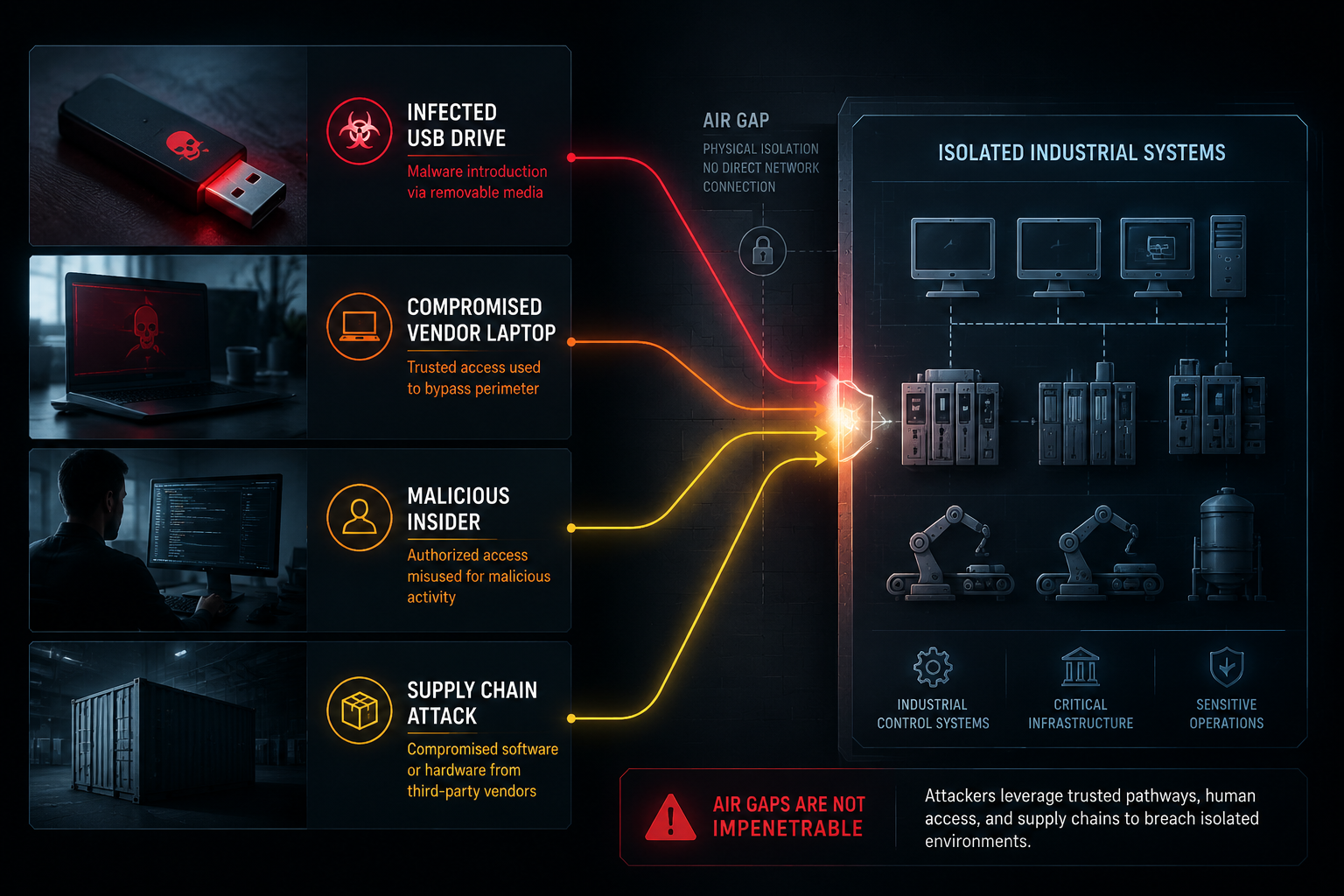
Infected USB Devices: The Digital Trojan Horse
USB devices and removable media represent the most common attack vector against air-gapped systems. Attackers deliberately leave infected USB drives in parking lots, lobbies, or mail them directly to targets, knowing that curious employees often plug them into secure systems.
Here’s how USB attacks work:
- Malware lies dormant on the device until inserted
- Autorun features automatically execute malicious code
- Once inside, malware can spread to other connected systems
- Data can be exfiltrated when the USB is later connected to networked systems
The infamous Stuxnet attack used this exact method to infiltrate Iran’s nuclear facilities. Despite sophisticated air-gap protections, a simple USB device delivered the malware that ultimately destroyed centrifuges.
Insider Threats: When Trust Becomes Vulnerability
Malicious insiders or compromised employees pose significant risks to air-gapped environments. These individuals already have authorized access, making their actions difficult to detect and prevent.
Insider threats include:
- Disgruntled employees seeking revenge or financial gain
- Compromised personnel coerced or bribed by external attackers
- Unintentional insiders who unknowingly introduce threats
- Contractor personnel with temporary access but unclear loyalties
Unlike external attackers, insiders understand your systems, security procedures, and valuable assets. They can introduce malware, steal data, or sabotage operations while appearing to perform legitimate activities.
Compromised Vendor Access: Trusted Partners as Attack Vectors
Maintenance personnel, system integrators, and technology vendors often require access to air-gapped systems for updates, repairs, and support. These legitimate business relationships create opportunities for attackers to exploit trusted access channels.
Vendor-related risks include:
- Compromised vendor employees carrying malware
- Infected maintenance laptops and diagnostic tools
- Malicious software updates or patches
- Social engineering targeting vendor personnel
- Weak security practices at vendor organizations
Attackers increasingly target smaller vendors and service providers because they typically have weaker security but trusted access to larger, more secure organizations.
Supply Chain Compromises: Threats Built-In from Day One
The most sophisticated attacks begin before systems even reach your facility. Attackers compromise hardware or software during manufacturing, shipping, or installation, embedding malware that activates later.
Supply chain attack methods:
- Malicious firmware embedded in industrial components
- Compromised software installed during system setup
- Hardware modifications during shipping or storage
- Infected installation media or documentation
- Backdoors built into legitimate software updates
These attacks are particularly dangerous because they bypass all perimeter security and appear as legitimate system behavior, making detection extremely difficult.
Real-World Examples of Air-Gap Breaches in Industrial Environments
The theoretical risks of air-gapped systems have become harsh realities for numerous organizations. These real-world incidents demonstrate how attackers successfully breach supposedly secure environments.

Stuxnet: The Wake-Up Call for Industrial Security
The Stuxnet attack remains the most famous example of air-gap bypass. This sophisticated malware targeted Iran’s nuclear enrichment facilities, which were protected by multiple air gaps and extensive physical security.
Key attack elements:
- Multiple USB-based infection vectors
- Four zero-day exploits for Windows systems
- Stolen digital certificates for legitimacy
- Specific targeting of Siemens industrial controllers
- Physical destruction of centrifuge equipment
Despite having no network connections, the facility’s systems were completely compromised. The attack succeeded because it exploited the human and physical elements that air gaps cannot protect against.
Ukrainian Power Grid: Coordinated Infrastructure Attack
In 2015 and 2016, attackers successfully disrupted Ukraine’s power grid multiple times. These attacks combined social engineering, spear-phishing, and eventual access to supposedly isolated control systems.
Attack progression:
- Initial compromise through spear-phishing emails
- Lateral movement to reach air-gapped OT networks
- Direct manipulation of industrial control systems
- Coordinated attacks on multiple facilities simultaneously
- Extended power outages are affecting hundreds of thousands
The attackers demonstrated that air gaps provide little protection when adversaries are patient, well-resourced, and willing to use multiple attack vectors over extended periods.
Manufacturing Sector Incidents
Numerous manufacturing companies have experienced breaches of air-gapped production systems, though many incidents remain unreported due to competitive concerns and regulatory requirements.
Common attack patterns include:
- Ransomware delivered via infected USB devices
- Production data theft through compromised maintenance systems
- Sabotage of quality control systems
- Intellectual property theft from isolated design systems
- Safety system manipulation in chemical and pharmaceutical plants
These incidents often result in production shutdowns, quality issues, regulatory violations, and significant financial losses that far exceed the cost of proper cybersecurity measures.
Why “Isolated” No Longer Means “Secure” in 2026
The fundamental assumption behind air-gapped security – that physical isolation prevents cyber attacks – no longer holds in our interconnected world. Several factors have rendered traditional air gaps inadequate for modern threat protection.
Legacy Systems Lack Modern Security Features
Most industrial control systems and OT equipment were designed decades ago when cybersecurity wasn’t a primary concern. These legacy systems have inherent vulnerabilities that air gaps cannot address:
- No built-in security controls like encryption or authentication
- Unpatched operating systems that cannot be easily updated
- Default passwords that are rarely changed
- Weak access controls with shared administrative accounts
- No activity logging or security monitoring capabilities
When attackers breach the air gap through other means, these systems offer little resistance to compromise or detection capabilities for ongoing attacks.
Operational Requirements Compromise Isolation
Modern manufacturing and industrial operations increasingly require connectivity that undermines true air-gap isolation:
- Remote monitoring for predictive maintenance and efficiency
- Data collection for quality control and regulatory compliance
- Software updates for security patches and feature improvements
- Vendor support requiring remote diagnostic access
- Integration requirements with enterprise systems for reporting
Organizations often implement “air gaps” that aren’t truly isolated, creating security vulnerabilities while maintaining a false sense of protection.
Human Factors Create Persistent Vulnerabilities
Air gaps cannot eliminate the human elements that attackers routinely exploit:
- Convenience trumps security when air gaps interfere with daily operations
- Social engineering targets personnel with system access
- Insider threats exploit legitimate access for malicious purposes
- Training gaps leave employees unprepared for modern attack methods
- Process violations occur when security procedures conflict with operational needs
The most sophisticated technical controls fail when human factors aren’t properly addressed through training, procedures, and cultural change.
Modern Protection Strategies for Air-Gapped Systems: Cybersecurity Risks
Protecting industrial and OT environments in 2026 requires moving beyond simple air gaps to implement layered security strategies. These modern approaches provide better protection while maintaining operational efficiency and supporting legitimate business requirements.

Network Segmentation: Smart Isolation
Rather than complete isolation, network segmentation creates controlled boundaries between different system zones while enabling necessary connectivity. This approach provides security benefits without operational limitations.
Effective segmentation strategies:
- Zone-based architecture separating OT networks by function and risk level
- Firewalls and access controls manage traffic between network segments
- Demilitarized zones (DMZs) for systems requiring both OT and IT connectivity
- Unidirectional gateways allow data flow without return communication paths
- Micro-segmentation isolates individual devices and applications
Proper segmentation provides the security benefits of air gaps while supporting modern operational requirements like remote monitoring and data analytics.
Zero Trust Principles for OT Environments
Zero trust security assumes that no user, device, or network segment should be automatically trusted, even within supposedly secure environments. This approach is particularly valuable for protecting against insider threats and compromised credentials.
Zero trust implementation includes:
- Identity verification for all users and devices before granting access
- Least privilege access, providing only the minimum permissions required
- Continuous monitoring of user and device behavior for anomalies
- Multi-factor authentication for all administrative and remote access
- Regular access reviews to ensure permissions remain appropriate
Zero trust principles help organizations detect and prevent attacks that bypass traditional perimeter security, including air gaps.
Device Control and USB Security
Since USB devices represent a primary attack vector against air-gapped systems, implementing strong device controls is essential for modern OT security.
Device control measures:
- USB port blocking or physical removal was not required
- Whitelisting approved devices with centralized management
- Automatic scanning of all removable media before use
- Encrypted USB devices for authorized data transfers
- Air-gapped scanning stations for checking external media safely
These controls significantly reduce air-gapped systems’ cybersecurity risks while still supporting legitimate operational requirements for data transfer and system maintenance.
Continuous OT Monitoring and Threat Detection
Traditional air gaps provide no visibility into what’s happening inside supposedly secure environments. Modern OT security requires continuous monitoring to detect attacks that bypass perimeter controls.
Monitoring capabilities include:
- Network traffic analysis to identify unusual communication patterns
- Device behavior monitoring for signs of compromise or malfunction
- Process monitoring to detect unauthorized changes to industrial systems
- File integrity monitoring for critical system and configuration files
- User activity monitoring to identify suspicious or unauthorized actions
Continuous monitoring provides the visibility needed to detect and respond to attacks quickly, minimizing potential damage and operational disruption.
Building Layered OT Security Architecture
No single security control can protect against all modern threats. Effective OT security requires multiple overlapping layers that provide defense in depth against various attack vectors.
Essential security layers:
- Physical security controls access to facilities and equipment
- Network security with firewalls, segmentation, and access controls
- Endpoint security protects individual devices and systems
- Application security, securing industrial software and databases
- Data security protects sensitive information at rest and in transit
- Identity security, managing user accounts, and access permissions
- Monitoring and response, providing visibility and incident response capabilities
This layered approach ensures that if attackers bypass one security control, additional layers provide continued protection and detection capabilities.
Air-Gapped Systems Security Risk Assessment
Evaluate your current air-gap security posture and identify potential vulnerabilities
1. How do you handle USB devices and removable media?
2. What level of vendor/contractor access do you allow?
3. How do you monitor activity on air-gapped systems?
4. What's your approach to system updates and patches?
5. How do you manage user access and authentication?
6. What security training do personnel receive?
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free ConsultationPractical Steps for Addressing Air-Gapped Systems Cybersecurity Risks
Moving from traditional air gaps to modern OT security requires a systematic approach that balances security improvements with operational requirements. Here’s how to get started:
Immediate Actions You Can Take Today
Assess your current environment:
- Document all systems currently protected by air gaps
- Identify actual connectivity requirements and data flows
- Evaluate existing security controls and monitoring capabilities
- Review vendor access procedures and security requirements
Implement quick wins:
- Disable unnecessary USB ports or implement device controls
- Change default passwords on all industrial systems
- Establish procedures for scanning removable media
- Train personnel on social engineering and insider threat awareness
Medium-Term Security Improvements
Enhance network architecture:
- Implement network segmentation to replace complete air gaps
- Deploy firewalls and access controls between network zones
- Establish secure remote access solutions for vendor support
- Create monitoring capabilities for network traffic and device behavior
Strengthen access controls:
- Implement multi-factor authentication for administrative access
- Establish least privilege access principles for all users
- Create regular access reviews and permission audits
- Develop incident response procedures for security events
Long-Term Strategic Security Planning
Build a comprehensive OT security program:
- Develop security policies and procedures specific to OT environments
- Establish security awareness training for all personnel
- Create vendor security requirements and assessment processes
- Implement continuous monitoring and threat detection capabilities
Plan for ongoing improvement:
- Regular security assessments and penetration testing
- Stay current with emerging threats and attack techniques
- Participate in industry security information sharing
- Maintain relationships with cybersecurity experts and consultants
FAQ: Air-Gapped Systems Cybersecurity Risks
Q: Are air gaps completely useless for security?
A: Air gaps still provide some protection against automated attacks and casual hackers, but they’re insufficient against determined adversaries with modern attack techniques. They should be part of a layered security strategy, not the only protection.
Q: How can I tell if my air-gapped system has been compromised?
A: Look for unusual system behavior, unexpected network traffic, new files or processes, performance changes, or unauthorized configuration modifications. Implement monitoring tools to detect these indicators automatically.
Q: What’s the biggest risk to air-gapped systems in manufacturing?
A: USB devices and removable media represent the highest risk, followed by insider threats and compromised vendor access. These attack vectors bypass the air gap entirely.
Q: Should we eliminate air gaps?
A: Not necessarily. Replace complete isolation with network segmentation that provides controlled connectivity. This maintains security benefits while supporting operational requirements.
Q: How much does modern OT security cost compared to air gaps?
A: Initial implementation costs more than simple air gaps, but modern security provides better protection and supports business requirements. The cost of a successful attack usually far exceeds security investment.
Q: Can we keep some systems completely air-gapped?
A: Yes, for the most critical systems that truly don’t require any connectivity. However, ensure these systems have other security controls like device restrictions and monitoring.
Q: What should we do about legacy systems that can’t be updated?
A: Implement additional network controls, monitoring, and access restrictions around legacy systems. Consider replacement planning for systems that pose significant risks.
Q: How often should we review our OT security?
A: Conduct formal reviews annually, with continuous monitoring and quarterly assessments of high-risk areas. Update security measures as threats and business requirements evolve.
Q: What’s the first step in improving our OT security?
A: Start with a comprehensive assessment of your current environment, including all systems, connections, and security controls. This provides the foundation for improvement planning.
Q: Do we need specialized OT security expertise?
A: Yes, OT environments have unique requirements that differ from traditional IT security. Consider working with specialists who understand industrial systems and operational requirements.
Q: How do we balance security with operational efficiency?
A: Modern security approaches like network segmentation and zero trust can actually improve operational efficiency while enhancing security. The key is proper implementation that supports business processes.
Q: What regulations apply to OT security?
A: Various regulations apply depending on your industry, including NERC CIP for power, FDA for pharmaceuticals, and general frameworks like NIST. Consult with compliance experts for your specific situation.
Conclusion: Moving Beyond Air Gaps to Real Security
The harsh reality is that air-gapped systems are no longer safe in 2026. While physical isolation once provided adequate protection, modern attackers have developed sophisticated methods to breach these supposedly secure environments. Air-gapped systems cybersecurity risks now include USB-based malware, insider threats, compromised vendors, and supply chain attacks that bypass traditional isolation entirely.
The good news is that better alternatives exist. Modern OT security approaches like network segmentation, zero trust principles, and continuous monitoring provide superior protection while supporting legitimate business requirements. These strategies acknowledge that perfect isolation is neither possible nor necessary – what matters is implementing the right controls to detect and prevent attacks.
Your next steps should focus on:
- Assessing your current air-gapped systems and their actual security posture
- Identifying operational requirements that air gaps prevent you from meeting
- Implementing layered security controls that provide better protection
- Establishing monitoring and response capabilities for ongoing threat detection
Don’t let outdated security assumptions put your operations at risk. The cost of a successful attack – including production shutdowns, regulatory violations, and reputation damage – far exceeds the investment in modern security measures.
Ready to move beyond air gaps to real security? Our team specializes in helping manufacturing and industrial organizations implement modern OT security that provides peace of mind without operational disruption. We offer same-day support and 24/7 monitoring to ensure your critical systems stay protected and operational.
Contact us today for a comprehensive OT security assessment. Our industry expertise and proactive solutions will help you eliminate IT headaches while building the secure and compliant infrastructure your business needs to thrive.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity