Article Summary
• Who this is for: Manufacturing companies, plant managers, OT/IT leaders, and industrial operations teams that rely on PLCs, SCADA systems, and connected production environments to keep operations running.
• The challenge: Cybercriminals are exploiting weak IT-to-OT segmentation, remote access tools, default credentials, and outdated PLC firmware to infiltrate production environments, causing downtime, ransomware incidents, operational disruption, and safety risks.
• Key insights covered:
- Most PLC attacks start with phishing and lateral movement through poorly segmented IT/OT networks.
- Remote vendor access, shared credentials, and unpatched legacy systems create major entry points for attackers.
- Attackers increasingly use subtle process manipulation, not just ransomware, to damage production quality and operations over time.
- Effective defense requires OT-specific monitoring, network segmentation, access control, and collaboration between IT and OT teams.
- Manufacturers need security strategies designed specifically for industrial environments, not traditional IT-only cybersecurity approaches.
• Your outcome: Gain a clear understanding of how modern PLC attacks happen, identify where your manufacturing environment is vulnerable, and learn the practical steps needed to reduce operational risk, prevent costly downtime, and strengthen industrial cybersecurity resilience.
Quick Answer
Hackers typically access PLCs through a multi-step process that starts with compromising corporate IT networks via phishing emails, then pivoting to operational technology (OT) systems where PLCs operate with minimal security. Once inside, attackers can manipulate production parameters, trigger safety shutdowns, or deploy ransomware to halt operations entirely. The key vulnerability lies in the convergence of IT and OT networks without proper segmentation and monitoring.
Key Takeaways
• Phishing remains the primary entry point – 90% of successful PLC attacks begin with email-based social engineering targeting IT staff
• Network convergence creates risk – Modern manufacturing connects OT systems to corporate networks, expanding attack surfaces
• Default credentials are common – Many PLCs still use factory-default passwords that attackers easily exploit
• Remote access tools become backdoors – Vendor remote maintenance systems often lack proper security controls
• Legacy systems lack security – Older PLCs weren’t designed with cybersecurity in mind and can’t be easily updated
• Production impact is immediate – Successful PLC compromise can halt operations within minutes
• Segmentation is critical – Proper network isolation between IT and OT systems prevents lateral movement
• Monitoring OT traffic reveals threats – Unusual PLC communications often indicate ongoing attacks
• Patch management differs from IT – OT systems require specialized update procedures to avoid downtime
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation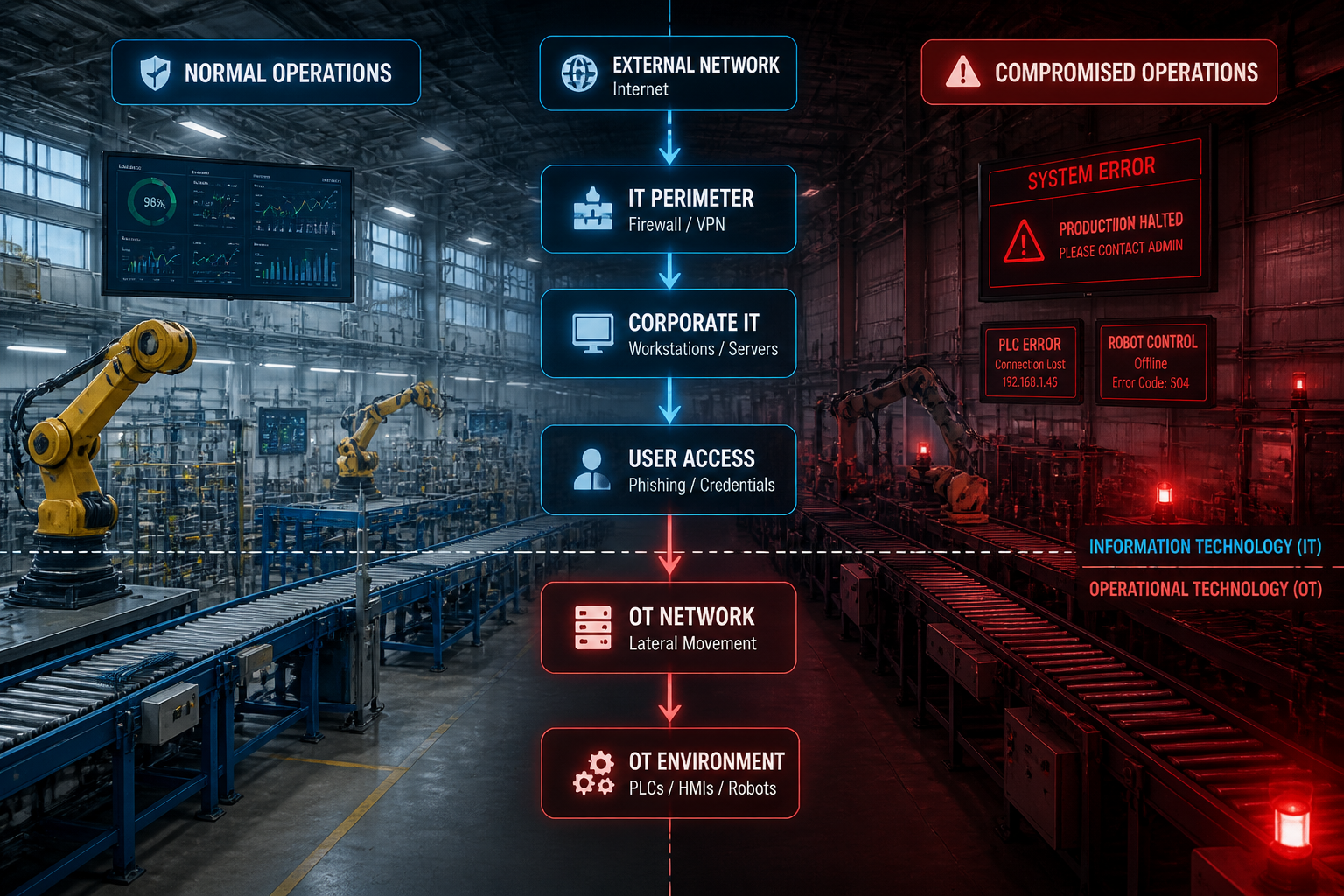
Why PLCs Have Become High-Value Targets for Cybercriminals
Programmable Logic Controllers represent the heart of modern manufacturing operations. These industrial computers control everything from assembly line speeds to safety systems, making them incredibly valuable targets for cybercriminals seeking maximum disruption.
The shift toward Industry 4.0 has connected previously isolated OT systems to corporate networks and the internet. This connectivity brings operational benefits like remote monitoring and predictive maintenance, but it also creates new pathways for attackers to reach critical production systems.
The business impact makes PLCs attractive targets:
• Immediate operational disruption – Stopping production lines costs manufacturers thousands of dollars per minute
• Ransom potential – Companies often pay quickly to restore operations and avoid extended downtime
• Safety implications – Manipulating safety systems can create dangerous conditions requiring immediate response
• Competitive advantage – Industrial espionage through PLC access can reveal proprietary processes
• Supply chain effects – Shutting down key suppliers can impact entire industries
Manufacturing companies face a perfect storm of vulnerabilities. Legacy PLC systems designed for reliability rather than security now connect to networks that extend far beyond the factory floor. Many organizations lack visibility into their OT environments, making it difficult to detect threats until production stops.
The financial motivation for attackers continues to grow. A successful ransomware attack on a major manufacturer can generate millions in ransom payments, while the technical barriers to entry keep decreasing as attack tools become more sophisticated and accessible.
How Attackers Think About Industrial Systems
Understanding how hackers access PLCs requires thinking like an attacker. Cybercriminals approach industrial targets differently than traditional IT environments, focusing on operational disruption rather than data theft.
Attackers follow a logical progression when targeting manufacturing systems:
First, they research the target company to identify technologies, suppliers, and personnel. Public information like job postings, vendor relationships, and industry publications reveals valuable details about industrial systems and network architecture.
Next, they map potential entry points. Rather than attacking PLCs directly, sophisticated attackers target the easier-to-compromise IT infrastructure that connects to OT systems. Email systems, VPN servers, and employee workstations provide initial access with familiar attack techniques.
The attacker mindset prioritizes:
• Path of least resistance – Why attack hardened PLCs when you can compromise a user’s laptop first?
• Operational knowledge – Understanding industrial processes helps attackers cause maximum disruption
• Timing considerations – Attacks during peak production or critical deadlines increase pressure to pay ransoms
• Multiple objectives – Combining data theft, operational disruption, and ransom demands maximizes profit
Attackers also understand that manufacturing environments have unique constraints. OT systems can’t be easily taken offline for security updates, creating persistent vulnerabilities. Emergency response procedures often prioritize safety over security, giving attackers windows of opportunity during crises.
The human element remains crucial. Social engineering attacks targeting OT personnel often succeed because these employees focus on operational reliability rather than cybersecurity threats. Attackers exploit this mindset by crafting attacks that appear to address operational concerns.
Common Attack Vectors: How Hackers Access PLCs
Phishing Attacks Leading to IT Network Compromise
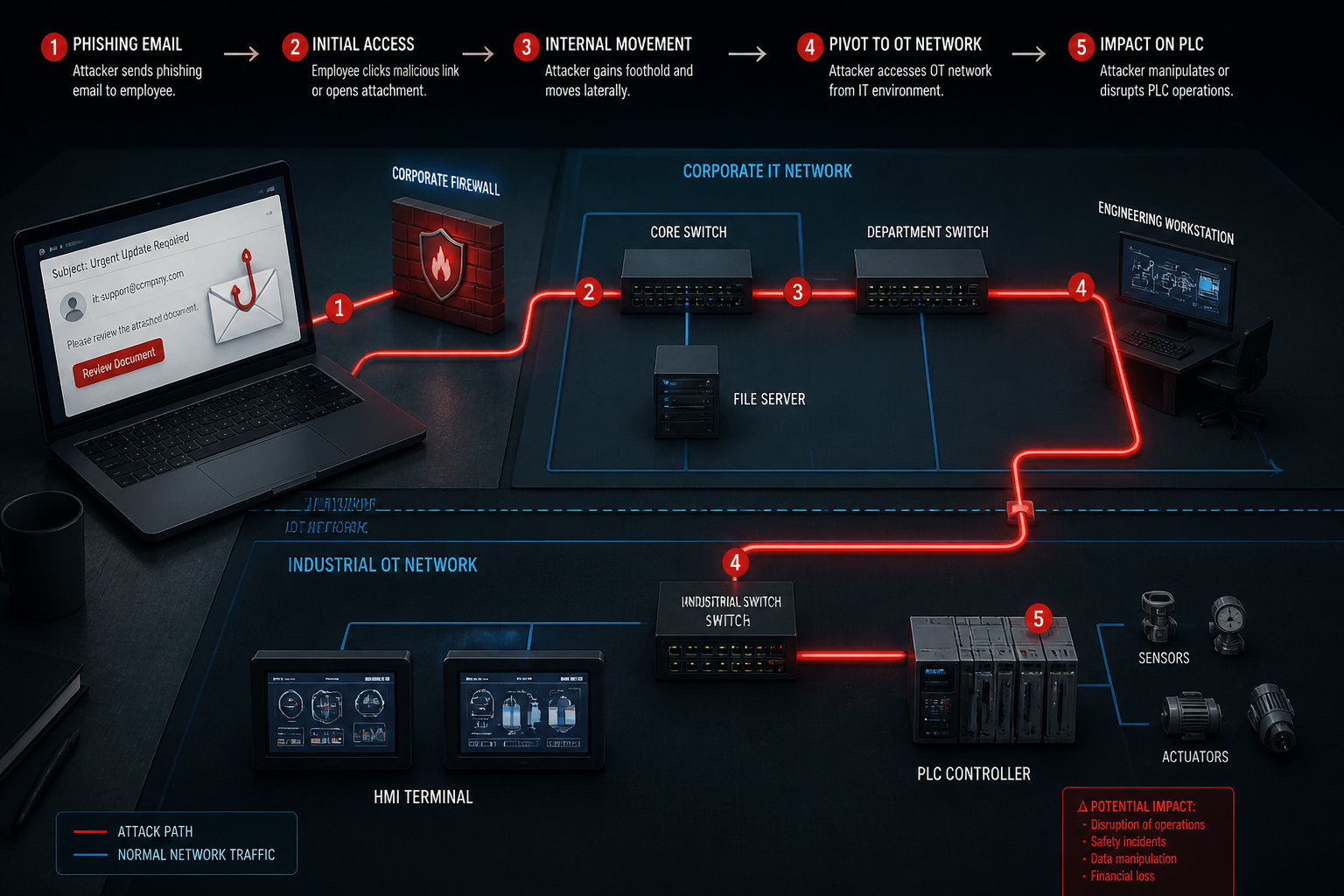
Email-based phishing remains the most common initial attack vector against manufacturing companies. Attackers craft convincing messages targeting employees with access to both IT and OT systems, often impersonating suppliers, customers, or industry organizations.
Successful phishing campaigns against manufacturers typically:
• Target engineering staff – These employees often have elevated access to both corporate systems and production networks
• Reference current projects – Attackers research ongoing initiatives to make emails appear legitimate and urgent
• Include industrial-themed malware – Payloads designed specifically for manufacturing environments increase success rates
• Exploit operational urgency – Messages claiming production issues or safety concerns bypass normal security awareness
Once attackers gain initial access through phishing, they begin reconnaissance to map the network and identify pathways to OT systems. This lateral movement phase can take weeks or months as attackers carefully avoid detection while expanding their access.
The convergence of IT and OT networks provides the bridge attackers need. Many organizations connect these environments for legitimate business purposes like production reporting, inventory management, and remote monitoring. However, inadequate segmentation allows attackers to pivot from compromised IT systems directly to PLC networks.
Remote Access System Vulnerabilities
Remote access solutions designed for vendor support and maintenance create significant security risks when improperly configured. These systems often provide direct pathways to PLC networks, bypassing traditional IT security controls.
Common remote access vulnerabilities include:
• Persistent VPN connections – Always-on vendor access creates permanent entry points for attackers
• Shared credentials – Multiple vendors using the same login credentials increases exposure risk
• Unmonitored sessions – Lack of logging makes it difficult to detect unauthorized access
• Outdated software – Remote access tools often lag behind security updates
Attackers specifically target these remote access systems because they provide legitimate-looking pathways to industrial networks. Compromising a vendor’s systems can grant access to multiple customer environments simultaneously.
The challenge for manufacturers lies in balancing operational needs with security requirements. Vendors require remote access for troubleshooting, updates, and preventive maintenance. However, each connection represents a potential attack vector that requires careful management and monitoring.
Unpatched Firmware and Default Credentials
Legacy PLC systems present significant security challenges due to outdated firmware and factory-default configurations. Many industrial systems operate for decades without security updates, creating persistent vulnerabilities that attackers can easily exploit.
Firmware-related attack vectors include:
• Known vulnerabilities – Public databases list security flaws in specific PLC models and firmware versions
• Buffer overflow exploits – Attackers can crash or control PLCs by sending malformed network packets
• Protocol weaknesses – Industrial communication protocols often lack encryption or authentication
• Default passwords – Factory settings remain unchanged on many production systems
The patching challenge in OT environments differs significantly from traditional IT systems. Production systems can’t be easily taken offline for updates, and firmware changes risk disrupting carefully tuned industrial processes. This creates a security debt that accumulates over years of operation.
Attackers maintain databases of default credentials for industrial equipment from major manufacturers. Automated scanning tools can quickly identify vulnerable systems across internet-connected networks, making default password attacks a low-effort, high-success strategy.
USB and Insider Threat Vectors
Physical access to industrial systems creates additional attack opportunities that bypass network security controls entirely. USB-based attacks and malicious insiders represent significant threats to PLC security.
Physical attack methods include:
• Malicious USB devices – Infected drives can deploy malware when connected to engineering workstations or HMI terminals
• Rogue devices – Attackers may install unauthorized hardware to maintain persistent access
• Social engineering – Impersonating vendors or contractors to gain facility access
• Insider threats – Disgruntled employees with legitimate access can cause immediate damage
The Stuxnet attack demonstrated the effectiveness of USB-based delivery methods for industrial malware. Even air-gapped systems remain vulnerable to physical attacks that don’t require network connectivity.
Manufacturing environments often have less stringent physical security than corporate offices. Production floors, maintenance areas, and vendor spaces may lack adequate access controls, creating opportunities for attackers to interact directly with industrial systems.
PLC Security Risk Assessment
Evaluate your industrial control system vulnerabilities
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free ConsultationReal-World Attack Scenario: Step-by-Step PLC Compromise

Understanding how hackers access PLCs becomes clearer through a realistic attack scenario. This example demonstrates how attackers combine multiple techniques to achieve their objectives while avoiding detection.
Phase 1: Initial Reconnaissance and Access
The attack begins months before any systems are compromised. Attackers research MidState Manufacturing, an automotive parts supplier, through public sources including LinkedIn profiles, job postings, and industry publications. They identify key personnel, technology vendors, and operational details.
Initial intelligence gathering reveals:
• Engineering manager John Smith frequently posts about Siemens PLC projects on LinkedIn
• Recent job posting seeks “Rockwell Automation specialist,” indicating PLC vendor preferences
• Company website mentions a 24/7 production schedule, suggesting high downtime costs
• Vendor directory lists multiple industrial automation suppliers with remote access needs
Armed with this information, attackers craft a targeted phishing email to John Smith. The message appears to come from Siemens technical support, referencing a “critical firmware vulnerability” affecting his specific PLC model. The email includes a malicious PDF attachment disguised as a security bulletin.
When John opens the attachment on his engineering workstation, malware installs silently in the background. The initial payload establishes a command-and-control connection while remaining dormant to avoid detection by antivirus software.
Phase 2: Network Mapping and Lateral Movement
Over the following weeks, attackers use their foothold on John’s workstation to map the internal network. They discover that engineering systems connect to both the corporate domain and the production network through a poorly configured firewall.
Network reconnaissance reveals:
• Engineering workstations have dual network connections to IT and OT environments
• PLC programming software stores connection credentials in plaintext configuration files
• Remote access VPN allows vendor connections directly to the production network
• Network monitoring focuses on IT systems, leaving OT traffic largely unmonitored
Attackers extract PLC connection credentials from the engineering software and identify active industrial systems. They also add additional workstations to establish multiple access points and reduce the risk of losing access if one system is compromised.
The lateral movement phase proceeds slowly and carefully. Attackers avoid actions that might trigger security alerts or disrupt operations, instead focusing on gathering intelligence about production processes and system configurations.
Phase 3: PLC Access and Control
With network access and valid credentials, attackers connect directly to the production PLCs controlling the main assembly line. Initial access uses legitimate engineering tools and protocols, making the connection appear normal to any monitoring systems.
Once connected to PLCs, attackers can:
• Read current production parameters – Understanding normal operations helps plan disruptive changes
• Modify control logic – Altering PLC programs can cause equipment malfunctions or quality issues
• Manipulate safety systems – Disabling or triggering safety interlocks creates dangerous conditions
• Install persistent backdoors – Modified firmware ensures continued access even after discovery
The attackers choose to modify temperature control parameters for the paint curing process. By gradually increasing temperatures over several days, they cause quality defects that aren’t immediately obvious but will result in customer complaints and potential recalls.
This subtle approach maximizes damage while delaying detection. Unlike ransomware that immediately announces its presence, process manipulation can continue for weeks before anyone realizes the system has been compromised.
Phase 4: Escalation and Ransom Demand
After establishing their ability to manipulate production systems, attackers prepare for the final phase of their operation. They deploy ransomware across both IT and OT networks simultaneously, encrypting critical systems and displaying ransom demands.
The coordinated attack affects:
• Corporate file servers and email systems
• Engineering workstations and PLC programming software
• HMI displays throughout the production facility
• Backup systems and recovery infrastructure
The ransom note threatens to permanently damage production equipment if payment isn’t received within 48 hours. Attackers demonstrate their control by triggering emergency shutdowns across multiple production lines, bringing operations to a complete halt.
MidState Manufacturing faces a critical decision: pay the ransom to restore operations quickly, or attempt recovery procedures that could take weeks while losing millions in production revenue.
What Happens After Attackers Gain PLC Access
Once hackers successfully access PLCs, they have numerous options for achieving their objectives. The specific actions depend on their motivation, technical capabilities, and understanding of the target’s industrial processes.
Immediate Production Shutdown
The most direct impact attackers can achieve is stopping production entirely. This approach maximizes pressure on the target organization while demonstrating the attacker’s control over critical systems.
Shutdown methods include:
• Emergency stop activation – Triggering safety systems designed to halt operations during emergencies
• Parameter manipulation – Changing setpoints to values that force automatic shutdowns
• Communication disruption – Blocking network traffic between PLCs and supervisory systems
• Logic modification – Altering control programs to create unsafe or unstable conditions
Production shutdowns create immediate financial pressure. Manufacturing companies lose revenue for every minute of downtime, with costs often reaching thousands of dollars per hour for complex production lines. This urgency frequently leads to quick ransom payments rather than lengthy recovery procedures.
The psychological impact on operations staff can be significant. Seeing critical systems respond to unauthorized commands undermines confidence in industrial control systems and may require extensive retraining and process validation before normal operations resume.
Subtle Process Manipulation
More sophisticated attackers may choose subtle manipulation over obvious disruption. This approach can cause long-term damage while avoiding immediate detection, potentially affecting product quality, equipment reliability, and customer relationships.
Subtle manipulation techniques:
• Quality parameter changes – Slightly altering specifications to cause defects that appear later in the supply chain
• Equipment stress – Operating machinery outside optimal parameters to accelerate wear and increase maintenance costs
• Efficiency reduction – Decreasing throughput in ways that appear to be normal operational variations
• Safety margin erosion – Reducing safety buffers without triggering immediate alarms
These attacks can continue for months before detection, causing cumulative damage that far exceeds the immediate impact of ransomware. Product recalls, equipment failures, and customer complaints create lasting business consequences that extend well beyond the initial attack.
The attribution challenge makes subtle attacks particularly dangerous. When quality issues or equipment problems develop gradually, organizations often attribute them to normal operational causes rather than cyber attacks.
Data Theft and Industrial Espionage
PLC access can provide valuable intellectual property beyond the immediate operational disruption. Industrial control systems contain detailed information about proprietary processes, production capabilities, and competitive advantages.
Valuable data accessible through PLCs:
• Process parameters – Temperature, pressure, timing, and chemical formulations that define product quality
• Production capacity – Actual throughput rates and efficiency metrics that competitors value highly
• Quality control procedures – Testing methods and acceptance criteria that ensure product compliance
• Maintenance schedules – Equipment reliability data that reveals operational strengths and weaknesses
This information has significant value in underground markets, particularly for state-sponsored attackers seeking to benefit domestic industries. The theft may go undetected for years, giving competitors sustained advantages in product development and pricing.
Prevention Strategies: Protecting PLCs from Cyber Attacks

Preventing PLC attacks requires a comprehensive approach that addresses both technical vulnerabilities and operational practices. Effective protection strategies must balance security requirements with the operational reliability that manufacturing depends on.
Network Segmentation and Access Control
Proper network segmentation creates the foundation for industrial cybersecurity by limiting how far attackers can move once they gain initial access. Effective segmentation isolates OT systems from corporate networks while maintaining necessary business connectivity.
Essential segmentation practices include:
• DMZ implementation – Creating buffer zones between IT and OT networks with strict firewall rules
• VLAN separation – Using virtual networks to isolate different types of industrial systems
• Unidirectional gateways – Allowing data to flow from OT to IT while blocking reverse connections
• Jump servers – Providing controlled access points for legitimate administrative activities
Access control mechanisms must account for the unique requirements of industrial environments. Unlike traditional IT systems, OT networks often require real-time communication with minimal latency. Security controls must preserve these performance characteristics while blocking unauthorized access.
Effective access control strategies:
• Role-based permissions – Limiting user access based on specific job functions and operational needs
• Multi-factor authentication – Requiring additional verification for access to critical systems
• Session monitoring – Logging and analyzing all interactions with industrial control systems
• Privileged access management – Controlling and auditing administrative activities
The key to successful segmentation lies in understanding legitimate business requirements before implementing security controls. Operations teams must remain able to perform their jobs effectively while security measures prevent unauthorized access.
Continuous OT Network Monitoring
Traditional IT security monitoring tools often can’t effectively monitor OT networks due to different protocols, communication patterns, and operational requirements. Specialized industrial cybersecurity solutions provide visibility into PLC communications and can detect threats that bypass conventional security tools.
Effective OT monitoring includes:
• Protocol analysis – Understanding normal industrial communication patterns to identify anomalies
• Asset discovery – Maintaining accurate inventories of all connected industrial devices
• Behavioral analysis – Detecting unusual activities that may indicate compromise or malfunction
• Integration capabilities – Connecting OT monitoring with existing IT security operations centers
Monitoring systems must operate passively to avoid disrupting industrial processes. Unlike IT networks, where active scanning and testing are common, OT environments require non-intrusive monitoring methods that don’t interfere with real-time operations.
Key monitoring capabilities:
• Real-time alerting – Immediate notification of suspicious activities or unauthorized changes
• Historical analysis – Long-term trending to identify gradual changes or emerging threats
• Compliance reporting – Documentation required for regulatory compliance and audit purposes
• Incident response – Integration with security teams for rapid threat response
The goal is to achieve the same level of security visibility in OT networks that organizations expect in IT environments, while respecting the operational constraints that make manufacturing different from traditional business systems.
Patch Management and Firmware Updates
Managing security updates in industrial environments requires specialized procedures that balance security improvements with operational stability. Unlike IT systems that can be updated during maintenance windows, OT systems often require extended planning and testing before any changes.
Industrial patch management best practices:
• Risk assessment – Evaluating security vulnerabilities against operational impact before applying updates
• Testing procedures – Validating updates in development environments before production deployment
• Rollback planning – Preparing procedures to quickly restore systems if updates cause problems
• Vendor coordination – Working with equipment manufacturers to ensure update compatibility
The challenge lies in managing systems with different update cycles and requirements. Some PLCs may receive firmware updates quarterly, while others operate for years without changes. Security teams must prioritize updates based on risk levels and operational impact.
Update prioritization factors:
• Vulnerability severity – Critical security flaws require immediate attention regardless of operational impact
• System criticality – Updates to safety systems and primary production equipment take priority
• Attack likelihood – Vulnerabilities with known exploits or active threats require a faster response
• Business impact – Considering production schedules and customer commitments when planning updates
Organizations need policies that define acceptable risk levels and update timelines for different types of systems. These policies should align with business objectives while maintaining adequate security protection.
Bridging IT and OT Security Teams
Effective industrial cybersecurity requires collaboration between IT security professionals and OT operations teams. These groups often have different priorities, technical backgrounds, and risk tolerance levels that must be aligned to protect industrial systems effectively.
Successful collaboration strategies:
• Cross-training programs – Teaching IT staff about industrial systems and OT staff about cybersecurity
• Joint incident response – Developing procedures that leverage both IT security expertise and OT operational knowledge
• Shared visibility tools – Implementing monitoring systems that both teams can access and understand
• Regular communication – Establishing ongoing dialogue about threats, vulnerabilities, and operational changes
The cultural differences between IT and OT teams can create challenges. IT security focuses on confidentiality and data protection, while OT operations prioritize availability and safety. Finding common ground requires understanding how cybersecurity supports operational objectives rather than conflicting with them.
Building effective partnerships:
• Business case alignment – Demonstrating how security improvements support operational reliability and efficiency
• Operational integration – Incorporating security considerations into existing operational procedures
• Performance metrics – Measuring security effectiveness in terms that operations teams value
• Executive support – Ensuring leadership reinforces the importance of IT-OT collaboration
When IT and OT teams work together effectively, organizations can implement security measures that protect against cyber threats while maintaining the operational excellence that manufacturing requires. This collaboration becomes increasingly important as industrial systems become more connected and cyber threats continue evolving.
The investment in people, processes, and technology needed for effective industrial cybersecurity pays dividends in operational reliability, regulatory compliance, and peace of mind. Organizations that take proactive steps to secure their OT environments position themselves for success in an increasingly connected manufacturing landscape.
Conclusion
Understanding how hackers access PLCs and shut down production lines reveals the critical importance of industrial cybersecurity in 2026. The convergence of IT and OT networks has created new opportunities for attackers, while manufacturing organizations often lack the specialized security measures needed to protect their operational technology.
The attack methods we’ve explored—from phishing campaigns that pivot to PLC networks to subtle process manipulation that causes long-term damage—demonstrate that traditional IT security approaches aren’t sufficient for protecting industrial systems. Manufacturing companies need comprehensive strategies that address network segmentation, continuous monitoring, patch management, and cross-functional collaboration between IT and OT teams.
The key steps for protecting your organization include:
• Implementing proper network segmentation between IT and OT environments
• Deploying specialized monitoring tools designed for industrial protocols and communications
• Establishing patch management procedures that balance security with operational requirements
• Building collaboration between IT security and OT operations teams
• Creating incident response plans that address both cyber threats and operational safety
The stakes continue rising as manufacturing becomes more connected and cyber criminals develop more sophisticated attack techniques. Organizations that invest in industrial cybersecurity today will have significant advantages in operational reliability, regulatory compliance, and competitive positioning.
Don’t wait for a successful attack to expose vulnerabilities in your industrial systems. The cost of prevention is always lower than the cost of recovery, and the peace of mind that comes from knowing your production systems are secure allows you to focus on what matters most—growing your business.
If you’re ready to assess your current OT security posture and develop a comprehensive protection strategy, our team of industrial cybersecurity experts can help. We understand the unique challenges of manufacturing environments and provide personalized service that addresses your specific operational requirements while delivering the proactive solutions you need to stay secure.
Frequently Asked Questions
How long does it typically take for hackers to access PLCs after initial network compromise?
The timeline varies significantly based on network architecture and security controls. In poorly segmented environments, attackers can reach PLCs within hours of compromising IT systems. However, sophisticated attackers often spend weeks mapping networks and gathering credentials to avoid detection before accessing production systems.
Can air-gapped PLC systems still be vulnerable to cyber attacks?
Yes, air-gapped systems remain vulnerable to physical attacks, USB-based malware, and insider threats. The Stuxnet attack demonstrated that even isolated industrial systems can be compromised through removable media and social engineering targeting maintenance personnel.
What’s the difference between IT and OT security monitoring?
IT security monitoring focuses on data protection and network traffic analysis using standard protocols. OT monitoring requires specialized tools that understand industrial protocols like Modbus, DNP3, and EtherNet/IP, while operating passively to avoid disrupting real-time control systems.
How often should PLC firmware be updated for security?
PLC firmware should be updated based on risk assessment rather than fixed schedules. Critical security vulnerabilities require immediate attention, while routine updates can follow planned maintenance windows. Most organizations aim for annual reviews with updates applied as needed.
What are the signs that PLCs may have been compromised?
Warning signs include unexplained production anomalies, unusual network traffic patterns, unauthorized configuration changes, unexpected system reboots, and performance degradation. However, sophisticated attacks may not show obvious symptoms for weeks or months.
Can ransomware specifically target PLC systems?
Yes, specialized ransomware variants can target industrial control systems. These attacks may encrypt PLC programming software, modify control logic, or disrupt communication protocols. Some ransomware specifically designed for OT environments can render PLCs inoperable until restored from backups.
What role do vendors play in PLC security risks?
Vendors often require remote access for maintenance and support, creating potential attack vectors. Risks include shared credentials, persistent VPN connections, and inadequate monitoring of vendor activities. Organizations should implement vendor access management policies and monitor all remote sessions.
How much does industrial cybersecurity monitoring typically cost?
Costs vary based on facility size and complexity, typically ranging from $50,000 to $500,000 annually for comprehensive OT security monitoring. This includes specialized software, hardware appliances, and managed services. The investment is usually justified by avoiding a single production outage.
What compliance requirements exist for PLC security?
Requirements vary by industry and region. NERC CIP applies to electric utilities, FDA regulations cover pharmaceutical manufacturing, and NIST frameworks provide general guidance. Many insurance policies now require specific cybersecurity controls for coverage of operational technology incidents.
Can existing IT security staff handle OT security effectively?
IT security staff need additional training to understand industrial protocols, operational constraints, and safety implications. Cross-training programs and collaboration with OT operations teams are essential. Many organizations benefit from specialized industrial cybersecurity consultants during initial implementation.
What happens if a PLC attack affects safety systems?
Safety system attacks create serious risks requiring immediate emergency response procedures. Organizations should have plans for manual operation, emergency shutdowns, and coordination with safety personnel. Regulatory reporting may be required depending on the industry and potential impact.
How can small manufacturers afford industrial cybersecurity?
Small manufacturers can start with basic measures like network segmentation, password management, and employee training. Cloud-based monitoring services and managed security providers offer cost-effective options. Many cybersecurity improvements can be implemented gradually as part of normal equipment upgrades.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity