Article Summary
• Who this is for: Small business owners, office managers, and operations leaders relying on a single internal IT person or basic MSP support to manage cybersecurity and IT operations.
• The challenge: Traditional IT support is no longer enough to defend against modern cyber threats like ransomware, AI-driven phishing, compliance failures, and cloud security risks. Businesses without 24/7 monitoring, tested backups, and specialized security expertise face major downtime, financial loss, and insurance/compliance exposure.
• Key insights covered:
- Cybersecurity in 2026 requires specialized expertise, continuous monitoring, and layered defense strategies that one IT generalist cannot realistically provide.
- Most successful attacks happen after hours, making 24/7 monitoring and rapid incident response essential for minimizing damage.
- A hybrid approach combining internal IT staff with managed cybersecurity services delivers stronger protection without replacing existing IT personnel.
- Modern security now includes compliance management, endpoint detection, immutable backups, employee security training, and proactive threat detection.
- Businesses that delay upgrading their security posture increase their risk of ransomware, operational downtime, failed compliance audits, and cyber insurance denial.
• Your outcome: Readers will understand exactly where their current IT setup leaves them vulnerable and what practical steps are needed to strengthen cybersecurity. They’ll walk away with a clearer roadmap for reducing risk, improving business continuity, and implementing scalable security support that protects operations and revenue.
Quick Answer
Your dedicated IT person can’t single-handedly protect your business from today’s cyber threats because modern cybersecurity requires 24/7 monitoring, specialized expertise across multiple domains, and redundant coverage that no individual can provide. Small business cybersecurity support now demands a team approach with continuous threat detection, compliance management, and proactive defense strategies that go far beyond traditional IT maintenance.
Key Takeaways
• Cyber threats evolved dramatically – 2026 attacks use AI, target cloud systems, and exploit remote work vulnerabilities your IT person wasn’t trained for
• 24/7 monitoring is essential – Hackers don’t work business hours, but most internal IT staff can’t provide round-the-clock security oversight
• Specialization matters – Modern cybersecurity requires expertise in compliance, endpoint detection, incident response, and threat intelligence
• Single point of failure risk – When your IT person is sick, on vacation, or overwhelmed, your security coverage disappears
• Hybrid approach works best – Keep internal IT for daily operations while partnering with managed security providers for specialized protection
• Compliance requirements increased – Insurance companies and regulations now mandate security standards that most small businesses can’t meet alone
• Proactive defense beats reactive fixes – Modern threats require prevention and rapid response, not just problem-solving after attacks occur
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation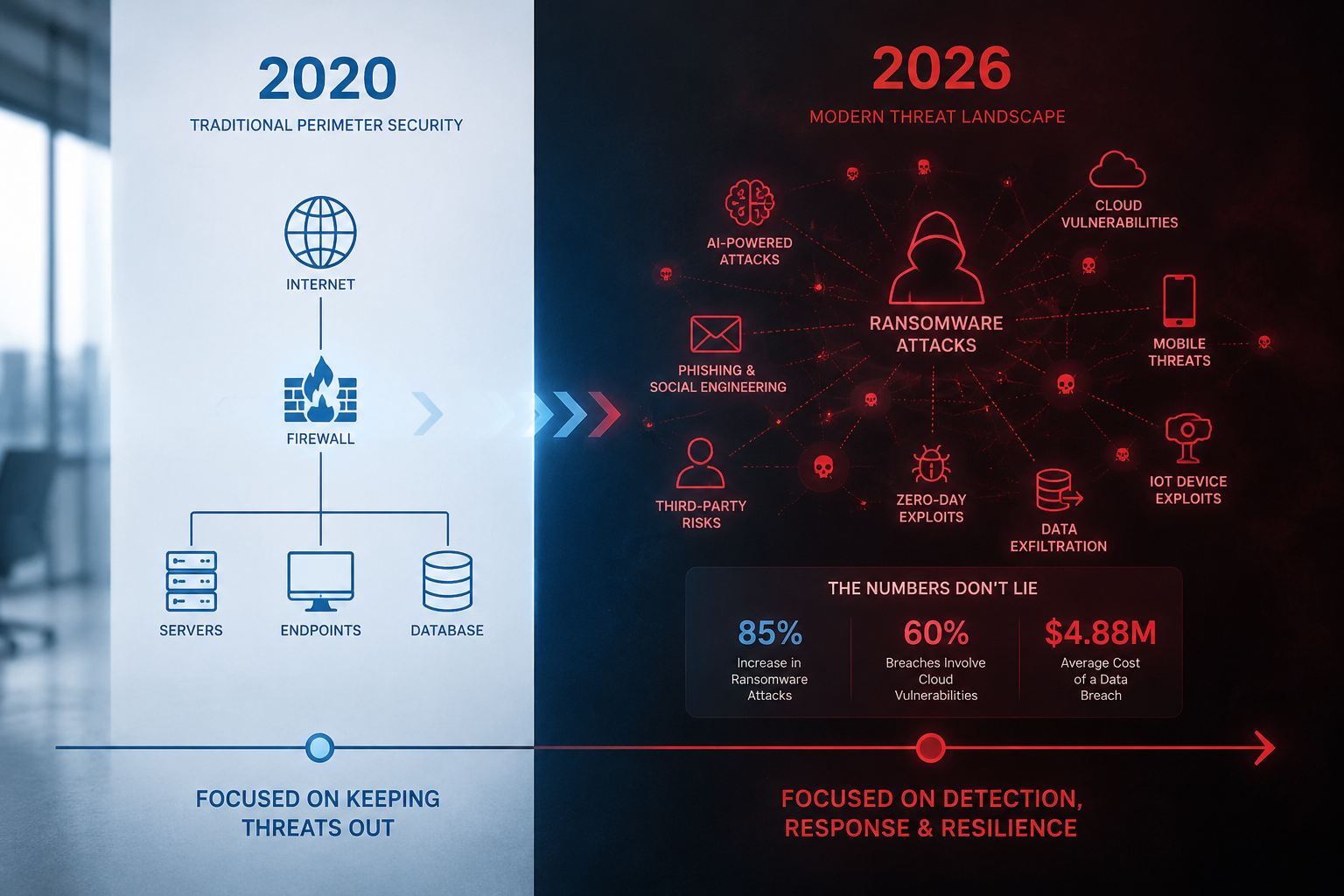
How Cybersecurity Threats Changed Everything in 2026
The cybersecurity landscape transformed completely between 2020 and 2026, making traditional IT support inadequate for business protection. What worked five years ago now leaves dangerous security gaps that cybercriminals actively exploit.
AI-powered attacks became mainstream in 2025, allowing hackers to create personalized phishing emails, deepfake voice calls, and automated vulnerability scanning at an unprecedented scale. Your IT person likely learned cybersecurity when these threats didn’t exist.
Cloud-first business operations introduced new attack vectors through misconfigured cloud storage, compromised SaaS applications, and complex multi-vendor security integration challenges. Managing security across Microsoft 365, cloud backups, and various business applications requires specialized knowledge that most generalist IT professionals don’t possess.
Remote work permanently changed the security perimeter. Employees access company data from home networks, coffee shops, and mobile devices, creating dozens of potential entry points that need constant monitoring and protection.
Ransomware groups professionalized their operations, targeting small businesses specifically because they know most lack sophisticated defenses. These groups research your company, employees, and IT infrastructure before launching carefully planned attacks designed to maximize damage and the likelihood of payment.
The reality? Cybersecurity became a specialized field requiring dedicated focus, continuous education, and team-based approaches that individual IT generalists cannot provide while managing daily technology operations.
Why the Traditional IT Support Model Falls Short
Most small businesses still rely on a single IT person or a break-fix support model that worked fine when cybersecurity meant installing antivirus software and updating firewalls. This approach creates four critical vulnerabilities in 2026’s threat environment.

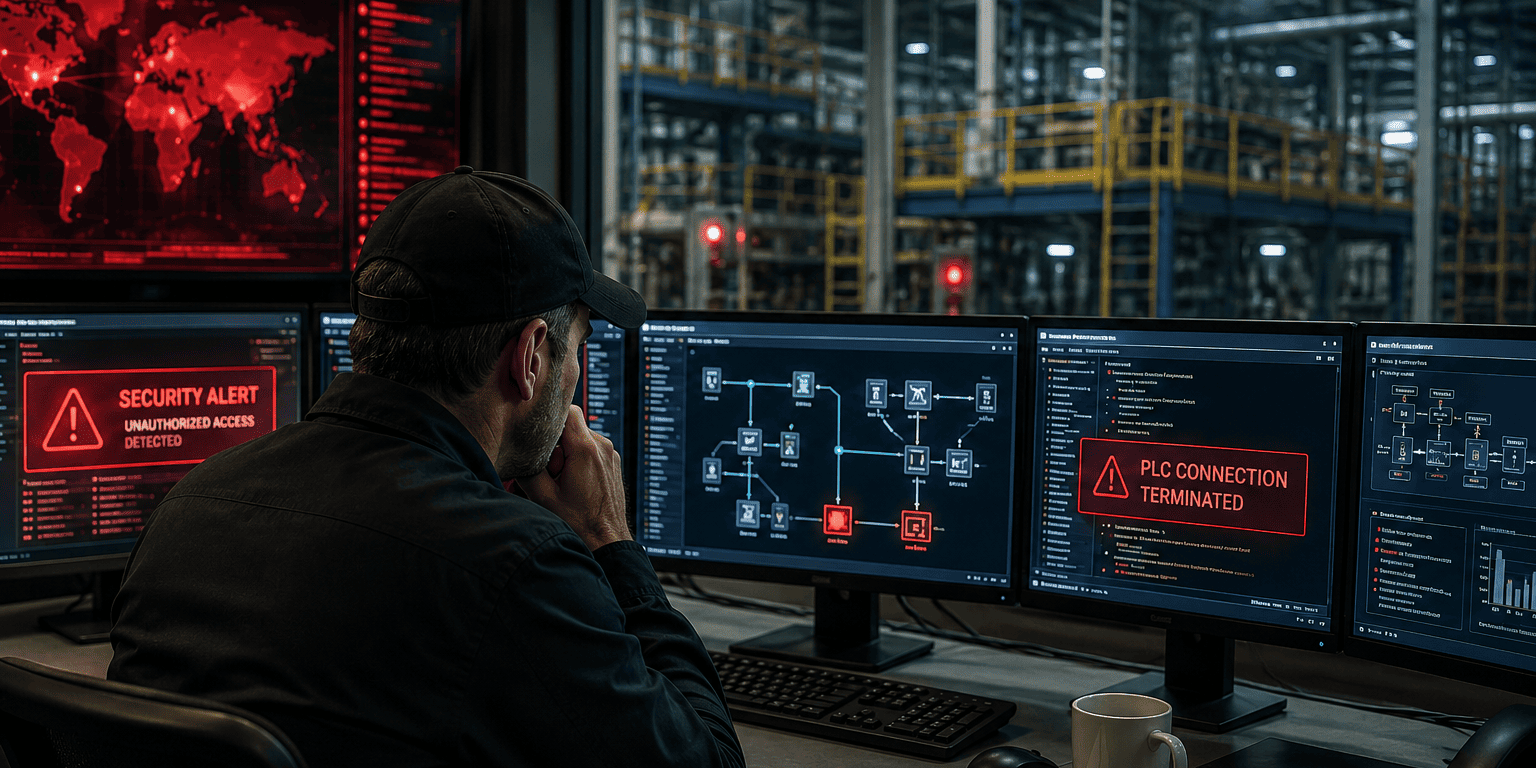
No 24/7 Security Monitoring
Cybercriminals operate around the clock, often launching attacks during weekends and holidays when they know businesses have minimal IT coverage. Your IT person works business hours, but hackers don’t.
Real-world impact: A manufacturing company in Atlanta discovered ransomware had been encrypting its files for 72 hours over a long weekend. Their part-time IT contractor only checked systems on Tuesday morning; by then, three years of customer data were compromised, and production stopped for two weeks.
Modern threats require continuous monitoring with automated alert systems, threat detection algorithms, and immediate response capabilities. No single person can provide this level of coverage while maintaining work-life balance.
Limited Cybersecurity Expertise
Your IT person excels at fixing computers, managing networks, and solving daily technology problems. But cybersecurity now requires specialized knowledge in:
• Threat intelligence – Understanding current attack methods and emerging vulnerabilities
• Compliance frameworks – Meeting HIPAA, SOC 2, PCI DSS, and insurance requirements
• Incident response – Containing breaches and minimizing damage when attacks occur
• Security architecture – Designing layered defenses across cloud and on-premise systems
• Forensic analysis – Investigating security incidents and preventing recurrence
Expecting one person to master all these specialties while handling daily IT tasks is unrealistic. It’s like asking your family doctor to also perform brain surgery; both are medical professionals, but the expertise requirements are completely different.
Burnout and Overwhelm Risks
IT professionals face increasing pressure as cybersecurity responsibilities pile onto their existing workload. They’re expected to maintain systems, support users, manage vendors, and now also become cybersecurity experts, often without additional training or resources.
This leads to dangerous shortcuts, delayed security updates, and reactive instead of proactive security management. When your IT person is overwhelmed, security becomes an afterthought until something breaks.
Single Point of Failure
What happens when your IT person gets sick, takes a vacation, or finds another job? Your entire cybersecurity program disappears with them. There’s no backup expertise, no continuity of security monitoring, and no institutional knowledge about your specific security configuration.
Choose this approach if: Your business handles minimal sensitive data, operates entirely offline, and can afford several days of downtime without significant financial impact. For most businesses in 2026, this describes almost no one.
What Modern Small Business Cybersecurity Support Actually Requires
Effective cybersecurity protection in 2026 demands a comprehensive approach that combines technology, expertise, and continuous monitoring. Here’s what your business actually needs to stay secure.

24/7 Security Operations Center (SOC) Monitoring
Professional cybersecurity requires around-the-clock monitoring by security analysts who specialize in threat detection and incident response. A proper SOC provides:
Real-time threat detection using advanced algorithms that analyze network traffic, user behavior, and system activities for suspicious patterns. These systems can identify potential breaches within minutes, not days or weeks.
Immediate incident response with security experts who know how to contain threats, preserve evidence, and minimize business disruption. When ransomware strikes at 2 AM on Sunday, you need someone responding immediately, not waiting until Monday morning.
Threat intelligence integration that keeps your defenses updated against the latest attack methods, malware signatures, and vulnerability exploits targeting businesses like yours.
Specialized Security Expertise
Modern cybersecurity requires a team of specialists, each focused on different aspects of your digital protection:
• Security architects who design comprehensive defense strategies
• Compliance specialists who ensure you meet industry regulations and insurance requirements
• Incident response experts who handle breaches quickly and effectively
• Penetration testers who proactively find vulnerabilities before hackers do
• Security awareness trainers who educate your employees about current threats
No single IT person can develop expertise across all these areas while also managing your daily technology needs.
Advanced Endpoint Detection and Response (EDR)
Traditional antivirus software catches known threats, but modern attacks use custom malware and sophisticated techniques that bypass signature-based detection. EDR solutions provide:
Behavioral analysis that identifies suspicious activities even from unknown threats. If software starts encrypting files rapidly or accessing unusual network locations, EDR systems can stop it immediately.
Automated response capabilities that isolate infected devices, block malicious processes, and preserve forensic evidence without waiting for human intervention.
Continuous monitoring of all endpoints, including laptops, desktops, servers, and mobile devices that access your business data.
Comprehensive Backup and Disaster Recovery
Effective backup strategies go far beyond copying files to an external drive. Modern backup solutions include:
Immutable backups that ransomware cannot encrypt or delete, ensuring you always have clean data to restore from. These use specialized storage that prevents any modification once data is written.
Rapid recovery capabilities that can restore entire systems within hours, not days or weeks. When production stops, every hour costs money.
Regular testing and validation to ensure backups actually work when needed. Many businesses discover their backup strategy failed only when they need to restore critical data.
Compliance and Risk Management
Most small businesses now face regulatory requirements or insurance mandates that require documented cybersecurity programs. This includes:
Policy development covering data handling, access controls, incident response procedures, and employee security training requirements.
Regular risk assessments that identify vulnerabilities and prioritize security improvements based on actual business impact.
Audit trail maintenance with detailed logs of security events, access attempts, and system changes that auditors and insurance companies require.
Choose managed cybersecurity if: Your business stores customer data, processes payments, requires compliance certifications, or cannot afford more than a few hours of downtime without significant revenue loss.
Real Business Risks Your Current Setup Can’t Handle
Understanding specific scenarios where traditional IT support fails helps illustrate why comprehensive small business cybersecurity support has become essential for protecting your operations and reputation.
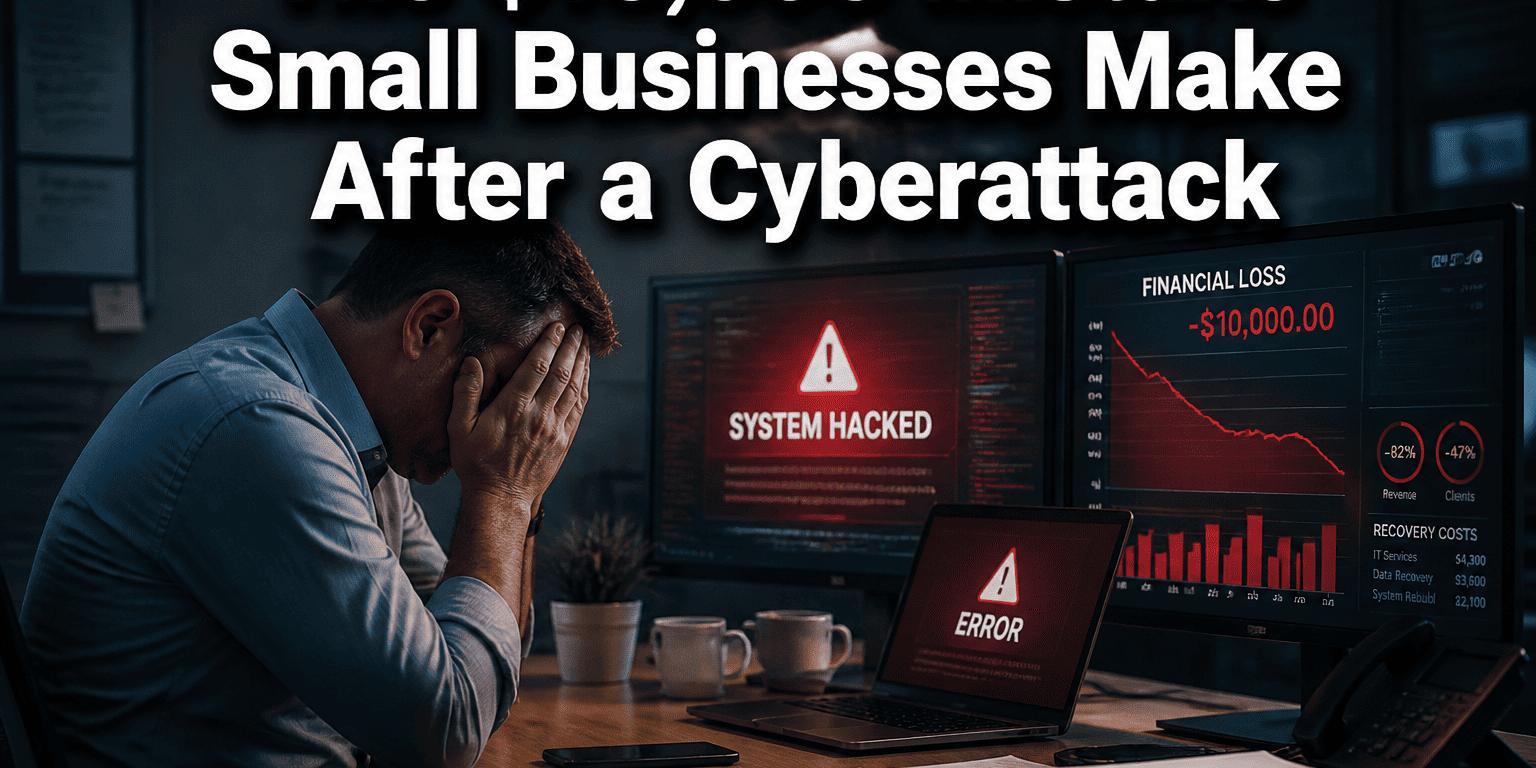
The Weekend Ransomware Attack
Scenario: Friday evening, your accounting manager receives an email appearing to be from your largest client requesting an urgent invoice review. She downloads the attachment, unknowingly installing ransomware that begins encrypting files across your network.
Traditional IT response: Your IT person discovers the attack on Monday morning when employees can’t access files. By then, ransomware had encrypted three days’ worth of data, including customer records, financial files, and project documents. Recovery takes two weeks and costs $45,000 in lost productivity, emergency IT services, and ransom payment.
Managed security response: Automated monitoring detects unusual file encryption activity within 15 minutes. Security analysts immediately isolate affected systems, stop the ransomware spread, and begin recovery from immutable backups. Business resumes normal operations by Monday morning with minimal data loss.
The Compliance Audit Nightmare
Scenario: Your cyber insurance company requires a security audit to renew your policy. They want documentation of security policies, employee training records, access controls, and incident response procedures.
Traditional IT challenge: Your IT person scrambles to create policies retroactively, can’t provide training documentation that doesn’t exist, and has no formal incident response plan. Insurance renewal is denied, leaving you vulnerable to lawsuits and financial losses if a breach occurs.
Managed security advantage: Comprehensive documentation exists for all security policies, employee training is tracked and updated regularly, and detailed audit logs demonstrate ongoing compliance. Insurance renewal proceeds smoothly with potential premium reductions for strong security practices.
The Supply Chain Compromise
Scenario: A software vendor you use gets hacked, and attackers use their access to push malicious updates to customer systems, including yours. This “supply chain attack” bypasses traditional security because the malware comes from a trusted source.
Traditional IT limitation: Your IT person has no visibility into vendor security practices, no way to detect compromised software updates, and no established procedures for responding to supply chain incidents.
Managed security protection: Threat intelligence services provide early warning about vendor compromises, endpoint detection systems identify suspicious behavior from “trusted” software, and incident response teams have established procedures for supply chain security events.
The Employee Departure Data Theft
Scenario: A disgruntled employee downloads customer lists, financial data, and proprietary information before quitting to join a competitor. They use legitimate access credentials, making the theft difficult to detect.
Traditional IT blind spot: Your IT person focuses on technical issues, not monitoring user behavior patterns or data access anomalies. The theft goes unnoticed until customers start switching to the competitor months later.
Managed security detection: User behavior analytics identify unusual data access patterns, data loss prevention systems block large file downloads, and detailed audit logs provide evidence for legal action if needed.
Common mistake: Assuming cyber insurance will cover all costs of a security breach. Most policies have significant exclusions and require proof of reasonable security measures before paying claims.
Small Business Cybersecurity Risk Assessment
Answer these questions to evaluate your current cybersecurity posture and identify areas for improvement.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free ConsultationThe Hybrid Approach: Keeping IT Staff While Adding Security Expertise
You don’t need to fire your IT person to get proper cybersecurity protection. The most effective approach combines internal IT staff for daily operations with specialized managed security services for comprehensive threat protection.

How Internal IT and Managed Security Work Together
Your IT person handles: Daily user support, hardware maintenance, software installations, network administration, and vendor coordination. These operational tasks require someone who understands your specific business processes and can provide personalized service during business hours.
Managed security providers handle: 24/7 threat monitoring, security incident response, compliance management, advanced threat detection, and specialized cybersecurity expertise that requires dedicated focus and continuous training.
This division allows your IT person to focus on what they do best while ensuring cybersecurity gets the specialized attention it requires. Neither role duplicates the other; they complement each other for comprehensive protection.
Benefits of the Hybrid Model
Cost efficiency: Hiring internal cybersecurity specialists costs $80,000-$120,000 annually per person, plus benefits and training costs. Managed security services provide an entire team of specialists for a fraction of that investment.
Expertise depth: Your business gains access to security architects, compliance specialists, incident response experts, and threat intelligence analysts without the overhead of hiring and training multiple specialists.
Scalability: Security services can scale up during high-risk periods or scale down during stable operations, providing flexibility that fixed staffing can’t match.
Continuity: When your IT person takes a vacation or changes jobs, security monitoring and protection continue uninterrupted through the managed service provider.
Making the Transition Smooth
Start with assessment: Professional security assessments identify current vulnerabilities and create a roadmap for improvement that doesn’t disrupt daily operations.
Gradual implementation: Add managed security services incrementally, beginning with 24/7 monitoring and expanding to include backup management, compliance support, and advanced threat detection over time.
Clear communication: Explain to your IT person that managed security services enhance their role rather than replace it. They become the primary point of contact for security vendors while focusing on operational excellence.
Defined responsibilities: Document which tasks remain with internal IT and which transfer to managed security providers, preventing confusion and ensuring nothing falls through the cracks.
Choose the hybrid approach if: You want to maintain internal IT relationships and operational control while adding specialized cybersecurity expertise that your current staff cannot reasonably provide.
When to Make the Switch to Comprehensive Security Support
Specific business indicators signal when traditional IT support becomes inadequate for your cybersecurity needs. Recognizing these warning signs helps you transition to comprehensive small business cybersecurity support before a costly incident occurs.
Clear Warning Signs
Compliance requirements increased: If customers, partners, or insurance companies now require security certifications, documented policies, or audit reports that your current IT setup cannot provide.
Remote work expanded: When employees regularly access business data from home, mobile devices, or public networks, that extend your security perimeter beyond traditional office boundaries.
Cloud services multiplied: Using multiple cloud applications like Microsoft 365, cloud backup services, online accounting software, or industry-specific SaaS platforms creates security complexity that requires specialized management.
Cyber insurance demands grew: Insurance companies increasingly require specific security controls, employee training documentation, and incident response plans that most small businesses cannot develop internally.
Business growth accelerated: Adding employees, locations, or revenue streams increases your attractiveness to cybercriminals while expanding the potential attack surface that needs protection.
Financial Triggers
Revenue exceeds $1 million annually: Businesses at this level become attractive targets for cybercriminals and typically cannot afford extended downtime without significant financial impact.
Customer data volume increased: Storing personal information, payment details, or confidential business data creates liability that requires professional-grade protection.
Regulatory oversight applies: Industries like healthcare, finance, legal services, or government contracting face compliance requirements that demand documented cybersecurity programs.
Downtime costs exceed $5,000 per day: If system outages prevent revenue generation, customer service, or critical operations at this level, proactive security becomes cost-effective insurance.
Operational Indicators
IT person works excessive overtime: When cybersecurity responsibilities push your IT staff beyond normal working hours regularly, it’s time to add specialized support.
Security updates lag: If system patches, software updates, or security configurations fall behind schedule due to competing priorities, vulnerabilities accumulate dangerously.
Incident response is reactive: Discovering security issues days or weeks after they occur, rather than detecting and responding immediately, indicates inadequate monitoring capabilities.
Backup testing stopped: If you’re not regularly testing data recovery procedures or haven’t verified backup integrity recently, your disaster recovery plan probably won’t work when needed.
Making the Business Case
Calculate current risk exposure: Estimate costs of one-week downtime, regulatory fines, customer notification requirements, and reputation damage from a security breach.
Compare service costs: Professional managed security services typically cost less than hiring one internal cybersecurity specialist, while providing expertise from an entire team.
Review insurance requirements: Many cyber insurance policies now offer premium discounts for businesses using managed security services, potentially offsetting service costs.
Consider growth plans: If you plan to expand operations, add employees, or pursue new markets, building proper cybersecurity infrastructure now prevents costly retrofitting later.
Edge case consideration: Very small businesses (under 10 employees) with minimal digital operations might delay comprehensive security services, but should still implement basic managed backup and monitoring solutions.
Frequently Asked Questions
Q: How much does professional cybersecurity support cost compared to keeping everything in-house?
A: Managed cybersecurity services typically cost $150-$500 per employee per month, while hiring internal cybersecurity specialists costs $80,000-$120,000 annually each. Most small businesses save 40-60% using managed services while getting broader expertise.
Q: Will managed security services slow down our IT operations or create bureaucracy?
A: Properly implemented managed security enhances IT efficiency by handling specialized tasks your internal staff shouldn’t manage. Your IT person focuses on daily operations while security experts handle threat monitoring and incident response.
Q: How quickly can managed security services detect and respond to cyber threats?
A: Professional security operations centers typically detect threats within 15-30 minutes and begin a response immediately. Internal IT staff usually discover threats hours or days later during routine maintenance.
Q: What happens to our current IT person if we add managed security services?
A: Your IT person’s role evolves to focus on operational excellence, user support, and vendor coordination. They become more valuable by specializing in business-specific technology needs rather than trying to master cybersecurity.
Q: Do small businesses really need 24/7 security monitoring?
A: Yes, because cybercriminals specifically target small businesses during off-hours when they know monitoring is minimal. Most successful ransomware attacks occur during weekends and holidays.
Q: How do we maintain control over our systems with external security providers?
A: You retain complete control over business decisions while security providers handle technical implementation. Clear service agreements define responsibilities, access levels, and escalation procedures.
Q: What’s the biggest mistake small businesses make with cybersecurity?
A: Assuming their current IT setup provides adequate protection without testing incident response procedures, validating backup systems, or assessing compliance with current security standards.
Q: How do we choose between different managed security providers?
A: Look for providers with relevant industry experience, 24/7 operations centers, clear pricing, local support availability, and references from similar businesses in your area.
Q: Can we start with basic managed security and expand services later?
A: Absolutely. Most businesses begin with 24/7 monitoring and backup management, then add compliance support, advanced threat detection, and employee training over time based on needs and budget.
Q: What compliance requirements might affect our business?
A: Common requirements include HIPAA for healthcare data, PCI DSS for payment processing, SOC 2 for service providers, and various cyber insurance mandates that most small businesses now face.
Q: How long does it take to implement comprehensive cybersecurity support?
A: Basic monitoring and backup services can be operational within 2-4 weeks. Complete security program implementation, including policies, training, and advanced controls, typically takes 60-90 days.
Q: What should we do immediately while evaluating managed security options?
A: Ensure current backups are working and tested, update all software and security patches, enable multi-factor authentication on critical accounts, and document your current IT inventory and procedures.
Conclusion
Your dedicated IT person provides valuable daily support, but cybersecurity in 2026 requires specialized expertise, 24/7 monitoring, and team-based approaches that no individual can deliver alone. The hybrid model – combining internal IT operations with managed cybersecurity services – gives you the best of both worlds: personalized service for daily needs and professional security protection against modern threats.
The question isn’t whether you need better cybersecurity support, but how quickly you can implement it before a costly incident occurs. Every day you delay increases your exposure to ransomware, data breaches, and compliance violations that could devastate your business operations and reputation.
Take action today: Schedule a comprehensive security assessment to identify your current vulnerabilities and develop a roadmap for implementing professional cybersecurity support that complements your existing IT operations. Your business depends on it, and your peace of mind is worth the investment.
Don’t wait for a security incident to force your hand. The cost of prevention is always less than the cost of recovery, and in 2026’s threat landscape, comprehensive small business cybersecurity support isn’t optional – it’s essential for business survival and growth.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity