Article Summary
• Who this is for: Small business owners and operators in service-based or regulated industries, such as accounting, dental, healthcare, legal, finance, and local professional firms, who rely on backups but lack a formal cyber incident response plan.
• The challenge: After a cyberattack, panic-driven recovery decisions, especially restoring infected backups, can trigger reinfection, longer downtime, compliance exposure, and $10,000+ in avoidable costs.
• Key insights covered: The article breaks down the highest-cost recovery mistakes: restoring without forensic analysis, failing to isolate affected systems, skipping incident documentation/reporting, rushing password resets, and avoiding professional incident response support.
• Your outcome: Readers learn how to respond correctly in the first hours after an attack, protect clean systems, verify backups before restoration, reduce repeat incidents, and understand when to involve an MSP or cybersecurity partner to control business risk and recovery costs.
Quick Answer
The most expensive mistake small businesses make after a cyberattack isn’t the attack itself—it’s restoring operations from infected backups without proper isolation and forensic analysis. This single error typically costs businesses an additional $10,000 in repeated infections, compliance fines, and extended downtime, turning a manageable incident into a devastating financial crisis.
Key Takeaways
• Infected backup restoration is the #1 costly mistake, causing reinfection within 72 hours
• Skipping system isolation allows malware to spread to clean systems during recovery
• No incident reporting leads to compliance violations and potential $25,000+ fines
• Rushed password resets without proper analysis leave backdoors open for attackers
• Avoiding forensic analysis means missing how attackers got in, guaranteeing repeat attacks
• Proper incident response planning can reduce post-attack costs by 80%
• Same-day support from experienced IT partners prevents panic-driven, expensive decisions
• 24/7 monitoring catches attacks early, minimizing both initial and secondary damage
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
What Actually Happens After Most Small Business Cyberattacks
When ransomware hits a small accounting firm or a dental practice gets breached, the immediate reaction is pure panic. I’ve seen business owners make decisions in those first few hours that end up costing them far more than the original attack ever would have.
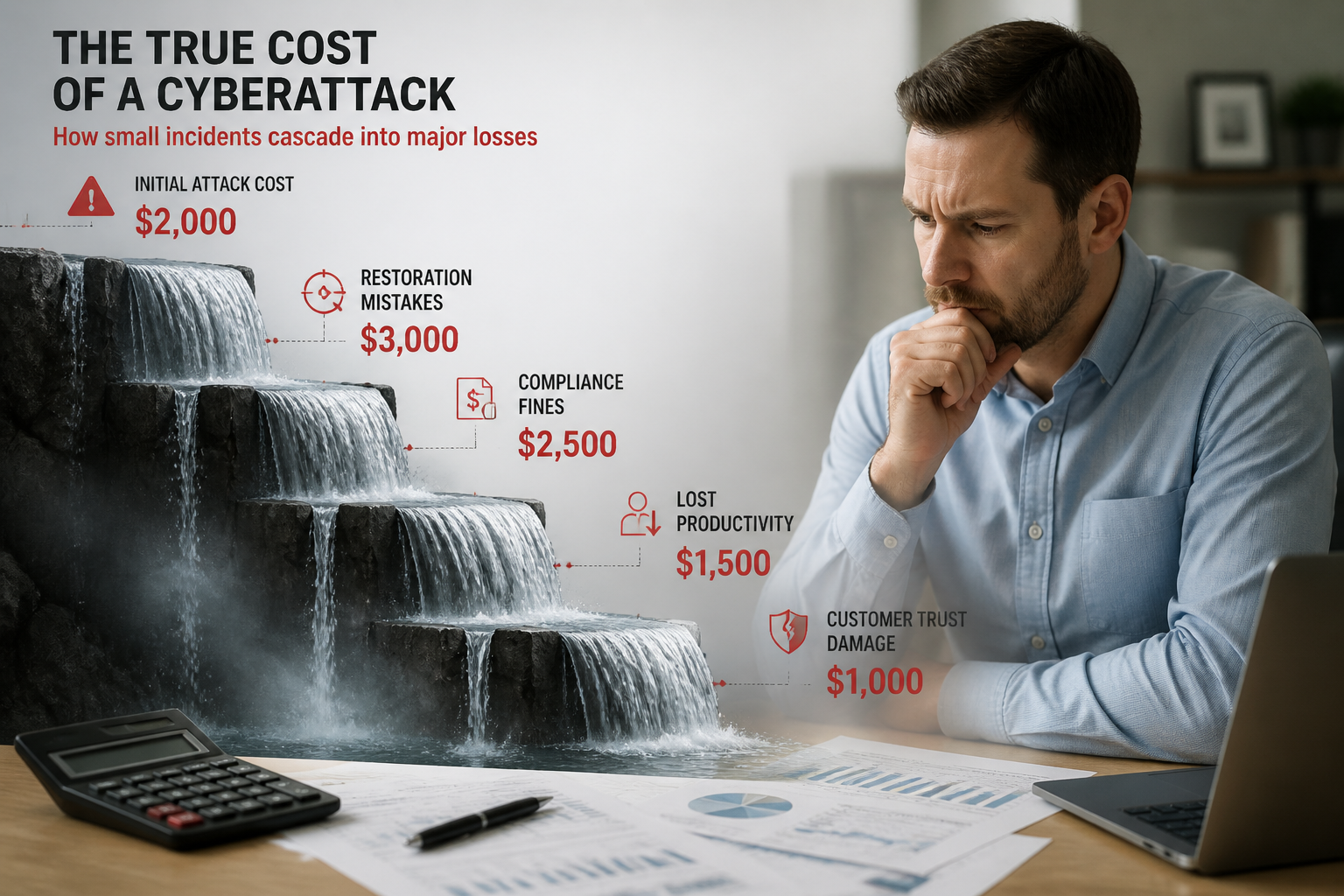
Here’s the typical scenario: Your systems are down, clients are calling, and you’re losing money every minute. The instinct is to get back online as quickly as possible. That urgency, while understandable, leads to the expensive mistakes that turn a $2,000 problem into a $12,000 nightmare.
Most small businesses don’t have a structured incident response plan. Without that roadmap, they’re making critical decisions under extreme stress exactly when clear thinking matters most. The result? A cascade of errors that compounds the original damage.
The reality is that 73% of small businesses that experience a cyberattack make at least one major recovery mistake, doubling their total costs. These aren’t technical failures—they’re process failures that could be easily avoided with the right guidance and a reliable partner who understands incident response.
The $10,000 Mistake: Restoring From Infected Backups
The single most expensive error small businesses make after a cyberattack is rushing to restore their systems from backups without proper analysis. This mistake alone typically costs an additional $8,000 to $12,000 in repeated infections and extended downtime.
Here’s what happens: After discovering the attack, panicked business owners immediately grab their most recent backup and start restoring everything. They’re thinking about getting back online quickly, not about whether that backup might already be compromised.
The problem? Most ransomware and malware infections lurk in systems for weeks or even months before activating. Your “clean” backup from yesterday probably contains the same malicious code that caused the attack. When you restore from infected backups, you’re essentially reinstalling the attack.
Within 24 to 72 hours, the malware reactivates. Now you’re dealing with a second attack, often worse than the first, because the attackers know your defenses are down. You’ve lost additional days of productivity, spent money on the first restoration attempt, and potentially exposed more sensitive data.
The financial breakdown:
- Initial restoration costs: $2,000-$3,000
- Second attack response: $3,000-$4,000
- Extended downtime (additional 3-5 days): $2,000-$3,000
- Emergency IT support for repeated incidents: $1,500-$2,000
- Total additional cost: $8,500-$12,000
The correct approach involves forensic analysis to determine how far back the infection goes, then restoring from a verified clean backup point. Yes, this means potentially losing more recent data, but it prevents the devastating cycle of reinfection that destroys small businesses.
Other Critical Mistakes After a Cyberattack Small Business Owners Make
Failing to Isolate Affected Systems Properly
When an attack is discovered, the immediate response should be containment. However, many small business owners try to “save” unaffected systems by quickly moving data or maintaining network connections. This spreads the infection to previously clean systems.
The mistake: Keeping infected systems connected to the network while trying to clean them, or transferring files from potentially compromised machines to “safe” computers.
The cost: What could have been isolated to one or two machines now affects your entire network. Complete network rebuilds can cost $5,000-$8,000 more than targeted system recovery.
The solution: Immediately disconnect affected systems from the network and internet. Don’t transfer anything until you know exactly what you’re dealing with.
Skipping Incident Documentation and Reporting
Small businesses often skip proper incident reporting, thinking they can handle everything internally. This creates serious compliance and legal issues, especially for businesses in regulated industries like healthcare, finance, or those handling customer payment data.
The mistake: Not documenting the incident timeline, affected systems, or potential data exposure. Failing to report breaches to relevant authorities or notify affected customers within the required timeframes.
The cost: Compliance violations can result in fines ranging from $10,000 to $50,000 for small businesses. Legal fees for handling customer lawsuits or regulatory investigations can add another $15,000-$25,000.
The solution: Document everything from the moment you discover the attack. Know your reporting requirements and meet all deadlines. When in doubt, consult with legal counsel early.
Weak Post-Attack Password and Access Management
After an attack, many businesses rush to change passwords without understanding how the attackers gained access. They’ll change user passwords but miss service accounts, admin credentials, or fail to revoke compromised access tokens.
The mistake: Surface-level password changes that don’t address the actual security gaps the attackers exploited.
The cost: Attackers maintain access through unchanged service accounts or backdoors, leading to repeat attacks within 30-60 days. Each subsequent attack costs progressively more as customer trust erodes and regulatory scrutiny increases.
The solution: Conduct a complete access audit. Change all passwords, revoke all access tokens, and implement multi-factor authentication before bringing systems back online.
Avoiding Professional Forensic Analysis
Small business owners often skip forensic analysis to save money, thinking they can figure out what happened on their own. This penny-wise, pound-foolish approach virtually guarantees future attacks.
The mistake: Cleaning up the obvious damage without understanding how attackers got in, what they accessed, or whether they left backdoors.
The cost: Without knowing the attack vector, you can’t fix the underlying vulnerability. Repeat attacks are almost inevitable, and each one becomes more expensive as attackers learn your systems.
The solution: Invest in professional forensic analysis. A $2,000-$3,000 forensic investigation can prevent $20,000+ in future attack costs.
Cyberattack Response Cost Calculator
Calculate the potential cost of post-cyberattack mistakes vs. proper response.
Cost Breakdown - Improper Response
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
The Correct Step-by-Step Response Plan
Having a structured response plan eliminates the guesswork and prevents costly mistakes. Here’s the proven approach that minimizes both immediate and long-term costs:
Immediate Response (First 2 Hours)
1. Stay calm and document everything
- Note the time of discovery
- Take photos of any ransom messages or error screens
- Don’t touch anything else until you have a plan
2. Isolate affected systems immediately
- Disconnect from the network and the internet
- Don’t shut down, just disconnect
- Leave systems running for forensic analysis
3. Contact your incident response team
- If you have an IT partner, call them immediately
- If not, contact a cybersecurity professional
- Don’t attempt recovery alone
Assessment Phase (Hours 2-24)
4. Conduct initial damage assessment
- Identify all affected systems
- Determine what data may have been compromised
- Check backup integrity going back 30-90 days
5. Begin forensic analysis
- Professional analysis of how the attack occurred
- Identification of the attack timeline
- Assessment of data exposure
6. Notify relevant parties
- Legal counsel (within 4 hours)
- Insurance provider (within 24 hours)
- Regulatory bodies (as required)
Recovery Phase (Days 2-7)
7. Implement containment measures
- Complete network segmentation
- Password and access credential reset
- Security patch deployment
8. Restore from verified clean backups
- Use backups from before the infection timeline
- Test restored systems in an isolated environment
- Gradually reconnect to the network with monitoring
9. Strengthen security posture
- Address vulnerabilities that enabled the attack
- Implement additional monitoring
- Update incident response procedures
Post-Recovery (Ongoing)
10. Monitor for reinfection
- 24/7 monitoring for 30+ days post-recovery
- Regular security assessments
- Employee security awareness training
This structured approach typically costs $5,000-$8,000 total, compared to $15,000-$25,000 for businesses that make critical mistakes during recovery.

How to Prevent These Expensive Mistakes After a Cyberattack
The best way to avoid costly post-attack mistakes is preparation. Small businesses that have an incident response plan and a reliable IT partner recover faster and spend significantly less on remediation.
Establish an Incident Response Partnership
Don’t wait until you’re under attack to find cybersecurity help. Establish a relationship with an IT provider that offers same-day support and has proven incident response expertise. When panic sets in, having a trusted partner who can guide you through the process is invaluable.
Look for providers that offer:
- 24/7 monitoring and response capabilities
- Documented incident response procedures
- Experience with businesses in your industry
- Straightforward pricing for emergency response
Create and Test Your Response Plan
A written incident response plan eliminates guesswork during high-stress situations. Your plan should include:
- Emergency contact information for IT support, legal counsel, and insurance
- Step-by-step procedures for containment and assessment
- Communication templates for customers, vendors, and regulatory bodies
- Decision trees for common scenarios
Test your plan annually with tabletop exercises. Practice makes perfect, and you don’t want your first time following the plan to be during a real attack.
Implement Proactive Security Measures
The goal is to catch attacks early, before they can cause significant damage. Invest in:
- Professional backup management with regular integrity testing
- Network monitoring that can detect unusual activity
- Employee security awareness training
- Regular security assessments and vulnerability management
Know Your Compliance Requirements
Understand what incident reporting and notification requirements apply to your business. Different industries have different rules, and the penalties for non-compliance can be severe. When in doubt, consult with legal counsel who understands cybersecurity law.
Frequently Asked Questions
How quickly should I respond after discovering a cyberattack?
Immediate isolation should happen within minutes of discovery. Professional help should be contacted within the first hour. The faster you respond correctly, the less damage occurs, and the lower your recovery costs will be.
Can I handle incident response myself to save money?
While possible, it’s rarely cost-effective for small businesses. The risk of making expensive mistakes far outweighs the cost of professional help. Most businesses that attempt DIY recovery end up spending more on corrections than they would have on a proper initial response.
How do I know if my backups are infected?
Professional forensic analysis can determine the infection timeline and identify clean backup points. Never assume recent backups are clean—most malware infections persist for weeks or months before detection.
What should I tell customers about the attack?
Be honest but measured in your communications. Focus on what you’re doing to protect them and when you expect to restore normal operations. Have legal counsel review any public statements before release.
How long does proper incident response take?
Complete recovery typically takes 5-10 business days when done correctly. Rushed recovery attempts often take longer due to repeated infections and additional complications.
Do I need to report every type of cyberattack?
Reporting requirements vary by industry and the type of data potentially compromised. Healthcare, finance, and businesses handling credit card data have specific notification requirements. Consult legal counsel to understand your obligations.
How can I prevent future attacks?
Address the vulnerabilities that enabled the initial attack, implement stronger access controls, provide security training for employees, and establish ongoing monitoring. Most repeat attacks exploit the same weaknesses as the original incident.
What does cyber insurance cover for incident response?
Coverage varies significantly between policies. Many cover forensic analysis, legal fees, and notification costs, but may not cover business interruption from poor recovery decisions. Review your policy details and understand what’s covered before you need it.
Should I pay ransomware demands?
Payment doesn’t guarantee data recovery and often leads to repeat attacks. Focus on proper backup and recovery procedures instead. Consult with legal counsel and law enforcement before making any payment decisions.
How do I choose the right incident response partner?
Look for providers with documented experience, industry expertise, 24/7 availability, and transparent pricing. Ask for references from similar businesses and verify their incident response credentials.
What’s the difference between backup restoration and disaster recovery?
Backup restoration simply copies files back to the systems. Disaster recovery includes forensic analysis, security remediation, and systematic restoration with verification. Proper disaster recovery prevents reinfection and addresses underlying vulnerabilities.
How often should I test my incident response plan?
Annual testing is the minimum recommendation. Quarterly tabletop exercises are ideal for businesses handling sensitive data. Regular testing identifies gaps in your plan and ensures everyone knows their role during an actual incident.
Conclusion
The aftermath of a cyberattack doesn’t have to devastate your small business financially. The $10,000+ mistakes we’ve discussed—restoring from infected backups, failing to isolate systems, skipping forensic analysis, and inadequate incident reporting—are entirely preventable with the right approach and guidance.
The key is having a reliable partner who can provide same-day support when you need it most. Panic-driven decisions made in isolation almost always lead to expensive complications that could have been avoided with proper expertise and a structured response plan.
Don’t wait until you’re under attack to establish these critical relationships and procedures. The businesses that recover quickly and cost-effectively are those that prepared in advance, implemented proactive solutions, and partnered with experienced IT professionals who understand the unique challenges small businesses face.
Your focus should be on running your business, not managing IT headaches or cybersecurity crises. With the right preparation and partnership, you can have the peace of mind that comes from knowing you’re protected and that if an incident does occur, you’ll handle it correctly the first time.
Take action today to assess your current incident response readiness. A small investment in preparation and the right IT partnership can save you tens of thousands of dollars and weeks of disruption when it matters most.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity