Article Summary
• Who this is for: Manufacturing business owners and operations leaders who rely on connected production systems and want to prevent costly downtime caused by cyberattacks
• The challenge: Ransomware increasingly targets manufacturing environments where IT and operational technology (OT) systems are connected, allowing attacks to halt production within hours
• Key insights covered: Why manufacturers are prime ransomware targets, how attacks spread through factory networks, the real cost of production downtime, and practical strategies like network segmentation, secure backups, and OT-focused cybersecurity planning
• Your outcome: A clear understanding of manufacturing cyber risks and actionable steps to strengthen security, protect production continuity, and reduce the risk of operational shutdowns with proactive IT and cybersecurity support
Manufacturing companies face a growing threat that can shut down entire production lines within hours. Ransomware in manufacturing attacks specifically target operational technology systems, causing production downtime that costs far more than traditional data breaches. The key to protection lies in understanding how these attacks spread through factory networks and implementing targeted defenses for both IT and OT environments.
Key Takeaways
• Manufacturing ransomware attacks target production systems, not just data, causing costly operational shutdowns
• Factory networks with connected OT systems create unique vulnerabilities that traditional IT security can’t address
• Production downtime from cyberattacks averages $50,000 per hour for mid-sized manufacturers
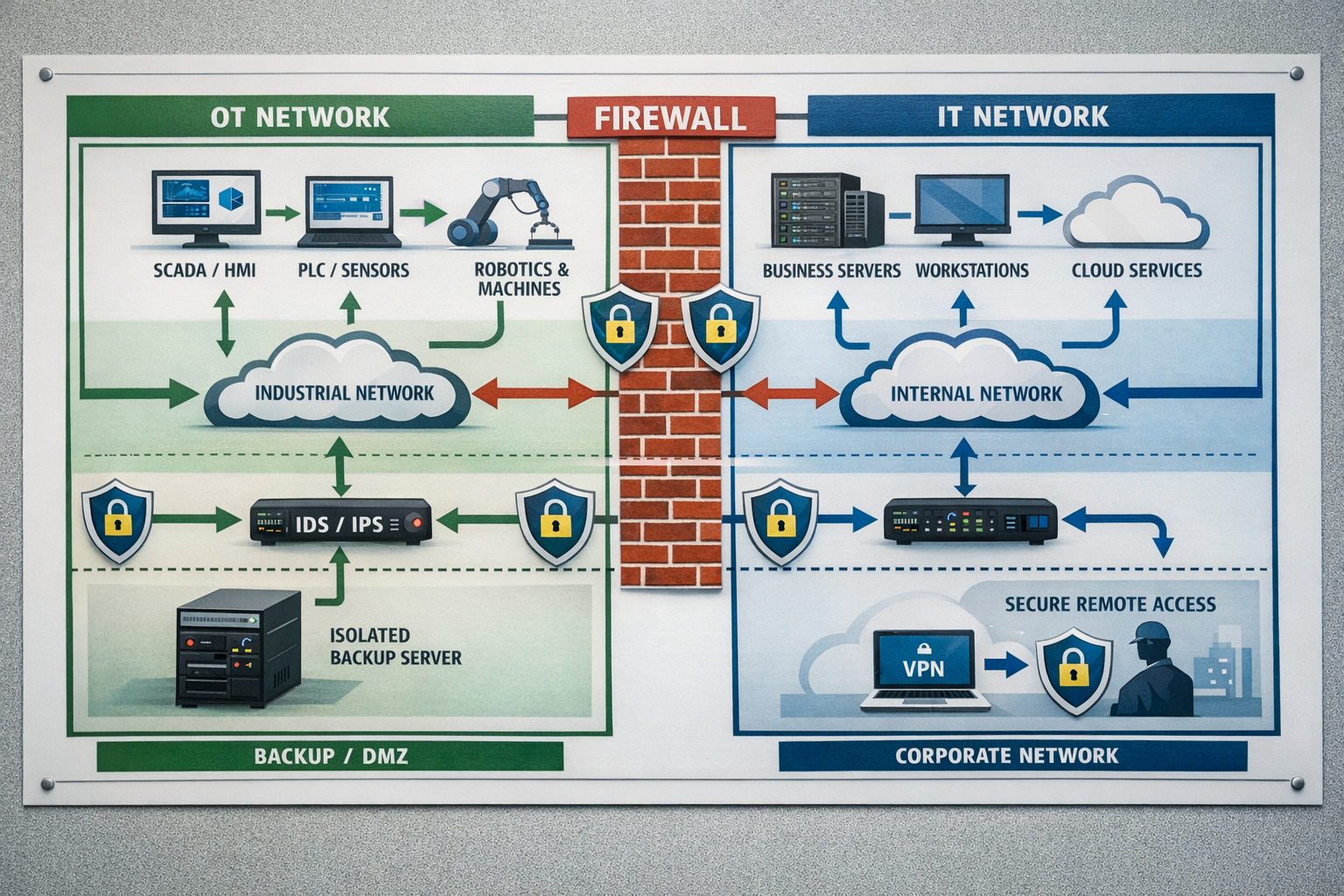
• Network segmentation between IT and OT systems provides the strongest defense against ransomware spread
• Isolated backup systems and incident response plans specific to manufacturing environments are essential
• Regular security assessments of industrial control systems help identify vulnerabilities before attackers do
• Employee training on manufacturing-specific phishing tactics reduces the most common attack entry point
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation

Why Manufacturing Companies Are Prime Ransomware Targets
Manufacturing companies have become the top target for ransomware attacks because of one simple fact: they can’t afford downtime. When a production line stops, the financial impact is immediate and severe. Every hour of shutdown means lost revenue, missed delivery deadlines, and potential safety risks.
What makes manufacturing so attractive to cybercriminals?
The combination of legacy systems and modern connectivity creates perfect conditions for attackers. Many factories run on industrial control systems that were designed decades ago, long before cybersecurity was a concern. These systems now connect to corporate networks and the internet, creating pathways that ransomware can exploit.
The financial pressure works in the attackers’ favor. A automotive parts manufacturer facing a three-day shutdown might lose $500,000 in revenue while also facing penalty clauses from major customers. This pressure often leads companies to pay ransoms quickly, making manufacturing a profitable target.
Manufacturing ransomware attacks also target the supply chain impact. When one factory shuts down, it can disrupt multiple customers and partners. This amplifies the pressure to restore operations quickly, regardless of cost.
Legacy system vulnerabilities compound the problem. Many manufacturing environments run Windows XP or older operating systems on critical equipment. These systems can’t be easily updated or replaced, creating permanent security gaps that attackers know how to exploit.
How Ransomware Spreads Through Manufacturing Networks
Understanding how ransomware moves through factory networks is crucial for building effective defenses. Manufacturing cyber resilience starts with recognizing that industrial networks operate differently from typical office environments.
The attack typically starts in the IT network. Phishing emails targeting accounting or administrative staff provide the initial foothold. Once inside the corporate network, attackers look for connections to the operational technology (OT) side where production systems operate.
Common pathways ransomware uses to spread:
• Shared network connections between office computers and factory floor systems
• Remote access tools used by equipment vendors for maintenance and support
• Engineering workstations that connect to both corporate networks and production equipment
• Unpatched industrial software running on Windows-based control systems
• USB drives and removable media moved between IT and OT environments
The OT environment amplifies the damage. Once ransomware reaches industrial control systems, it can encrypt human-machine interfaces (HMIs), supervisory control and data acquisition (SCADA) systems, and programmable logic controllers (PLCs). This doesn’t just lock up data – it stops production entirely.
Lateral movement happens quickly in manufacturing networks. Many factory networks were designed for operational efficiency, not security. Systems often share credentials, lack proper access controls, and trust connections from other devices on the network.
The most dangerous aspect is that OT ransomware protection requires different strategies than traditional IT security. Standard antivirus software can’t run on many industrial systems, and security patches often require production shutdowns to install.
The True Cost of Manufacturing Production Downtime
Production downtime cyberattacks create costs that extend far beyond the immediate ransom demand. Manufacturing business continuity depends on understanding and preparing for these broader financial impacts.
Direct operational costs hit immediately:
• Lost production revenue during shutdown periods
• Overtime costs to catch up on delayed orders
• Emergency contractor fees for system recovery
• Expedited shipping costs to meet customer commitments
• Raw material waste from interrupted processes
Supply chain penalties compound the damage. Many manufacturing contracts include strict delivery requirements with financial penalties for delays. A three-day ransomware shutdown might trigger penalty clauses worth hundreds of thousands of dollars.
Customer relationship costs last longer than the attack. When manufacturers can’t deliver on time, customers start looking for alternative suppliers. Rebuilding trust and winning back lost business often takes months or years.
Regulatory and compliance issues add complexity. Manufacturing companies in regulated industries face additional scrutiny after cyberattacks. Safety inspections, compliance audits, and regulatory reporting requirements create ongoing costs and operational disruptions.
Insurance gaps leave manufacturers exposed. Many traditional business insurance policies don’t adequately cover cyber-related production losses. The gap between cyber insurance limits and actual downtime costs can be substantial.
One mid-sized automotive supplier we worked with faced $2.3 million in total costs from a four-day ransomware attack, even though the actual ransom demand was only $75,000. The majority of costs came from production delays, customer penalties, and emergency recovery efforts.
Building Effective Factory Ransomware Prevention
Factory ransomware prevention requires a layered approach that addresses both traditional IT security and the unique challenges of operational technology environments. The goal isn’t just protecting data – it’s ensuring production continuity.

OT network segmentation security forms the foundation. Properly separating your corporate network from production systems creates the strongest barrier against ransomware spread. This means implementing firewalls, access controls, and monitoring between IT and OT environments.
Essential prevention components include:
• Air-gapped backups stored offline and tested regularly for production system recovery
• Vendor access controls that limit and monitor third-party connections to factory systems
• Employee training focused on manufacturing-specific phishing and social engineering tactics
• Asset inventory management to track all connected devices in both IT and OT environments
• Patch management programs that balance security updates with production requirements
Industrial control system security needs specialized attention. Many PLCs, HMIs, and SCADA systems can’t run traditional security software. Instead, focus on network-based monitoring and anomaly detection that can identify unusual behavior without impacting operations.
Access control becomes critical in manufacturing environments. Implement role-based permissions that limit who can access production systems. Engineering workstations that bridge IT and OT networks need especially strict controls and monitoring.
Regular security assessments help identify vulnerabilities before attackers do. Manufacturing environments change frequently with new equipment, software updates, and process modifications. Quarterly assessments ensure your defenses keep pace with these changes.
The key is working with a reliable partner who understands both IT security and manufacturing operations. Same-day support becomes crucial when production systems are at risk, and 24/7 monitoring helps catch threats before they can spread to critical equipment.
Manufacturing Cyber Resilience and Recovery Planning
Manufacturing cyber resilience goes beyond prevention – it’s about maintaining operations even when attacks succeed. The best defense includes planning for business continuity when ransomware impacts production systems.

Incident response planning for manufacturing environments requires specialized procedures. Unlike typical IT incidents, OT ransomware attacks involve safety considerations, regulatory requirements, and complex system dependencies that affect recovery priorities.
Critical elements of manufacturing incident response:
• Production priority matrices that define which systems to restore first based on business impact
• Manual operation procedures for continuing production when automated systems are compromised
• Vendor contact lists with emergency support numbers for critical equipment manufacturers
• Regulatory notification requirements specific to your industry and location
• Communication plans that keep customers, suppliers, and stakeholders informed during incidents
Backup and recovery strategies need to address OT-specific challenges. Industrial systems often require specialized backup procedures, and recovery times can be longer due to safety testing and validation requirements.
Testing your incident response plan reveals gaps before real attacks occur. Run tabletop exercises that simulate ransomware scenarios affecting different production areas. Include both IT and operations teams in these exercises to ensure coordination.
Building relationships with the right partners provides peace of mind during crises. Look for cybersecurity providers with industry expertise in manufacturing environments. Straightforward pricing for emergency response services helps you budget for potential incidents.
The goal is to achieve cyber resilience that keeps your business running even when facing sophisticated threats. This means combining proactive solutions with rapid response capabilities and clear recovery procedures.
Our experience with manufacturing clients shows that companies with comprehensive incident response plans recover 60% faster than those without documented procedures. The investment in planning pays for itself during the first incident.
Frequently Asked Questions
How quickly can ransomware shut down a manufacturing facility?
Ransomware can halt production within 2-4 hours once it reaches operational technology systems. The speed depends on network architecture and how quickly the malware spreads from IT to OT environments.
What’s the difference between IT and OT security in manufacturing?
IT security protects data and business systems, while OT security focuses on operational technology that controls physical processes. OT systems often can’t run traditional security software and require specialized protection strategies.
Should manufacturers pay ransomware demands to restore production?
Paying ransoms doesn’t guarantee system restoration and funds for future attacks. Focus on prevention, backups, and incident response planning instead of relying on ransom payments for recovery.
How often should manufacturing companies test their cybersecurity defenses?
Conduct quarterly security assessments and annual penetration testing for manufacturing environments. Test incident response procedures every six months with tabletop exercises involving both IT and operations teams.
Can cyber insurance cover manufacturing production downtime losses?
Standard cyber policies often have limited coverage for operational downtime. Review your policy carefully and consider specialized manufacturing cyber insurance that covers production losses and supply chain disruptions.
What’s the biggest cybersecurity mistake manufacturing companies make?
Treating OT security as an IT problem. Manufacturing cybersecurity requires understanding industrial systems, safety requirements, and operational priorities that differ significantly from traditional business environments.
How long does it typically take to recover from a manufacturing ransomware attack?
Recovery times range from 3-14 days depending on backup quality, system complexity, and incident response preparedness. Companies with tested recovery plans typically restore operations 60% faster than those without documented procedures.
Do small manufacturing companies need the same cybersecurity as large enterprises?
Small manufacturers face the same threats but need proportional solutions. Focus on network segmentation, employee training, and reliable backup systems rather than trying to implement enterprise-scale security programs.
What role do equipment vendors play in manufacturing cybersecurity?
Vendors often require remote access for maintenance and support, creating potential attack vectors. Implement strict vendor access controls, monitor all third-party connections, and require cybersecurity standards in vendor contracts.
How can manufacturers balance cybersecurity with operational efficiency?
Effective manufacturing cybersecurity enhances rather than hinders operations by preventing costly downtime. Work with providers who understand manufacturing environments and can implement security without disrupting production processes.
Manufacturing Ransomware Risk Assessment
Evaluate your facility's vulnerability to ransomware attacks
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free ConsultationConclusion
Ransomware in manufacturing represents one of the most serious operational threats facing production facilities today. The combination of legacy systems, network connectivity, and operational pressure creates perfect conditions for attackers to cause maximum damage through production shutdowns.
The path forward requires understanding that manufacturing cybersecurity is fundamentally different from traditional IT security. Your operational technology systems need specialized protection strategies that balance security with production requirements. Network segmentation, isolated backups, and manufacturing-specific incident response plans form the foundation of effective defense.
Remember that the goal isn’t just protecting data – it’s ensuring production continuity. Every hour of downtime costs your business revenue, customer relationships, and competitive advantage. Investing in proper cybersecurity defenses pays for itself by preventing these costly shutdowns.
Working with a reliable partner who understands manufacturing environments makes all the difference. Look for providers who offer industry expertise, 24/7 monitoring, and same-day support when production systems are at risk. The peace of mind that comes from knowing your facility is properly protected allows you to focus on what you do best – manufacturing quality products.
Don’t wait for an attack to test your defenses. Start with a comprehensive security assessment that covers both your IT and OT environments. Identify vulnerabilities before attackers do, and build the cyber resilience your manufacturing business needs to thrive in 2026 and beyond.
Ready to protect your manufacturing facility from ransomware attacks? Contact AlphaCIS today for a comprehensive manufacturing cybersecurity assessment. Our team understands the unique challenges of industrial environments and can help you build defenses that protect production without disrupting operations.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity