Article Summary
• Who this is for: Manufacturing business owners, plant managers, and operations leaders relying on legacy systems to run production environments
• The challenge: Outdated manufacturing software and unsupported operating systems create serious cybersecurity vulnerabilities, while upgrades feel risky, expensive, and disruptive to production
• Key insights covered: How legacy systems expose factories to ransomware attacks, why unsupported software cannot be patched, common industrial security gaps, real operational risks, and practical protection strategies like network segmentation and phased modernization
• Your outcome: A clear understanding of how to reduce cybersecurity risk in manufacturing environments without shutting down operations, plus actionable steps to protect production systems while planning long-term modernization
Quick Answer
Legacy software in manufacturing creates serious cybersecurity vulnerabilities because these systems often run on unsupported operating systems, use default passwords, lack encryption, and cannot receive security patches. These outdated manufacturing software risks expose factories to ransomware attacks, production shutdowns, and compliance violations that can cost millions in downtime and recovery.
Key Takeaways
• Legacy systems are everywhere: Most manufacturing facilities still rely on software that’s 10-20 years old with zero vendor support
• Patching is impossible: Unsupported software manufacturing systems can’t receive critical security updates, leaving known vulnerabilities exposed
• Attackers know this: Cybercriminals specifically target industrial environments because legacy systems’ cybersecurity is often weak or nonexistent
• Downtime costs millions: A single ransomware attack on factory cybersecurity risks can shut down production for weeks
• Compliance pressure is mounting: Insurance companies and regulators are demanding better operational technology security risk management
• Network segmentation helps: You don’t need to replace everything immediately – smart isolation can reduce industrial control system vulnerabilities
• Gradual modernization works: A phased approach to upgrading OT legacy systems’ security is more practical than wholesale replacement
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
What Counts as Legacy Software in Manufacturing?
Legacy software in manufacturing includes any system that no longer receives vendor support, security updates, or compatibility patches. This typically means software that’s more than 10 years old, though some systems become “legacy” much faster.
Here’s what we commonly see in manufacturing facilities:
Operating Systems:
- Windows XP (ended support in 2014)
- Windows 7 (ended support in 2020)
- Windows Server 2008/2012
- Legacy Unix variants
Industrial Applications:
- Older HMI (Human Machine Interface) software
- Supervisory Control and Data Acquisition (SCADA) systems
- Manufacturing Execution Systems (MES) from the early 2000s
- Plant historians and data collection software
- Custom applications built on outdated frameworks
Embedded Systems:
- Programmable Logic Controllers (PLCs) with outdated firmware
- Industrial PCs running ancient software
- Robotic control systems
- Safety instrumented systems
The challenge isn’t just age – it’s that these systems were designed for reliability and uptime, not cybersecurity. Many were installed when manufacturing networks were completely isolated from the internet. That’s no longer the case.
Why Legacy Systems Still Dominate Manufacturing Floors
You might wonder why manufacturers haven’t simply upgraded their software. The reality is more complex than “if it ain’t broke, don’t fix it.”
Production downtime fears top the list of concerns. Manufacturing executives know that upgrading critical systems means potential weeks of downtime. When a production line generates $50,000 per hour, even a planned weekend upgrade feels risky.
Massive replacement costs make modernization daunting. We’re not talking about upgrading a few computers – entire production lines might need new PLCs, HMIs, and control systems. The price tag can easily reach millions for a single facility.
Integration complexity creates additional headaches. Legacy systems often use proprietary protocols and custom interfaces. New software might not communicate with existing equipment, forcing companies to replace perfectly functional machinery.
Regulatory validation adds another layer of difficulty. In industries such as pharmaceuticals and automotive, any system change requires extensive testing and documentation to maintain compliance certifications.
Skills gaps compound the problem. Many plant engineers learned these legacy systems decades ago. Training staff on new platforms takes time and money that many companies struggle to allocate.
The result? Manufacturing facilities continue running software that poses serious security risks because the alternatives seem even more risky or expensive.
The Hidden Cybersecurity Risks Lurking in Your Factory

Unsupported Operating Systems Create Open Doors
When Microsoft ended support for Windows XP in 2014, millions of manufacturing systems became permanently vulnerable. These unsupported software manufacturing environments can’t receive security patches, even when critical vulnerabilities are discovered.
The WannaCry wake-up call in 2017 showed how devastating this can be. The ransomware specifically targeted Windows XP systems, shutting down production at major manufacturers worldwide. Companies that had delayed upgrades paid the price with weeks of downtime.
Zero-day vulnerabilities become permanent threats on unsupported systems. When security researchers discover new attack methods, there’s no fix coming. Your system remains vulnerable forever.
Compliance violations multiply when you’re running unsupported software. Cyber insurance policies increasingly exclude coverage for incidents involving legacy systems. Regulatory frameworks like NIST are pushing for modern security standards that legacy systems simply can’t meet.
Default Credentials: The Keys Hackers Love
Industrial control system vulnerabilities often start with something embarrassingly simple: default usernames and passwords that were never changed.
Common default combinations like “admin/admin” or “operator/password” are well-known to attackers. Many legacy systems shipped with these credentials, and busy plant engineers never got around to changing them.
Hardcoded passwords in older software can’t be changed at all. Some legacy applications have authentication credentials built into the code itself. Even if you wanted to improve security, the software won’t let you.
Shared service accounts create additional risks. Legacy systems often use a single “service” account for multiple functions, making it impossible to track who did what or revoke access for specific users.
Network Exposure: When Air Gaps Disappear
The myth of the “air-gapped” factory network died years ago. Modern manufacturing demands connectivity for supply chain integration, remote monitoring, and data analytics. This connectivity exposes OT legacy systems’ security weaknesses to internet-based attacks.
Remote access tools installed during COVID-19 often bypassed security protocols. Many companies set up VPNs and remote desktop connections quickly, without properly segmenting legacy systems from these new access points.
IoT device proliferation creates new attack vectors. Smart sensors, wireless monitoring devices, and connected maintenance tools all communicate with legacy systems that weren’t designed to handle modern network traffic securely.
Supply chain connections require network links to vendors, customers, and logistics providers. Each connection potentially exposes your legacy systems to threats from external networks with different security standards.
Encryption: The Protection That Doesn’t Exist
Most legacy manufacturing software predates modern encryption standards. Data travels across your network in plain text, making it easy for attackers to intercept and manipulate.
Unencrypted communications between HMIs and PLCs can be captured and replayed by attackers. This allows cybercriminals to send malicious commands to your equipment or steal sensitive production data.
Stored data vulnerabilities mean that production recipes, quality data, and operational parameters sit unprotected on legacy servers. A single compromised system can expose years of valuable intellectual property.
Authentication weaknesses in legacy protocols make it easy for attackers to impersonate legitimate users or systems. Many older industrial protocols were designed for reliability, not security.
Real Operational Risks: Beyond IT Headaches
Production Downtime That Costs Millions
Manufacturing ransomware vulnerabilities don’t just threaten your computers – they can shut down entire production lines. Unlike office environments, where people can work with pen and paper temporarily, manufacturing requires functioning control systems.
Recovery complexity makes downtime especially painful. Even if you pay the ransom (which we never recommend), restoring complex manufacturing systems takes far longer than typical office computers. You’re looking at weeks, not hours.
Supply chain disruption multiplies the impact. When your production stops, it affects customers, suppliers, and partners. The reputational damage and contract penalties often exceed the direct costs of the attack itself.
Safety system failures create life-threatening situations. If ransomware compromises safety instrumented systems or emergency shutdown procedures, you’re facing potential injuries or environmental incidents alongside the cybersecurity crisis.
Data Theft and Intellectual Property Loss
Attackers increasingly target manufacturing companies for valuable intellectual property rather than just ransom payments. Your legacy systems likely contain decades of proprietary information.
Production recipes and formulas represent millions in research and development investment. Competitors would pay handsomely for your manufacturing processes, quality parameters, and operational know-how.
Customer and supplier data stored on legacy systems often lacks proper access controls. A single breach can expose sensitive information about your entire business ecosystem.
Operational intelligence reveals competitive advantages like production costs, efficiency metrics, and capacity planning. This information helps competitors undercut your pricing or poach your customers.
Regulatory and Insurance Consequences
Manufacturing compliance cybersecurity requirements are tightening rapidly. Legacy systems that can’t meet modern security standards create serious legal and financial exposure.
Cyber insurance exclusions increasingly apply to incidents involving unsupported software. Your policy might not cover ransomware attacks that exploit known vulnerabilities in legacy systems.
Regulatory fines multiply when data breaches involve inadequate security measures. Agencies view running unsupported software as negligent, leading to higher penalties and more scrutiny.
Customer requirements for cybersecurity certifications can disqualify you from major contracts. Many large manufacturers now require suppliers to demonstrate modern security practices before awarding business.
Why Attackers Love Targeting Legacy Manufacturing Environments
Cybercriminals specifically target manufacturing companies because they understand the unique vulnerabilities and high-value targets that legacy systems represent.
Predictable vulnerabilities make attacks easier to plan. Hackers know that Windows XP systems in manufacturing facilities can’t be patched, so they focus on exploits that target these known weaknesses.
High-value targets justify the effort required for sophisticated attacks. Manufacturing companies typically have valuable intellectual property, critical infrastructure that can’t afford downtime, and the financial resources to pay large ransoms.
Limited security expertise in operational technology makes detection and response more difficult. Many manufacturing companies have strong IT security but lack OT-focused cybersecurity professionals who understand industrial control systems.
Interconnected systems amplify attack impact. Once attackers gain access to one legacy system, they can often move laterally through poorly segmented networks to compromise multiple production lines or facilities.
Regulatory pressure to maintain uptime makes companies more likely to pay ransoms rather than endure lengthy recovery processes. Attackers know that production downtime creates intense pressure to resolve incidents quickly.
Risk Mitigation Strategies: Protecting What You Can’t Replace
You don’t need to replace every legacy system immediately to improve your security posture. Smart risk management can significantly reduce industrial system patching challenges while you plan longer-term modernization.
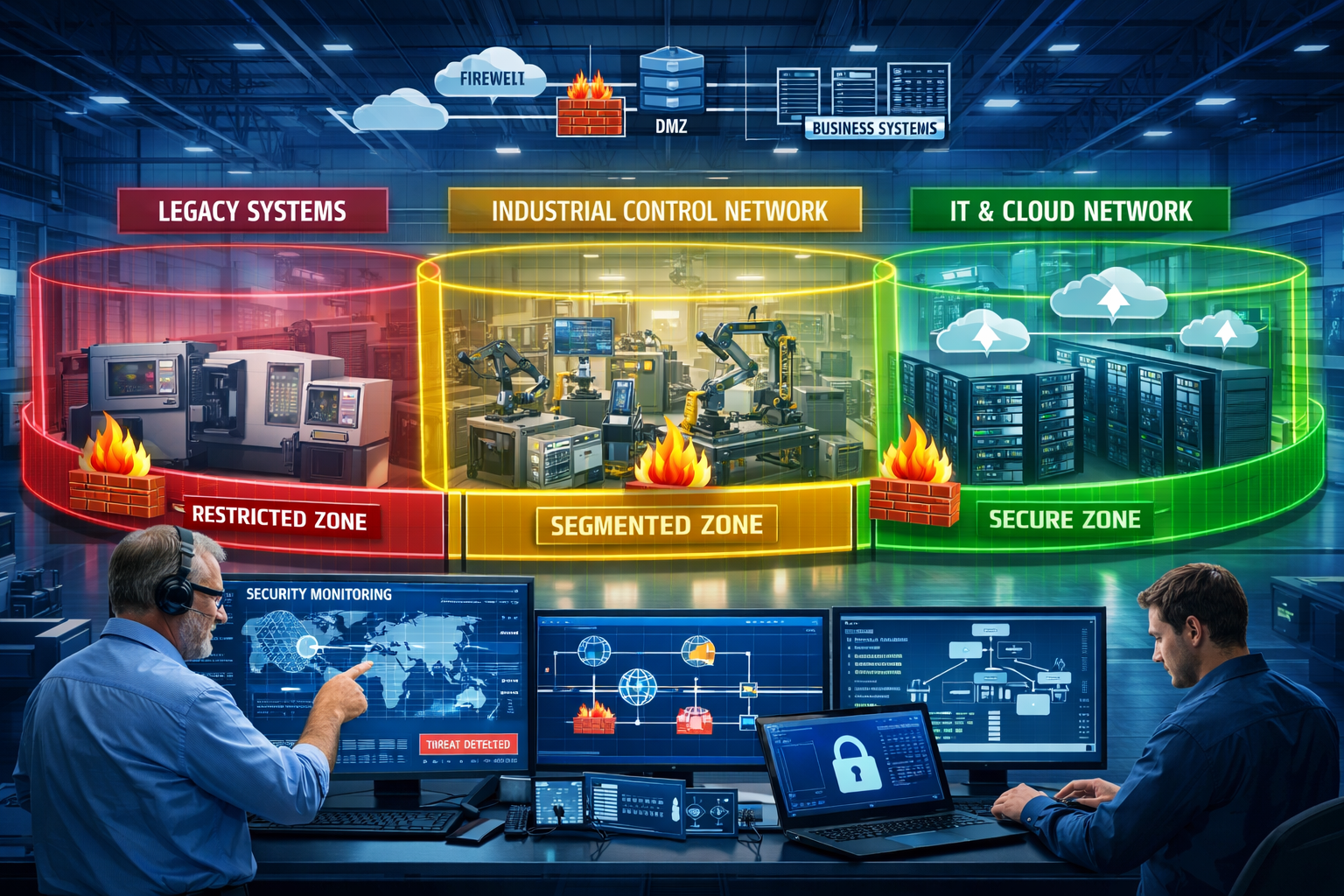
Network Segmentation: Your First Line of Defense
Network segmentation isolates legacy systems from both external threats and internal network traffic that could spread malware. This approach provides immediate security improvements without touching production systems.
Create security zones that group systems by risk level and function. Legacy production systems should be in the most restricted zone, with carefully controlled access points and monitoring.
Implement firewall rules that block unnecessary communications between zones. Legacy systems rarely need internet access or communication with office networks, so these connections can be safely severed.
Monitor all traffic between zones to detect unusual activity. Even if attackers compromise one system, proper segmentation and monitoring can prevent lateral movement to other critical assets.
Use jump boxes for necessary remote access. Instead of connecting directly to legacy systems, administrators access a hardened intermediary system that logs all activities and applies additional security controls.
Virtual Patching: Protection Without System Changes
Virtual patching uses network-based security tools to block attacks against known vulnerabilities without modifying the vulnerable systems themselves. This approach works particularly well for operational technology security risks.
Intrusion prevention systems can detect and block exploit attempts targeting specific vulnerabilities in legacy software. These systems sit on the network and don’t require any changes to production systems.
Application-aware firewalls understand industrial protocols and can filter malicious commands while allowing legitimate traffic. This provides granular protection for legacy HMI and SCADA systems.
Behavioral monitoring establishes baselines for normal system behavior and alerts on deviations that might indicate compromise. This helps detect attacks that bypass traditional signature-based security tools.
Enhanced Monitoring and Detection
Legacy systems often provide limited logging and monitoring capabilities, but network-based tools can fill these gaps and provide visibility into potential security incidents.
Network traffic analysis reveals communication patterns and can detect malicious activity even when endpoint logging is unavailable. This is crucial for legacy systems that provide minimal security event data.
Asset discovery and inventory tools help you understand exactly what legacy systems exist on your network and their current patch levels. You can’t protect what you don’t know about.
Threat intelligence integration helps security teams understand which vulnerabilities in your legacy systems are being actively exploited by attackers. This allows you to prioritize protective measures.
24/7 monitoring services provide the specialized expertise needed to detect and respond to OT-focused attacks. Many manufacturing companies lack the internal resources to monitor operational technology security risks around the clock.
At AlphaCIS, we’ve helped numerous Metro Atlanta manufacturers implement these monitoring solutions with same-day support and 24/7 monitoring that provides real peace of mind. Our industry expertise in operational technology means we understand the unique challenges of protecting legacy manufacturing systems.
Controlled Modernization: Strategic Upgrades
Rather than attempting wholesale system replacement, focus on upgrading the most critical and vulnerable components first. This approach balances security improvements with operational stability.
Risk-based prioritization helps you identify which legacy systems pose the greatest threat to your operations. Systems with known vulnerabilities, internet connectivity, or access to sensitive data should be upgraded first.
Pilot programs allow you to test new technologies on non-critical systems before implementing them in production environments. This reduces the risk of unexpected compatibility issues or downtime.
Vendor partnerships can provide migration paths and support for legacy system upgrades. Many industrial software vendors offer specialized services for modernizing older installations with minimal disruption.
Phased implementation spreads costs and risks over multiple budget cycles while providing incremental security improvements. Each phase builds on previous successes and lessons learned.
Long-term Modernization Roadmap: Planning Your Digital Transformation
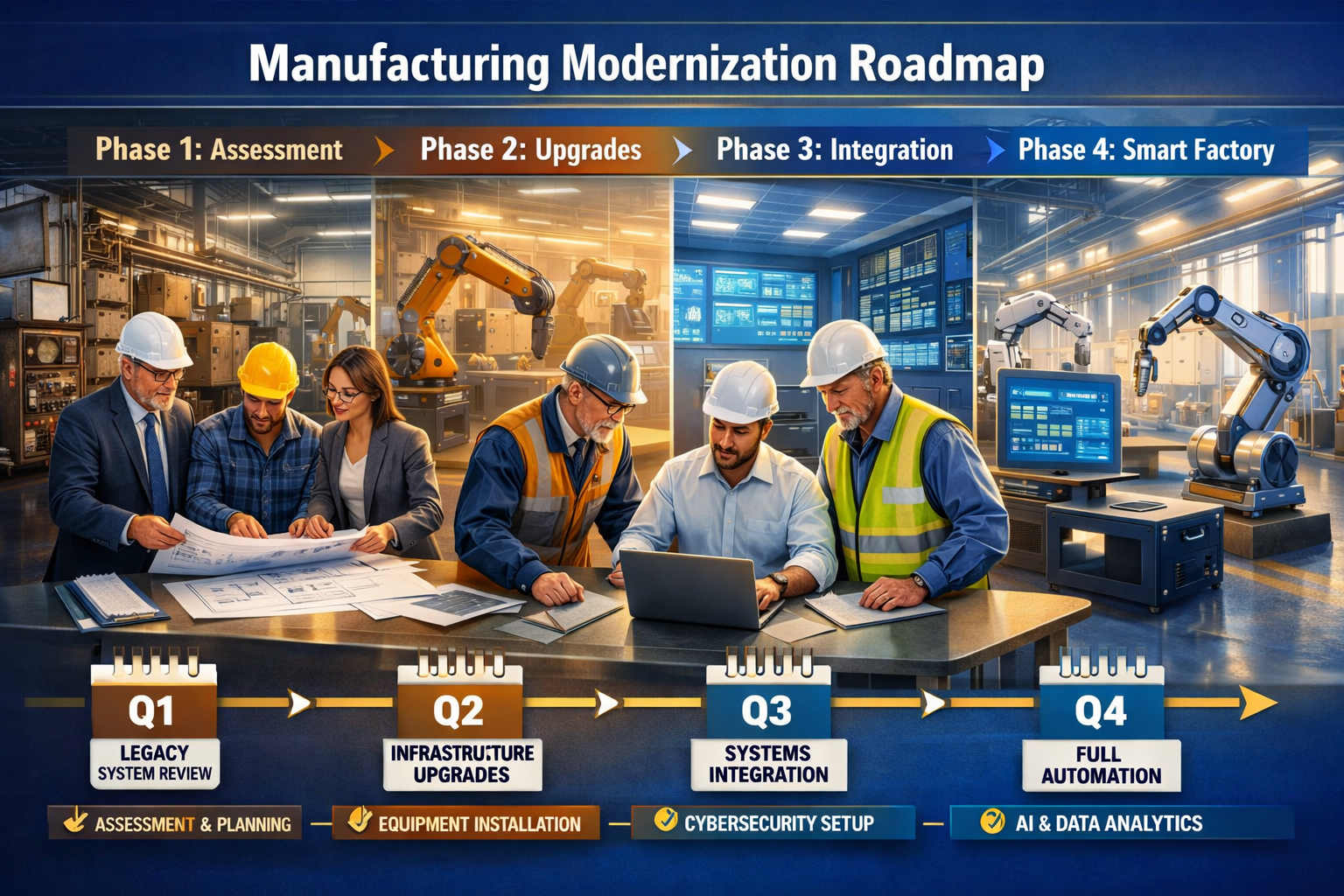
Creating a comprehensive plan for legacy system modernization helps you balance security needs with operational requirements and budget constraints. The key is developing a realistic timeline that prioritizes the most critical upgrades while maintaining production stability.
Assessment and Planning Phase (Months 1-3)
Start with a comprehensive inventory of all legacy systems, their vulnerabilities, and their business criticality. This assessment forms the foundation for all future modernization decisions.
Document the current state of each system, including hardware, software versions, network connections, and security controls. Many manufacturers are surprised by what they discover during this process.
Identify quick wins that can improve security without major system changes. Sometimes, simple configuration changes or additional monitoring can significantly reduce risk.
Establish success metrics that balance security improvements with operational requirements. Metrics might include reduced vulnerability counts, improved incident response times, or enhanced compliance scores.
Budget planning should account for both direct replacement costs and indirect expenses like training, downtime, and validation activities. Many companies underestimate the total cost of modernization projects.
Infrastructure Modernization (Months 4-12)
Focus on foundational improvements that support both current operations and future upgrades. Network infrastructure, security tools, and monitoring capabilities provide immediate benefits while enabling future modernization efforts.
Network redesign creates proper segmentation and security zones before upgrading individual systems. This approach provides immediate security benefits and simplifies future upgrades.
Security tool deployment includes firewalls, intrusion detection systems, and monitoring solutions designed for operational technology environments. These tools provide protection for legacy systems while you plan their replacement.
Backup and recovery systems ensure you can quickly restore operations if modernization efforts encounter problems. This reduces the risk of extended downtime during upgrade projects.
Systematic System Replacement (Years 2-3)
Begin replacing the most critical legacy systems with modern, secure alternatives. Prioritize systems that pose the greatest security risks or have the highest business impact.
Start with edge systems that have fewer dependencies and integration requirements. Success with these systems builds confidence and expertise for more complex upgrades later.
Maintain parallel operations during transitions to minimize downtime risk. Run old and new systems simultaneously until you’re confident the new system meets all operational requirements.
Document everything, including configuration details, integration procedures, and lessons learned. This documentation accelerates future upgrade projects and helps with staff training.
Validate thoroughly before decommissioning legacy systems. In regulated industries, this validation process can take months and requires extensive documentation.
Continuous Improvement and Maintenance (Ongoing)
Modern systems require ongoing maintenance and updates to remain secure. Establish processes and procedures that prevent your new systems from becoming tomorrow’s legacy vulnerabilities.
Patch management procedures ensure that security updates are tested and deployed promptly. This includes both operating system patches and application updates.
Regular security assessments identify new vulnerabilities and validate the effectiveness of existing security controls. The threat landscape evolves constantly, and your defenses must evolve too.
Staff training keeps your team current with new technologies and security practices. The human element remains crucial for maintaining secure operations.
Vendor management includes regular reviews of support contracts, security practices, and long-term product roadmaps. You want to avoid creating new legacy systems by choosing vendors and products with strong long-term viability.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free ConsultationConclusion
Legacy software risks in manufacturing represent one of the most significant cybersecurity challenges facing industrial companies in 2026. While these outdated manufacturing software risks can’t be eliminated overnight, smart risk management strategies can dramatically reduce your exposure while you plan systematic modernization.
The key is understanding that you don’t need to choose between security and operational stability. Network segmentation, virtual patching, enhanced monitoring, and controlled modernization provide practical paths forward that protect your operations without unnecessary downtime.
Start with an assessment to understand your current risk landscape. Implement quick wins like network segmentation and monitoring that provide immediate benefits. Plan systematically for long-term modernization that balances security needs with operational requirements.
Most importantly, don’t try to tackle these challenges alone. Partner with cybersecurity professionals who understand both manufacturing operations and the unique requirements of operational technology security. The cost of expert guidance is minimal compared to the potential impact of a successful cyberattack on your production systems.
Your legacy systems served you well for decades – now it’s time to protect them while building the secure, modern infrastructure that will serve your business for decades to come.
Legacy Manufacturing System Risk Assessment
Answer these questions to evaluate your cybersecurity risk level
Recommended Actions:
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity