Article Summary
• Who this is for: Manufacturing leaders, plant managers, and industrial engineers responsible for protecting PLCs, HMIs, and operational technology (OT) systems that run production environments
• The challenge: Modern manufacturing systems are increasingly connected to IT networks, remote vendors, and cloud platforms, exposing PLCs and HMIs to cyber threats they were never designed to defend against
• Key insights covered: How cybercriminals target industrial control systems, the risks of unsegmented OT networks, common attack vectors like remote access and outdated firmware, and essential security strategies such as network segmentation, monitoring, and secure vendor access
• Your outcome: A clear understanding of how to reduce cybersecurity risks in manufacturing environments and practical steps to protect production systems from costly downtime and operational disruption
Quick Answer
Protecting PLCs and HMIs from cyber threats requires a multi-layered approach combining network segmentation, access controls, regular patching, and continuous monitoring. Modern industrial control systems face increasing cyber risks that can cause costly production downtime, making proactive OT cybersecurity protection essential for manufacturing operations.
Key Takeaways
• Network segmentation is your first line of defense – separate OT networks from IT systems and the internet
• Access control prevents unauthorized users from reaching critical industrial systems
• Regular monitoring helps detect threats before they impact production
• Patch management keeps firmware updated while minimizing operational disruption
• Backup configurations ensure quick recovery if systems are compromised
• IT-OT collaboration bridges the gap between cybersecurity expertise and operational knowledge
• Risk assessment identifies vulnerabilities specific to your manufacturing environment
• Vendor access controls secure remote connections without blocking necessary support
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
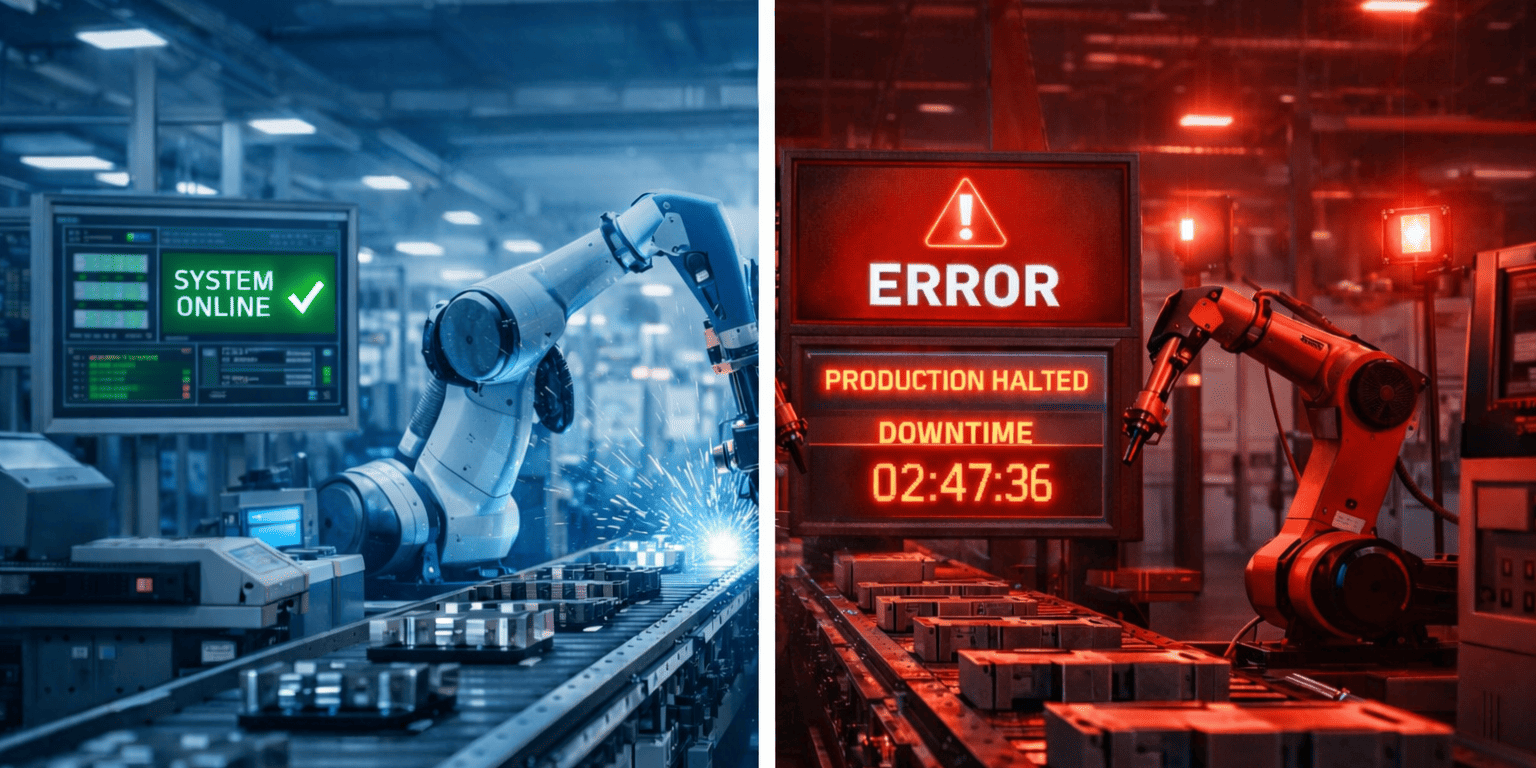
📅 Book Your Free ConsultationPicture this: It’s Monday morning, and your production line has been down for six hours. The culprit? A cyberattack that infiltrated through an unprotected HMI, spreading across your entire manufacturing network. What started as a simple phishing email has now cost you hundreds of thousands in lost production.
This scenario isn’t hypothetical anymore. Manufacturing facilities across the country are discovering that their industrial control systems – the PLCs and HMIs that run their operations – have become prime targets for cybercriminals. The challenge is that most of these systems were designed for reliability and efficiency, not security.
What PLCs and HMIs Actually Control in Your Facility
Programmable Logic Controllers (PLCs) and Human Machine Interfaces (HMIs) form the backbone of modern manufacturing operations. These systems control everything from conveyor belts and robotic arms to temperature regulation and quality control processes.
PLCs act as the “brain” of your production equipment, executing programmed logic to control machinery based on sensor inputs. HMIs provide the visual interface where operators monitor processes, adjust parameters, and respond to alarms. Together, they manage critical functions like:
Production Control Systems:
• Assembly line speed and sequencing
• Material handling and inventory tracking
• Quality control and inspection processes
• Equipment startup and shutdown procedures
Safety and Environmental Systems:
• Emergency shutdown systems
• Fire suppression and gas detection
• Environmental monitoring and compliance
• Worker safety interlocks and barriers
Utility and Infrastructure:
• Power distribution and load management
• HVAC and facility climate control
• Water treatment and waste management
• Compressed air and hydraulic systems
The interconnected nature of these systems means that compromising one component can cascade throughout your entire operation. When cybercriminals target these systems, they’re not just after data – they’re after operational disruption that can cost millions in downtime.
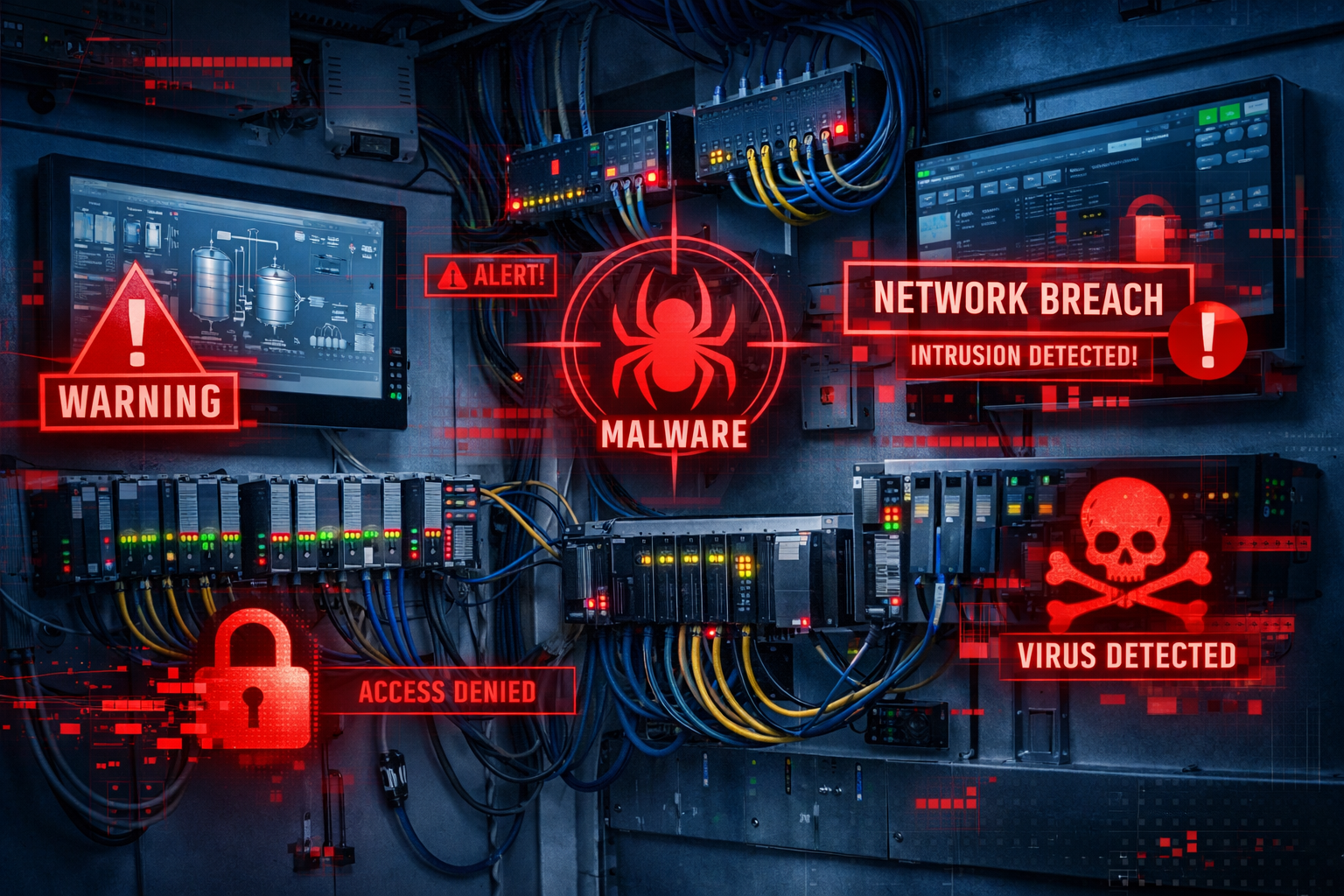
Why Manufacturing Systems Have Become Cyber Targets
Industrial control systems weren’t built with cybersecurity in mind. Most PLCs and HMIs were designed during an era when these systems operated in isolation, connected only to other industrial equipment through proprietary protocols.
The connectivity revolution changed everything. Modern manufacturing demands integration with enterprise systems, remote monitoring capabilities, and real-time data analytics. This connectivity brings tremendous operational benefits but also creates new attack vectors that cybercriminals actively exploit.
Financial motivation drives most attacks. Ransomware groups specifically target manufacturing because production downtime creates immediate pressure to pay. A single day of stopped production can cost more than the ransom demand, making manufacturers attractive targets.
Limited security visibility makes detection difficult. Unlike traditional IT networks, many manufacturing environments lack proper monitoring tools. This means attacks can persist for weeks or months before detection, giving attackers time to map systems and plan maximum disruption.
The result is a perfect storm: valuable targets with limited defenses and high pressure to restore operations quickly after an attack.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free ConsultationUnderstanding Common Attack Vectors Against Industrial Systems
Cybercriminals use several proven methods to infiltrate manufacturing networks and compromise PLCs and HMIs. Understanding these attack vectors helps you build more effective defenses.
Remote Access Compromise
Many manufacturers provide remote access for vendor support, system updates, and off-site monitoring. These connections often bypass normal security controls, creating direct pathways into industrial networks.
Attackers target these access points through:
• Compromised vendor credentials from third-party breaches
• Weak authentication on remote access systems
• Unmonitored VPN connections that remain active indefinitely
• Default passwords on remote access software
Choose secure remote access if: You need vendor support but want to maintain control over when and how external parties access your systems.
Unpatched Firmware Vulnerabilities
Industrial systems often run on firmware that hasn’t been updated in years. Manufacturers hesitate to patch systems during production, creating windows of vulnerability that attackers exploit.
Common firmware risks include:
• Known vulnerabilities with published exploits
• Default credentials that were never changed
• Insecure communication protocols
• Missing security features in older versions
Network Exposure and Lateral Movement
Flat network architectures allow attackers to move freely between systems once they gain initial access. What starts as a compromised office computer can quickly spread to production systems.
Typical exposure patterns:
• Direct internet connections to HMIs for remote monitoring
• Shared network segments between IT and OT systems
• Uncontrolled wireless access points in production areas
• Guest networks that connect to internal systems
USB and Removable Media Infections
Physical media remains a significant threat vector in manufacturing environments. USB drives, maintenance laptops, and even smartphone connections can introduce malware directly to air-gapped systems.
Common mistake: Assuming that air-gapped systems are automatically secure. Malware specifically designed for industrial systems can spread through removable media and activate when connected to target systems.
Real Operational Risks: Why Downtime Matters More Than Data
In manufacturing cybersecurity, the primary concern isn’t data theft – it’s operational disruption. When attackers compromise PLCs and HMIs, the immediate impact is on production capacity, not on information security.
Production Downtime Costs
Manufacturing downtime costs vary by industry, but even small facilities can lose tens of thousands per hour when production stops. Large automotive or chemical plants may face costs exceeding $100,000 per hour of unplanned downtime.
These costs compound quickly:
• Lost production output and missed delivery commitments
• Over time, labor costs to catch up on delayed orders
• Equipment restart and quality validation procedures
• Customer penalties and potential contract losses
• Regulatory reporting requirements for safety-related incidents
Safety System Compromise
Beyond financial losses, compromised industrial control systems can create serious safety risks. Attackers who gain control of safety interlocks, emergency shutdown systems, or environmental controls can create dangerous conditions for workers and surrounding communities.
Supply Chain Disruption
Modern manufacturing operates on just-in-time principles with minimal inventory buffers. When one facility goes down, the impact ripples through entire supply chains, affecting customers, suppliers, and partner companies.
Recovery Complexity
Unlike typical IT systems that can be restored from backups, industrial systems require careful validation before returning to service. This includes:
• Verifying control logic hasn’t been modified
• Testing safety systems and interlocks
• Validating product quality after restart
• Documenting incidents for regulatory compliance
This extended recovery process means that even brief cyberattacks can result in days of production losses.
Essential Security Best Practices for Industrial Control Systems
Protecting PLCs and HMIs requires a systematic approach that balances security with operational requirements. These practices form the foundation of effective industrial cybersecurity protection.

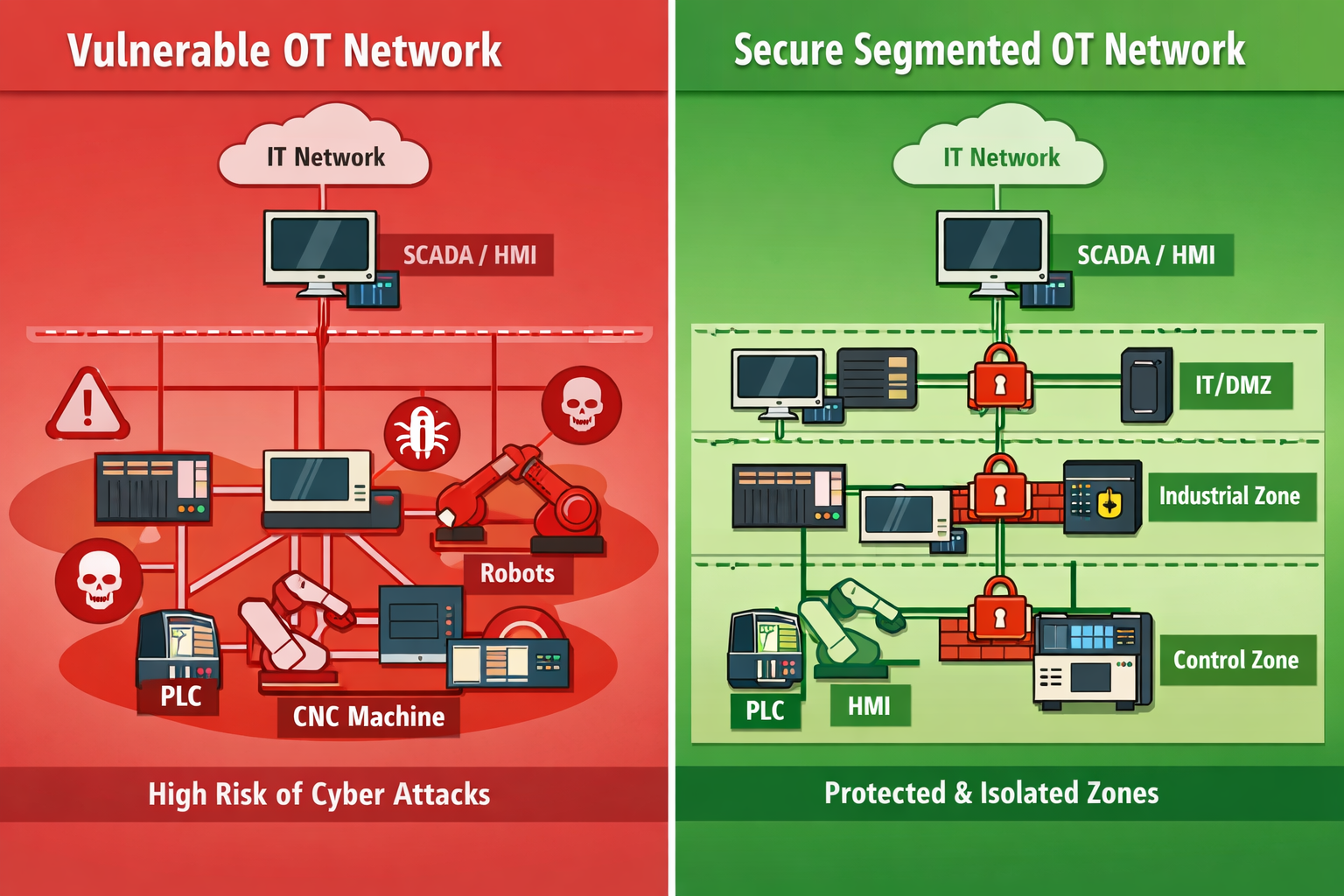
Network Segmentation and Zone Architecture
Network segmentation creates the most critical defense against cyber threats in manufacturing environments. Proper segmentation isolates industrial systems from corporate networks and the internet, limiting how far attackers can spread if they gain initial access.
Implement these segmentation layers:
DMZ for External Connections: Place all internet-facing systems in a demilitarized zone, including remote access servers, data historians, and vendor support systems.
OT Network Isolation: Separate operational technology networks from information technology networks using firewalls with strict access rules.
Production Zone Segmentation: Divide manufacturing areas into security zones based on criticality and function – separate packaging systems from reactor controls, for example.
Device-Level Microsegmentation: Use industrial switches with VLAN capabilities to isolate individual PLCs and HMI systems within production zones.
Choose network segmentation if: You want to limit attack spread and maintain operational control during security incidents.
Access Control and Authentication
Strong access controls ensure that only authorized personnel can interact with critical industrial systems. This includes both physical and logical access to PLCs, HMIs, and supporting infrastructure.
Physical Access Controls:
• Locked control cabinets with audit trails
• Badge-controlled access to production areas
• Security cameras monitoring critical equipment
• Visitor escort requirements in sensitive zones
Logical Access Controls:
• Multi-factor authentication for all system access
• Role-based permissions aligned with job functions
• Regular access reviews and deprovisioning procedures
• Separate accounts for administrative and operational tasks
Common mistake: Using shared accounts or default passwords on industrial systems. Each user should have individual credentials that can be tracked and managed.
Continuous Monitoring and Threat Detection
Traditional antivirus software doesn’t work well in industrial environments, but specialized OT monitoring tools can detect unusual activity and potential threats without impacting production systems.
Deploy monitoring for:
• Unusual network traffic patterns between industrial devices
• Unauthorized configuration changes to PLCs and HMIs
• Failed authentication attempts and privilege escalations
• Communication with external systems or unknown devices
Monitoring should be passive to avoid interfering with real-time control systems. Use network taps or span ports rather than inline devices that could introduce latency or failure points.
Patch Management for Industrial Systems
Keeping industrial systems updated requires careful planning to minimize production disruption while addressing security vulnerabilities.
Develop a structured approach:
Risk Assessment: Evaluate each patch for security impact versus operational risk. Critical security patches take priority over feature updates.
Testing Environment: Maintain a separate test system that mirrors your production environment for validating patches before deployment.
Maintenance Windows: Schedule updates during planned downtime or low-production periods. Coordinate with production planning teams well in advance.
Rollback Procedures: Prepare detailed rollback plans in case patches cause operational issues. Test these procedures in your lab environment.
Emergency Patching: For critical vulnerabilities, develop expedited procedures that can be executed quickly while maintaining safety requirements.
Building Effective IT and OT Collaboration
Successful industrial cybersecurity requires close collaboration between IT security teams and operational technology engineers. These groups traditionally work in separate domains with different priorities, but cyber threats demand unified responses.

Bridge the Knowledge Gap
IT security professionals understand cyber threats and defense strategies, but may lack deep knowledge of industrial processes and safety requirements. OT engineers know production systems intimately but may not fully grasp modern cyber risks.
Create cross-functional teams that include representatives from both domains:
• IT security analysts who understand OT protocols and constraints
• OT engineers trained in cybersecurity fundamentals
• Plant managers who can prioritize security investments
• Maintenance technicians who implement physical security measures
Establish Clear Communication Protocols
Security incidents require rapid response, but industrial environments have strict change control procedures. Develop communication protocols that balance security urgency with operational safety.
Define roles clearly:
• Who has the authority to isolate compromised systems
• How to communicate threats without causing panic
• When to involve external cybersecurity experts
• How to coordinate with law enforcement if needed
Shared Responsibility Model
Rather than treating cybersecurity as purely an IT function, distribute responsibilities based on expertise and system ownership.
IT Security Responsibilities:
• Threat intelligence and vulnerability management
• Network security architecture and monitoring
• Incident response coordination and forensics
• Compliance reporting and documentation
OT Engineering Responsibilities:
• System configuration and change management
• Safety system integrity and validation
• Vendor relationship management
• Production impact assessment
Joint Responsibilities:
• Risk assessment and prioritization
• Security policy development
• Training and awareness programs
• Business continuity planning
This collaborative approach ensures that security measures enhance rather than hinder manufacturing operations, creating sustainable protection that works in real-world production environments.
Securing Remote Vendor Access Without Blocking Support
Manufacturing facilities depend on vendor support for equipment maintenance, software updates, and troubleshooting. However, remote vendor access creates significant security risks that must be carefully managed.
Implement Zero-Trust Vendor Access
Replace always-on VPN connections with just-in-time access that requires approval for each session. This approach gives you control over when vendors can access your systems and what they can do during those sessions.
Key components include:
• Pre-scheduled access windows with defined start and end times
• Approval workflows that require operational staff sign-off
• Session recording for audit and compliance purposes
• Automatic disconnection when maintenance tasks are complete
Use Jump Boxes and Isolation Systems
Create dedicated systems that vendors can access without direct connectivity to your production network. These jump boxes provide the tools vendors need while maintaining network separation.
Benefits of this approach:
• Vendors get necessary system access for support tasks
• Your production network remains isolated from external connections
• All vendor activities can be monitored and recorded
• You maintain control over what systems vendors can reach
Choose jump box solutions if: You need regular vendor support but want to minimize network exposure and maintain detailed access logs.
Establish Vendor Security Requirements
Work with your equipment suppliers to establish minimum cybersecurity standards for remote access. Many vendors are willing to improve their security practices when customers make it a requirement.
Include these requirements in vendor agreements:
• Multi-factor authentication for all remote access
• Regular security training for support personnel
• Incident notification procedures if vendor systems are compromised
• Compliance with your cybersecurity policies during access sessions
Backup Configurations and Recovery Planning
When cyberattacks target industrial systems, having reliable backups and tested recovery procedures can mean the difference between hours of downtime and weeks of disruption.
Configuration Backup Strategy
PLCs and HMIs contain critical configuration data that defines how your production systems operate. Regular backups of this data enable quick recovery if systems are compromised or corrupted.
Back up these critical elements:
• PLC ladder logic and control programs
• HMI screen configurations and alarm settings
• Network device configurations and security policies
• Historical data and production recipes
• Safety system configurations and validation records
Store backups offline to prevent attackers from corrupting both production systems and backup data. Use air-gapped storage or write-once media for critical configuration backups.
Test Recovery Procedures Regularly
Backup data is only valuable if you can actually use it to restore operations. Regular testing validates both your backup data integrity and your team’s ability to execute recovery procedures under pressure.
Include these elements in recovery testing:
• Complete system restoration from backup media
• Validation of safety systems and interlocks after recovery
• Communication procedures during extended outages
• Coordination with suppliers and customers during downtime
Common mistake: Assuming that backups are complete and usable without regular testing. Schedule quarterly recovery drills to identify gaps in your procedures.
FAQ
Q: How often should we update PLC and HMI firmware?
A: Update firmware during scheduled maintenance windows, typically every 6-12 months for non-critical systems and within 30 days for critical security patches. Always test updates in a lab environment first.
Q: Can we use traditional antivirus software on industrial systems?
A: Standard antivirus software can interfere with real-time control systems. Use specialized OT security tools designed for industrial environments that provide protection without impacting operations.
Q: What’s the biggest cybersecurity mistake manufacturers make?
A: Connecting industrial systems directly to corporate networks or the internet without proper segmentation. This creates pathways for attackers to reach critical production systems.
Q: How do we balance security with operational efficiency?
A: Focus on security measures that enhance rather than hinder operations, such as network monitoring that provides operational insights and access controls that improve change management.
Q: Should we hire dedicated OT cybersecurity staff?
A: For larger facilities, dedicated OT security expertise is valuable. Smaller operations can work with specialized partners who understand both cybersecurity and manufacturing requirements.
Q: What should we do if we discover a cyberattack in progress?
A: Immediately isolate affected systems to prevent spread, notify your incident response team, and contact law enforcement if required. Document everything for forensic analysis.
Q: How much should we budget for industrial cybersecurity?
A: Most manufacturers should allocate 3-5% of their IT budget to OT cybersecurity, with higher percentages for facilities handling critical infrastructure or hazardous materials.
Q: Can air-gapped systems still be attacked?
A: Yes, through removable media, supply chain compromises, or insider threats. Air-gapping reduces risk but doesn’t eliminate it.
Q: What compliance requirements apply to manufacturing cybersecurity?
A: Requirements vary by industry and location. Common frameworks include the NIST Cybersecurity Framework, ISO 27001, and industry-specific standards like NERC CIP for power generation.
Q: How do we train operational staff on cybersecurity?
A: Provide practical, scenario-based training that relates to their daily work. Focus on recognizing suspicious activity and following proper procedures rather than technical security details.
Q: What’s the ROI of investing in industrial cybersecurity?
A: Calculate ROI based on avoided downtime costs, which typically range from $50,000 to $500,000 per day, depending on facility size and industry. Even modest security investments pay for themselves quickly.
Q: Should we work with our existing IT provider or find an OT specialist?
A: Look for providers with specific industrial cybersecurity experience. Manufacturing environments have unique requirements that general IT providers may not fully understand.
Conclusion
Protecting PLCs and HMIs from cyber threats isn’t just about technology – it’s about safeguarding your entire manufacturing operation. The strategies we’ve covered provide a roadmap for building robust defenses without sacrificing the operational efficiency that keeps your facility competitive.
The key is starting with the fundamentals: network segmentation, access controls, and monitoring systems that give you visibility into your industrial environment. From there, you can build more sophisticated defenses tailored to your specific risks and operational requirements.
Remember that cybersecurity is an ongoing process, not a one-time project. Threats continue evolving, and your defenses need to evolve with them. Regular assessments, updated procedures, and continuous training ensure that your protection remains effective over time.
Your next step is simple: Assess your current industrial cybersecurity posture and identify the gaps that pose the greatest risk to your operations. Many manufacturers discover that basic improvements in network segmentation and access controls dramatically reduce their exposure to cyber threats.
At AlphaCIS, we understand that manufacturing cybersecurity requires specialized expertise that bridges IT security knowledge with operational technology understanding. Our team has helped manufacturers across Metro Atlanta protect their critical systems while maintaining the operational efficiency that drives their success.
Ready to strengthen your industrial cybersecurity defenses? Let’s discuss your specific challenges and develop a protection strategy that works for your facility. Our industrial cybersecurity assessment identifies vulnerabilities and provides a clear roadmap for improvement – giving you the peace of mind that comes from knowing your production systems are properly protected.
Industrial Cybersecurity Risk Assessment
Evaluate your facility's current protection against cyber threats targeting PLCs and HMIs
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity