Article Summary
• Who this is for: Manufacturing leaders, operations managers, and business owners looking to protect production environments from modern cyber threats
• The challenge: Traditional cybersecurity focuses only on prevention, while manufacturers face operational risks, legacy systems, and downtime costs that require a resilience-first strategy
• Key insights covered: The difference between cybersecurity and cyber resilience, IT/OT security integration, network segmentation, incident response planning, backup and recovery strategies, and emerging manufacturing threat trends for 2026
• Your outcome: A practical roadmap to strengthen operational continuity, reduce ransomware risk, and build a cyber resilience strategy that keeps production running even during cyber incidents
A devastating ransomware attack shut down Colonial Pipeline for six days in 2021, disrupting fuel supplies across the Eastern United States. This wasn’t just an IT problem; it was an operational nightmare that highlighted a critical gap in how manufacturers think about cybersecurity. Building a comprehensive cyber resilience for manufacturers strategy goes far beyond traditional security measures to ensure your operations can withstand, adapt to, and quickly recover from cyber threats while maintaining production continuity.
Key Takeaways
• Cyber resilience differs from cybersecurity – it focuses on maintaining operations during and after attacks, not just preventing them
• Manufacturing faces unique risks with legacy operational technology (OT) systems that weren’t designed with security in mind
• IT and OT integration requires specialized approaches that balance security with operational safety and uptime requirements
• Incident response planning must account for both digital systems and physical production processes
• Network segmentation creates critical barriers between corporate networks and manufacturing operations
• Regular testing and monitoring ensure your resilience plan actually works when you need it most
• Executive leadership drives successful implementation by aligning cybersecurity with business continuity goals
• Compliance requirements are increasing, with cyber insurance demanding stronger security postures
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
What Makes Cyber Resilience Different from Traditional Cybersecurity?
Cyber resilience for manufacturers means your facility can continue operating safely even when under attack. Traditional cybersecurity focuses on building walls to keep threats out. Resilience assumes some threats will get through and prepares your organization to maintain critical functions, respond effectively, and recover quickly.
Think of it this way: cybersecurity is like installing better locks on your doors. Cyber resilience is having backup power, alternative communication methods, and emergency procedures so your business keeps running even if someone breaks in.
For manufacturers, this distinction is crucial because:
Production can’t always stop immediately. Some manufacturing processes take hours or days to shut down safely. Your resilience plan must account for these operational realities while protecting worker safety.
Legacy systems create unique vulnerabilities. Many factories run on operational technology that’s decades old and wasn’t designed with cybersecurity in mind. You need strategies that work with these constraints.
Downtime costs are massive. Every minute of unplanned production stoppage can cost thousands of dollars. A resilient approach minimizes these losses by maintaining partial operations or enabling faster recovery.
The manufacturing cyber resilience strategy we’ll outline helps you build this capability systematically, addressing both immediate threats and long-term operational continuity.
Why Manufacturing Requires a Specialized Approach to Cyber Resilience
Manufacturing environments present unique challenges that standard IT security approaches can’t address. Your factory floor operates under different rules than your corporate office, and your cybersecurity strategy must reflect these realities.
Operational Technology (OT) systems prioritize availability over security. Your programmable logic controllers (PLCs), human-machine interfaces (HMIs), and SCADA systems were designed to keep production running 24/7. Many can’t be patched without shutting down entire production lines, creating a fundamental tension between security and operations.
Safety systems can’t be compromised. Unlike typical IT environments, manufacturing cyber incidents can pose physical safety risks to workers. Your incident response plan must ensure that cybersecurity measures never interfere with emergency shutdown systems or safety protocols.
Legacy systems lack modern security features. Many manufacturers operate equipment that’s 10, 20, or even 30 years old. These systems often lack basic security features like encryption, authentication, or logging capabilities. You need creative solutions that add security layers without replacing critical equipment.
Real-time requirements limit security options. Manufacturing processes often require millisecond response times. Traditional security measures like deep packet inspection or complex authentication can introduce latency that disrupts production quality or safety.
I’ve worked with manufacturers who discovered their main production line was controlled by a Windows XP system that hadn’t been updated in over a decade. Replacing it would cost millions and require months of downtime. Instead, we implemented network segmentation and monitoring solutions that protected the legacy system while maintaining operational requirements.
Your industrial cybersecurity planning must balance these competing demands while building genuine resilience against evolving threats.

Essential Pillars of Manufacturing Cyber Resilience
A robust OT cybersecurity framework rests on five fundamental pillars that work together to protect your operations while maintaining production efficiency. Each pillar addresses specific aspects of manufacturing environments that generic cybersecurity approaches often miss.
Risk Visibility and Asset Management
You can’t protect what you don’t know exists. Many manufacturers lack complete visibility into their operational technology assets, making it impossible to assess and manage cyber risks effectively.
Start with comprehensive asset discovery. Use specialized OT scanning tools that can identify industrial devices without disrupting operations. Document not just what equipment you have, but also how it connects to other systems and what would happen if it failed.
Map data flows between IT and OT systems. Understanding how information moves between your corporate network and production systems helps identify potential attack paths and critical control points.
Assess legacy system vulnerabilities. Create an inventory of systems that can’t be patched or updated, along with compensating controls that reduce their risk exposure.
Establish baseline behaviors. Monitor normal operational patterns so you can quickly identify anomalies that might indicate a cyber incident.
Network Segmentation and Access Control
Proper segmentation creates barriers that prevent cyber threats from spreading between your corporate IT environment and critical production systems.
Implement the Purdue Model architecture. This industry-standard approach creates distinct network zones with controlled communication pathways between corporate systems, manufacturing operations, and safety systems.
Use industrial firewalls and data diodes. Standard IT firewalls often can’t handle industrial protocols or real-time requirements. Specialized equipment designed for manufacturing environments provides better protection without operational disruption.
Control remote access carefully. Many cyber incidents start with compromised remote access credentials. Implement multi-factor authentication, time-limited access, and monitoring for all remote connections to operational systems.
Limit lateral movement opportunities. Even if attackers penetrate your network, proper segmentation prevents them from moving freely between systems or escalating their access to critical controls.
Backup and Recovery Systems
Your manufacturing incident response plan must ensure you can restore operations quickly after a cyber incident, with minimal data loss and production impact.
Protect operational data and configurations. Back up not just corporate data, but also PLC programs, HMI configurations, and historical process data. Store these backups offline or in air-gapped systems that attackers can’t reach.
Test recovery procedures regularly. Practice restoring systems in non-production environments to ensure your backup strategy actually works and your team knows how to execute it under pressure.
Plan for partial operations. Identify which systems are absolutely critical for basic production and which can be temporarily bypassed. This allows you to maintain some output even while recovering from an incident.
Document manual procedures. If automated systems fail, your operators need clear instructions for manual operation modes that maintain safety while preserving critical functions.
Incident Response and Communication
Manufacturing incidents require specialized response procedures that account for both cybersecurity and operational safety considerations.
Establish clear escalation procedures. Define when to involve cybersecurity teams versus operational teams, and ensure everyone understands their roles during an incident.
Coordinate with external partners. Your incident response plan should include contact information for industrial control system vendors, cybersecurity specialists familiar with manufacturing environments, and relevant government agencies.
Maintain communication capabilities. Cyber incidents often disrupt normal communication systems. Establish backup methods for coordinating response activities and communicating with stakeholders.
Practice incident scenarios. Conduct tabletop exercises that simulate realistic manufacturing cyber incidents, including scenarios where you must choose between cybersecurity measures and operational safety.
Continuous Monitoring and Threat Detection
Traditional IT monitoring tools often miss threats targeting operational technology systems. Manufacturing environments require specialized monitoring approaches that understand industrial protocols and operational patterns.
Deploy OT-aware security monitoring. Use tools designed specifically for industrial environments that can detect anomalies in control system communications without impacting performance.
Monitor for insider threats. Manufacturing environments often have many contractors, vendors, and temporary workers with system access. Implement user behavior analytics to identify suspicious activities.
Integrate physical and cyber monitoring. Correlate cybersecurity events with physical security systems, production data, and safety system alerts to get a complete picture of potential threats.
Establish baseline performance metrics. Track key indicators like system availability, response times, and production quality to quickly identify when cyber incidents are affecting operations.
Building Effective IT and OT Collaboration
One of the biggest challenges in manufacturing cybersecurity is bridging the gap between information technology (IT) and operational technology (OT) teams. These groups often have different priorities, vocabularies, and approaches to problem-solving, but successful cyber resilience requires them to work together seamlessly.
Establish shared governance structures. Create cross-functional teams that include representatives from IT, OT, cybersecurity, and operations. These teams should meet regularly to discuss security initiatives, plan system changes, and coordinate incident response activities.
Develop a common language and procedures. IT teams focus on data confidentiality and integrity, while OT teams prioritize availability and safety. Establish clear definitions for terms like “critical system,” “acceptable downtime,” and “emergency response” that both teams understand and agree upon.
Implement change management processes. Any modification to operational systems – whether for security or operational reasons – should follow established procedures that consider both cybersecurity and production impacts. This prevents well-intentioned security measures from inadvertently disrupting operations.
Share threat intelligence effectively. IT teams often receive cybersecurity alerts that don’t clearly indicate whether operational systems are affected. Develop processes for translating threat intelligence into actionable guidance for OT environments.
I’ve seen manufacturers where IT and OT teams worked in complete isolation, each implementing security measures that conflicted with the other’s objectives. The breakthrough came when they started holding weekly “translation meetings” where each team explained their current projects and challenges in terms the other could understand. This simple step dramatically improved their overall security posture while reducing operational friction.
Your cyber risk management manufacturing strategy must account for these organizational dynamics and create structures that encourage collaboration rather than competition between teams.

2026 Threat Landscape Trends Affecting Manufacturers
The cybersecurity threat landscape continues to evolve rapidly, with attackers increasingly targeting manufacturing environments as they recognize the high-value, often vulnerable nature of industrial systems.
Ransomware attacks are becoming more sophisticated. Modern ransomware groups research their targets extensively, customizing attacks for specific industrial environments. They understand which systems you can’t afford to lose and target those for maximum impact.
Supply chain attacks are increasing. Attackers compromise software vendors, equipment manufacturers, or service providers to gain access to multiple manufacturing targets simultaneously. Your third-party risk management must account for these indirect attack vectors.
State-sponsored threats target critical infrastructure. Nation-state actors view manufacturing capabilities as strategic assets and may target them for espionage, sabotage, or positioning for future conflicts.
Insider threats remain significant. Disgruntled employees, compromised credentials, and social engineering attacks continue to be major risk factors, especially in manufacturing environments where operational access is often broadly distributed.
IoT and edge computing create new attack surfaces. As manufacturers adopt more connected devices and edge computing solutions, they create additional entry points that attackers can exploit.
AI-powered attacks are emerging. Sophisticated attackers are beginning to use artificial intelligence to automate reconnaissance, customize phishing attacks, and identify vulnerabilities in industrial systems.
Your operational technology security strategy must evolve to address these emerging threats while maintaining focus on the fundamental security hygiene that prevents most attacks.
Step-by-Step Manufacturing Cybersecurity Roadmap
Building effective ransomware resilience manufacturing capabilities requires a systematic approach that balances immediate risk reduction with long-term strategic improvements. This roadmap provides a practical framework for developing your cyber resilience plan.
Phase 1: Assessment and Foundation (Months 1-3)
Conduct a comprehensive asset inventory. Document all operational technology systems, including legacy equipment, network connections, and critical dependencies. Use specialized OT discovery tools that won’t disrupt production.
Perform risk assessment. Evaluate vulnerabilities in your current environment, focusing on systems that could impact production, safety, or regulatory compliance. Prioritize risks based on potential business impact rather than just technical severity.
Establish baseline security policies. Develop clear guidelines for OT system access, change management, and incident response that account for manufacturing operational requirements.
Begin staff training programs. Educate both IT and OT personnel about cybersecurity threats specific to manufacturing environments and their roles in maintaining security.
Phase 2: Core Protection Implementation (Months 4-8)
Implement network segmentation. Deploy firewalls, switches, and monitoring tools to create proper separation between corporate IT and operational technology networks. Follow the Purdue Model architecture as a starting framework.
Deploy backup and recovery systems. Establish offline backups for critical operational data, including PLC programs, HMI configurations, and historical process data. Test recovery procedures in non-production environments.
Enhance access controls. Implement multi-factor authentication for remote access, establish role-based permissions for operational systems, and deploy privileged access management solutions.
Install monitoring capabilities. Deploy OT-aware security monitoring tools that can detect anomalies in industrial protocols and operational patterns without impacting system performance.
Phase 3: Advanced Capabilities (Months 9-12)
Develop incident response procedures. Create detailed playbooks for responding to cyber incidents affecting manufacturing operations, including coordination between IT, OT, and operational teams.
Implement threat intelligence integration. Establish processes for receiving, analyzing, and acting on cybersecurity threat intelligence relevant to your industry and technology stack.
Enhance vendor risk management. Develop security requirements for third-party vendors with access to operational systems and establish ongoing monitoring of vendor security postures.
Conduct tabletop exercises. Practice incident response procedures through realistic scenarios that test both technical capabilities and organizational coordination.
Phase 4: Optimization and Maturation (Ongoing)
Establish continuous improvement processes. Regularly review and update security measures based on lessons learned, threat landscape changes, and operational evolution.
Expand monitoring and analytics. Implement advanced analytics capabilities that can correlate cybersecurity events with operational data to provide better threat detection and impact assessment.
Develop supply chain security programs. Work with suppliers and vendors to improve security across your entire manufacturing ecosystem.
Maintain regulatory compliance. Ensure your cybersecurity program meets evolving regulatory requirements and industry standards relevant to your sector.
This industrial disaster recovery planning approach ensures you build capabilities systematically while maintaining operational continuity throughout the implementation process.
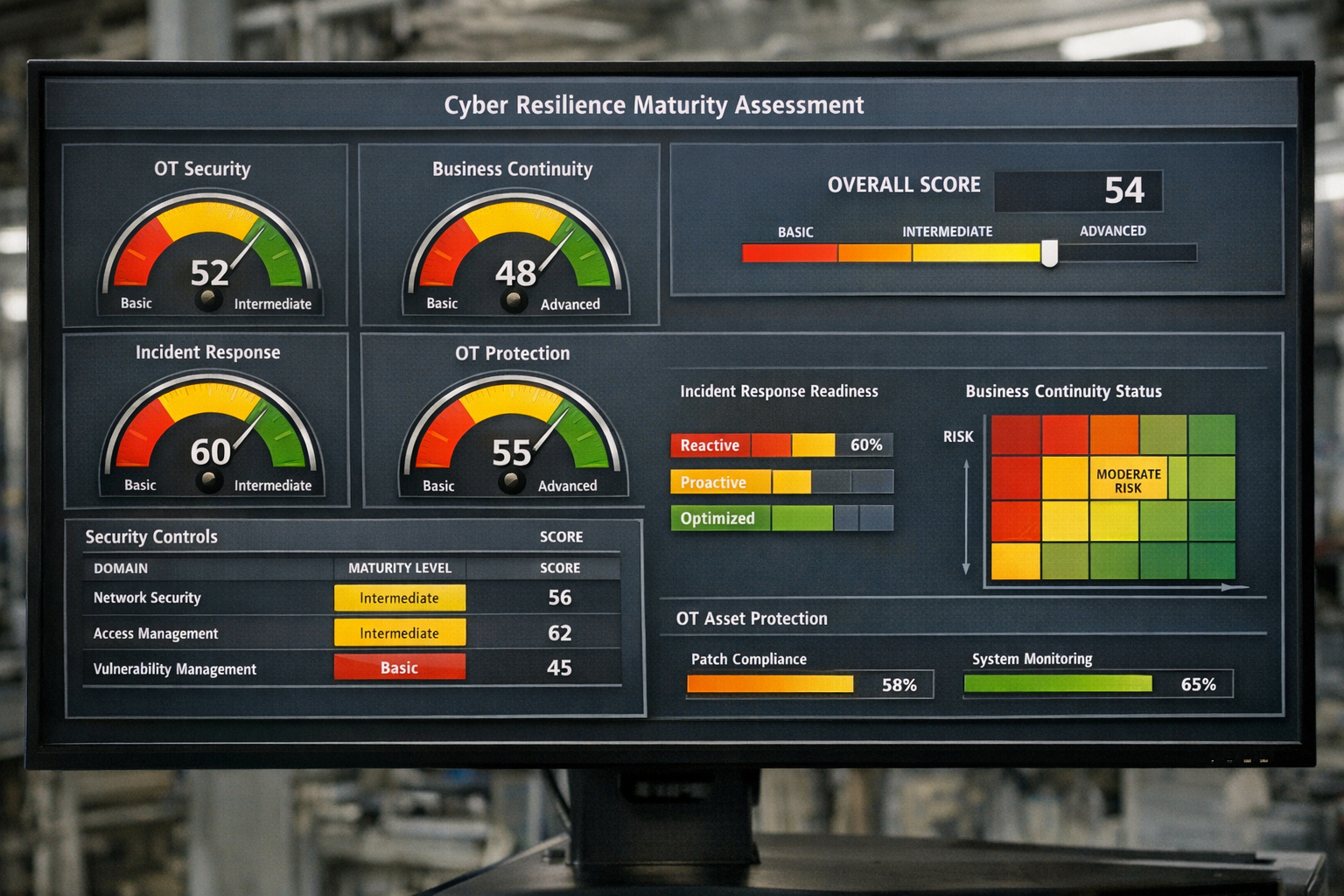
Measuring and Improving Your Cyber Resilience Maturity
Effective cyber resilience requires ongoing measurement and improvement. You need clear metrics that demonstrate progress and identify areas needing attention, but these metrics must be meaningful for manufacturing environments rather than generic IT measures.
Key Performance Indicators for Manufacturing Cyber Resilience
Mean Time to Detection (MTTD) for OT incidents. Measure how quickly your monitoring systems identify cybersecurity events affecting operational technology. Target detection times should account for the real-time nature of manufacturing processes.
Mean Time to Recovery (MTTR) for production systems. Track how long it takes to restore normal operations after a cyber incident. This metric should distinguish between different types of systems and incident severities.
Backup recovery success rates. Regularly test your ability to restore operational systems from backups and measure both success rates and recovery times for different scenarios.
Security awareness training completion. Monitor participation in cybersecurity training programs and measure knowledge retention through periodic assessments.
Vendor security assessment compliance. Track the percentage of third-party vendors that meet your cybersecurity requirements and maintain current security assessments.
Maturity Assessment Framework
Level 1 – Basic Protection: You have fundamental security controls in place, including basic network segmentation, antivirus software, and backup systems. Incident response is primarily reactive.
Level 2 – Managed Security: You’ve implemented comprehensive monitoring, established formal incident response procedures, and begun regular security training. Risk management processes are documented and followed.
Level 3 – Defined Resilience: Your organization has mature cybersecurity governance, integrated IT/OT security operations, and proactive threat hunting capabilities. Business continuity planning includes detailed cyber incident scenarios.
Level 4 – Predictive Operations: You use advanced analytics to predict and prevent security incidents, have automated response capabilities for common threats, and maintain real-time visibility across all operational systems.
Level 5 – Adaptive Resilience: Your cybersecurity program continuously evolves based on threat intelligence, operational changes, and lessons learned. You actively share threat information with industry partners and contribute to collective defense efforts.
Continuous Improvement Process
Quarterly security reviews. Conduct regular assessments of your cybersecurity posture, including reviews of recent incidents, changes to the threat landscape, and updates to operational systems.
Annual tabletop exercises. Practice incident response procedures through realistic scenarios that test both technical capabilities and organizational coordination under stress.
Peer benchmarking. Compare your cybersecurity maturity with industry peers through anonymous benchmarking studies or industry association programs.
Regulatory compliance audits. Use compliance assessments as opportunities to identify gaps in your cybersecurity program and drive improvements beyond minimum requirements.
Vendor security reviews. Regularly reassess the security postures of critical vendors and suppliers, especially those with access to operational systems.
Your manufacturing cybersecurity roadmap should include specific milestones for advancing through these maturity levels, with realistic timelines that account for operational constraints and resource availability.
Emergency Shutdown Cost Calculator
Estimate how much a cyber incident or outage could cost your business
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free ConsultationCommon Implementation Challenges and Solutions
Even with the best planning, implementing cyber resilience in manufacturing environments presents unique challenges that can derail your efforts if not addressed proactively.
Legacy System Integration
Challenge: Many manufacturers operate critical equipment that’s decades old and lacks basic security features. Replacing these systems isn’t financially feasible, but leaving them unprotected creates significant risks.
Solution: Implement compensating controls that add security layers without modifying the legacy systems themselves. This includes network segmentation, protocol filtering, and behavioral monitoring that can detect anomalies without requiring changes to the original equipment.
Operational Downtime Constraints
Challenge: Manufacturing operations often can’t tolerate the downtime required for security updates, system replacements, or comprehensive testing.
Solution: Develop phased implementation approaches that work around production schedules. Use redundant systems where possible to allow security to work on offline equipment. Plan major security initiatives during scheduled maintenance windows or seasonal shutdowns.
Skills and Resource Gaps
Challenge: Finding cybersecurity professionals who understand both IT security and operational technology is difficult and expensive.
Solution: Invest in training existing staff rather than trying to hire specialists. Partner with managed security service providers who have manufacturing expertise. Develop relationships with industry peers to share knowledge and resources.
Regulatory and Compliance Complexity
Challenge: Manufacturing organizations often face multiple, sometimes conflicting regulatory requirements that complicate cybersecurity planning.
Solution: Engage with regulatory bodies early in your planning process to understand requirements and acceptable approaches. Work with legal and compliance teams to ensure your cybersecurity program meets all applicable standards.
Vendor and Supply Chain Coordination
Challenge: Manufacturing cybersecurity depends heavily on equipment vendors, system integrators, and service providers who may have different security standards and capabilities.
Solution: Establish clear security requirements in vendor contracts and conduct regular security assessments of critical suppliers. Develop incident response procedures that account for vendor dependencies and communication requirements.
These challenges are common across the manufacturing industry, and addressing them proactively will significantly improve your chances of successful implementation.
Frequently Asked Questions
How long does it take to implement a comprehensive cyber resilience plan for manufacturing?
A complete cyber resilience program typically takes 12-18 months to implement fully, depending on your starting point and operational complexity. However, you can achieve meaningful risk reduction within the first 3-6 months by focusing on fundamental controls like network segmentation and backup systems.
What’s the typical cost of implementing manufacturing cyber resilience?
Costs vary significantly based on facility size and complexity, but most manufacturers should budget 2-5% of their annual IT spending for cybersecurity improvements. This includes both technology investments and staff training. The cost of a major cyber incident typically far exceeds these preventive investments.
How do we balance cybersecurity with operational safety requirements?
Always prioritize safety systems and ensure cybersecurity measures never interfere with emergency shutdown capabilities. Implement security controls in layers, with the most critical safety systems having the least restrictive security measures. Work closely with safety engineers to understand system interdependencies.
Can we implement cyber resilience without replacing legacy equipment?
Yes, most legacy systems can be protected through network-level controls, monitoring, and compensating security measures. Focus on isolating legacy systems, monitoring their communications, and implementing backup procedures rather than requiring system replacements.
What role should senior leadership play in cyber resilience planning?
Executive leadership is critical for success. Senior leaders must allocate resources, resolve conflicts between IT and OT teams, and ensure cybersecurity considerations are included in business continuity planning. They should also champion security awareness throughout the organization.
How often should we test our incident response procedures?
Conduct tabletop exercises quarterly and full-scale tests annually. Test different scenarios, including ransomware attacks, system failures, and supply chain disruptions. Include both technical response capabilities and business continuity procedures in your testing.
What’s the difference between cyber resilience and business continuity planning?
Business continuity planning addresses all types of disruptions to operations, while cyber resilience specifically focuses on maintaining operations during and after cybersecurity incidents. Cyber resilience should be integrated into your broader business continuity framework.
How do we handle cybersecurity for remote access to manufacturing systems?
Implement multi-factor authentication, time-limited access, and comprehensive logging for all remote connections. Use VPNs with strong encryption and consider implementing zero-trust network architectures. Monitor all remote access activities and maintain the ability to quickly revoke access if needed.
What cybersecurity training do manufacturing employees need?
All employees need basic cybersecurity awareness training covering phishing, password security, and incident reporting. OT personnel need specialized training on industrial cybersecurity threats and proper procedures for operational systems. IT staff need training on OT security considerations and manufacturing-specific threats.
How do we measure the effectiveness of our cyber resilience program?
Track metrics like mean time to detection and recovery, backup success rates, training completion, and incident response exercise results. Conduct regular maturity assessments and compare your capabilities against industry benchmarks. Most importantly, measure your ability to maintain operations during simulated incidents.
What should we look for in a managed security service provider for manufacturing?
Choose providers with specific experience in operational technology environments and an understanding of industrial protocols. They should offer 24/7 monitoring, incident response capabilities, and staff trained in manufacturing cybersecurity. Ensure they understand your operational constraints and safety requirements.
How do we handle cybersecurity for suppliers and vendors?
Establish clear security requirements in vendor contracts and conduct regular security assessments of critical suppliers. Implement network segmentation to limit vendor access to only necessary systems. Develop incident response procedures that account for vendor-related security incidents and communication requirements.
Conclusion
Building effective cyber resilience for manufacturers in 2026 requires more than just implementing the latest security technology. It demands a comprehensive approach that balances cybersecurity with operational requirements, integrates IT and OT systems thoughtfully, and prepares your organization to maintain critical functions even when under attack.
The manufacturing cybersecurity roadmap we’ve outlined provides a practical framework for developing these capabilities systematically. Start with a thorough assessment of your current environment, implement fundamental protections like network segmentation and backup systems, and gradually build more advanced capabilities like threat intelligence and predictive analytics.
Remember that cyber resilience is not a destination but an ongoing journey. The threat landscape continues to evolve, your operational environment changes over time, and new technologies create both opportunities and risks. Your cyber resilience program must evolve accordingly, with regular assessments, continuous improvement, and adaptation to changing circumstances.
The investment in cyber resilience pays dividends beyond just cybersecurity. Organizations with mature cyber resilience programs often find they have better operational visibility, more robust business continuity capabilities, and stronger relationships between IT and OT teams. These benefits improve overall operational efficiency and business performance.
Don’t wait for a cyber incident to expose gaps in your defenses. Start building your cyber resilience capabilities today, focusing first on the fundamentals and gradually expanding to more advanced capabilities. Your future self – and your stakeholders – will thank you for taking proactive steps to protect your operations and ensure business continuity.
Ready to strengthen your manufacturing cyber resilience? Contact our team for a comprehensive cybersecurity assessment tailored specifically for manufacturing environments. We’ll help you identify vulnerabilities, prioritize improvements, and develop a practical roadmap for building robust cyber resilience capabilities. Our industry expertise and personalized service approach ensure you get solutions that work with your operational requirements, not against them. Let us help you achieve the peace of mind that comes with knowing your operations can withstand and recover from cyber threats.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity