Article Summary
• Who this is for: Manufacturing executives, plant managers, and operations leaders responsible for protecting both production systems and business networks
• The challenge: IT and OT systems have different security priorities, but cyberattacks now target both—putting production uptime, safety, and revenue at serious risk
• Key insights covered: Core differences between IT and OT security, why traditional IT tools fail in industrial environments, network segmentation best practices, ransomware risks, and ICS security strategies
• Your outcome: Clear understanding of how to build a unified IT/OT security strategy that protects production, reduces downtime risk, and strengthens manufacturing resilience
Key Takeaways
• IT security protects data and business systems, while OT security safeguards production equipment and physical processes that keep your manufacturing operations running
• Traditional IT security tools often fail in OT environments because they can disrupt real-time operations and weren’t designed for industrial control systems
• Manufacturing cyber threats now target both networks, with ransomware attacks specifically designed to shut down production lines and cause maximum operational damage
• Network segmentation between IT and OT systems is critical, but must be implemented carefully to maintain necessary business connectivity
• Legacy OT systems create significant security gaps because they were built for reliability and uptime, not internet connectivity and cyber threats
• A unified security strategy addresses both domains while respecting their different operational requirements and risk tolerances
• Downtime costs in manufacturing can exceed $50,000 per hour, making OT security failures far more expensive than typical IT breaches
• Compliance requirements and cyber insurance now mandate specific protections for both IT and OT environments in manufacturing
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free ConsultationQuick Answer
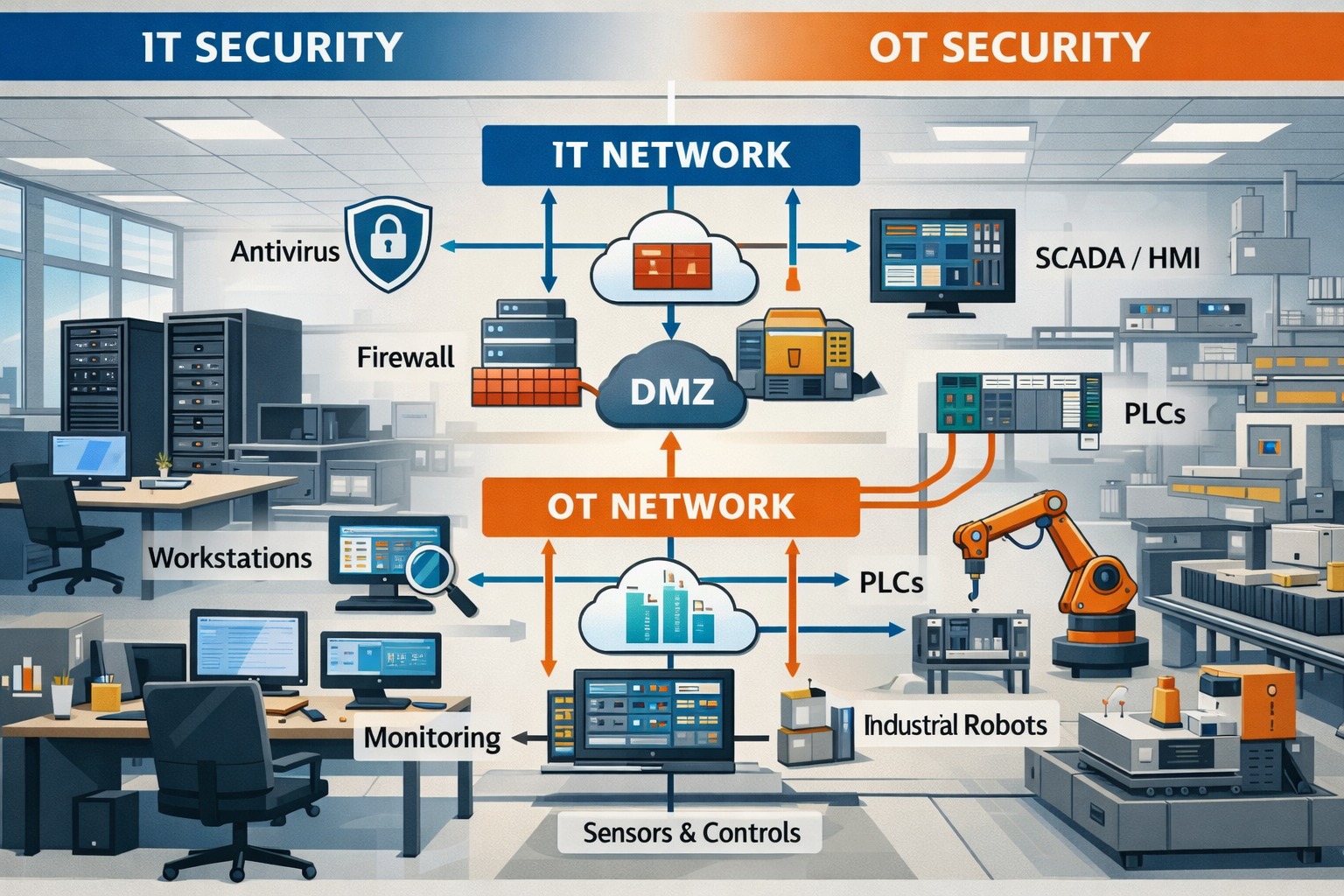
OT vs IT security in manufacturing represents two distinct but interconnected security domains. IT security focuses on protecting business data, networks, and traditional computer systems, while operational technology security safeguards the industrial control systems, SCADA networks, and production equipment that actually manufacture your products. The critical difference is that IT security prioritizes data confidentiality, while OT security must ensure production continuity and worker safety above all else.
What Is IT Security in Manufacturing?
IT security in manufacturing protects your business data, office networks, and traditional computer systems – essentially everything that supports your business operations but doesn’t directly control production equipment.
Your IT security covers systems like email servers, accounting software, customer databases, and employee workstations. These systems handle sensitive business information, financial data, and communications that keep your company running day-to-day.
Traditional IT security focuses on three main priorities:
• Confidentiality – Keeping sensitive data private and secure
• Integrity – Ensuring data accuracy and preventing unauthorized changes
• Availability – Maintaining system uptime for business operations
In most manufacturing companies, IT security teams manage firewalls, antivirus software, user access controls, and data backup systems. They can typically restart servers, install security patches, and perform maintenance during planned downtime windows without impacting production.
Choose traditional IT security approaches when you’re protecting business systems that can tolerate brief interruptions for security updates, patches, or incident response activities.
What Is Operational Technology Security?

Operational technology security protects the industrial control systems, SCADA networks, and production equipment that actually manufacture your products. This includes programmable logic controllers (PLCs), human-machine interfaces (HMIs), distributed control systems, and any technology that monitors or controls physical processes.
OT systems control everything from conveyor belts and robotic arms to temperature sensors and safety shutdown systems. These systems were originally designed for reliability and real-time performance, not cybersecurity.
OT security prioritizes completely different goals:
• Availability – Production must continue without interruption
• Safety – Worker protection and equipment safety come first
• Integrity – Process control data must be accurate and timely
• Confidentiality – Important but secondary to operational needs
The biggest challenge with OT cybersecurity risks is that these systems can’t be easily patched, restarted, or taken offline for security maintenance like traditional IT systems. A security update that requires a system reboot could shut down an entire production line.
Common mistake: Applying IT security tools directly to OT environments without considering operational impact. Many traditional security solutions can disrupt real-time communications and cause production delays.
Key Differences: IT vs OT Security in Manufacturing
| Aspect | IT Security | OT Security |
|---|---|---|
| Primary Goal | Protect business data and systems | Ensure production continuity and safety |
| Downtime Tolerance | Can handle planned maintenance windows | Minimal tolerance for any interruption |
| Update Frequency | Regular patches and updates | Infrequent updates due to operational risk |
| Network Access | Connected to the internet and corporate networks | Traditionally isolated or air-gapped |
| Lifespan | 3-5 years typical refresh cycle | 15-25 years is common for industrial equipment |
| Security Priority | Confidentiality first | Availability and safety first |
| Response Time | Minutes to hours acceptable | Milliseconds to seconds required |
| Compliance Focus | Data protection regulations | Safety and environmental standards |
This fundamental difference in priorities explains why traditional IT security approaches often fail in OT environments. Your production systems simply can’t tolerate the same security measures that work fine for business systems.
Why Traditional IT Security Fails in OT Environments
Traditional IT security tools can actually harm production operations when applied directly to OT systems. The problem isn’t that IT security is bad – it’s that operational technology has completely different requirements that most IT security solutions weren’t designed to handle.
Here’s what happens when IT security meets OT reality:
Real-time communication disruption occurs when security tools introduce latency or interrupt the precise timing that industrial control systems require. A firewall that takes an extra few milliseconds to inspect packets can cause a PLC to miss critical timing windows.
Patch management becomes nearly impossible because OT systems often can’t be taken offline for updates without stopping production. Many manufacturing companies run critical systems on decades-old operating systems because the risk of updating outweighs the security benefits.
Network scanning and vulnerability assessments can actually crash legacy OT systems that weren’t designed to handle unexpected network traffic. I’ve seen cases where routine IT security scans caused production equipment to fault and require a manual restart.
Antivirus software conflicts with real-time operations by consuming system resources and potentially blocking legitimate industrial communications. Many OT systems run on minimal hardware that can’t spare processing power for security software.
Choose specialized OT security solutions when you need to protect industrial systems without risking production disruption. These tools understand industrial protocols and can provide security monitoring without interfering with real-time operations.
Manufacturing Security Readiness Assessment
Evaluate your current IT and OT security posture to identify priority areas for improvement.
1. How are your IT and OT networks currently configured?
2. How often do you update OT system security?
3. Do you have visibility into OT network traffic and devices?
4. How do you handle remote access to production systems?
5. What is your incident response plan for OT security events?
Security Readiness Level
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free ConsultationReal Manufacturing Cyber Threats: When Production Becomes the Target
Manufacturing cyber threats have evolved from simple data theft to sophisticated attacks designed to shut down production and cause maximum operational damage. Today’s attackers understand that disrupting your production line is far more valuable than stealing your customer database.
Ransomware in manufacturing has become particularly devastating because attackers now target both your IT and OT systems simultaneously. They encrypt your business systems while also compromising the industrial controls that run your production equipment.
Here’s what a modern manufacturing cyberattack typically looks like:
Initial compromise usually starts through traditional IT channels – phishing emails, compromised credentials, or vulnerable internet-facing systems. Attackers establish a foothold in your business network first.
Lateral movement is where the real damage begins. Once inside your IT network, attackers look for connections to OT systems. Poor network segmentation makes this step easy for cybercriminals.
OT system infiltration allows attackers to map your production systems, understand your processes, and identify the most disruptive targets. They’re not just looking to encrypt files – they want to understand how to cause maximum production downtime.
Coordinated attack execution hits both domains simultaneously. Your business systems get encrypted while your production controls are either compromised or shut down entirely. Recovery becomes exponentially more complex when both IT and OT systems are affected.
Common mistake: Assuming that air-gapped OT systems are completely safe. Many “isolated” systems actually have hidden connections to business networks through engineering workstations, remote access systems, or shared infrastructure.
The financial impact extends far beyond ransom payments. Production downtime, emergency response costs, regulatory fines, and long-term reputation damage often cost manufacturers millions more than the initial ransom demand.
ICS Security Best Practices: Securing Production Environments

Industrial Control System (ICS) security requires a fundamentally different approach than traditional IT security because these systems control physical processes that can’t be easily stopped or restarted for security maintenance.
Start with network segmentation as your foundation. Your production systems should be separated from business networks with properly configured firewalls and monitoring systems. This doesn’t mean complete isolation – you still need some connectivity for business integration.
Implement these core ICS security best practices:
Asset discovery and inventory should be your first step. You can’t protect what you don’t know exists. Many manufacturing companies are surprised to discover how many connected devices are actually on their production networks.
Network monitoring specifically designed for OT environments can detect unusual communications without disrupting operations. Traditional network monitoring tools often miss industrial protocols or generate false alarms.
Secure remote access becomes critical when vendors, engineers, or operators need to connect to production systems. Direct VPN access to production networks creates unnecessary risk.
Change management processes must balance security with operational requirements. Every modification to production systems should be documented, tested, and approved, but the process can’t be so cumbersome that it prevents necessary maintenance.
SCADA security risks require special attention because these systems often have the highest level of access to critical production processes. Compromised SCADA systems can provide attackers with complete control over manufacturing operations.
Choose air-gapping for truly critical systems that don’t require network connectivity. Some safety systems and emergency shutdown controls should remain completely isolated from any network.
Backup and recovery procedures for OT systems are more complex than traditional IT backups because they often include specialized configurations, ladder logic, and process parameters that must be exactly right for safe operation.
IT and OT Network Segmentation: Building Secure Bridges
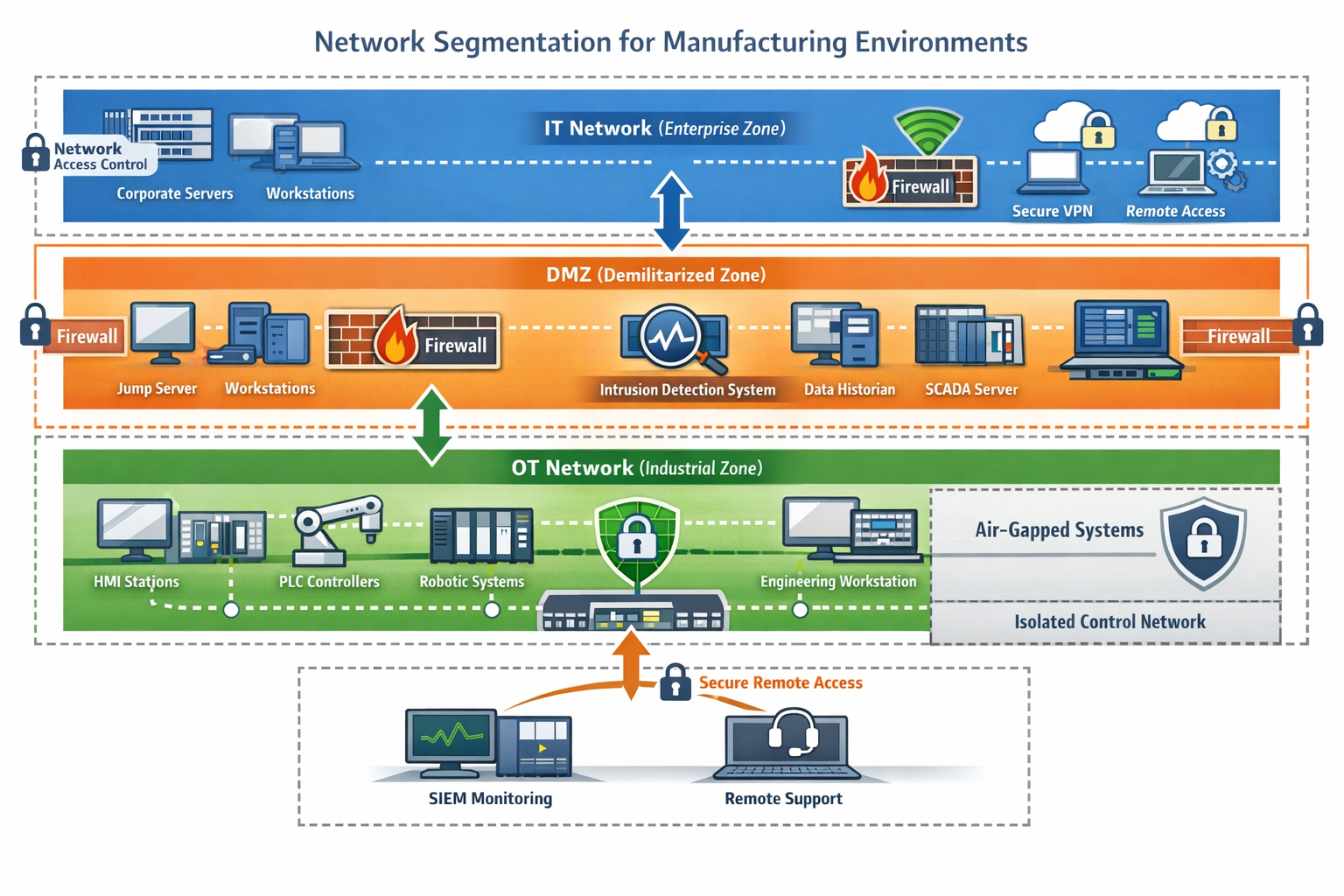
Effective IT and OT network segmentation creates secure boundaries while maintaining necessary business connectivity between your office systems and production environment. The goal isn’t complete isolation – it’s controlled, monitored communication.
Design your network architecture with multiple security zones:
Corporate IT zone includes your business systems, user workstations, email servers, and internet-connected applications. This zone can tolerate more security controls and regular maintenance.
DMZ (demilitarized zone) serves as a buffer between IT and OT networks. Shared services like engineering workstations, data historians, and application servers belong here.
OT zone contains your production systems, industrial controls, and safety systems. This zone prioritizes availability and real-time performance over security convenience.
Critical control zone houses your most sensitive systems like safety instrumented systems and emergency shutdown controls. These systems may be completely air-gapped.
Implement proper firewall rules that allow only necessary communications between zones. Default-deny policies work well, but you need to understand industrial protocols to write effective rules.
Monitor all inter-zone traffic with tools that understand both IT and OT communications. You want to detect unusual data flows without blocking legitimate operations.
Common mistake: Creating segmentation that looks good on paper but breaks necessary business processes. Work closely with operations teams to understand what connectivity is actually required.
Use industrial DMZ servers for functions that need access to both networks, such as manufacturing execution systems (MES) or enterprise resource planning (ERP) integration. This prevents direct connections between IT and OT zones.
Test your segmentation regularly to ensure that security controls don’t interfere with production operations and that necessary communications still work properly.
Why a Unified Security Strategy Is Critical in 2026
A unified security strategy addresses both IT and OT domains while respecting their different operational requirements and creates coordinated protection that’s greater than the sum of its parts. In 2026, the convergence of IT and OT systems makes this integration essential, not optional.
Modern manufacturing operations increasingly depend on connectivity between business systems and production equipment. Industry 4.0 initiatives, remote monitoring, predictive maintenance, and real-time analytics all require some level of integration between IT and OT networks.
Your unified strategy should include these key components:
Coordinated threat intelligence that understands both traditional cybersecurity threats and industrial-specific attack methods. Threats targeting one domain often have implications for the other.
Integrated monitoring and response capabilities that can correlate events across both IT and OT environments. An unusual login to a business system might be related to suspicious activity on the production network.
Consistent security policies that are adapted for each environment’s requirements. Your password policy might be the same across both domains, but patch management will necessarily be different.
Cross-trained security teams or partnerships with specialists who understand both domains. Traditional IT security teams need OT knowledge, while operations teams need cybersecurity awareness.
Unified incident response procedures that consider the operational impact of security decisions. Isolating a compromised business system is routine, but isolating production systems requires careful coordination with operations teams.
Choose a phased implementation approach that starts with the most critical gaps and gradually builds comprehensive protection. Don’t try to implement everything at once – that often leads to operational disruption and security gaps.
Leverage partnerships with experienced providers who understand both domains. At AlphaCIS, we’ve seen how proper integration of IT and OT security provides peace of mind while maintaining the operational excellence that manufacturing companies depend on.
Frequently Asked Questions
Q: Can I use the same antivirus software on both IT and OT systems?
A: No, traditional antivirus software can disrupt OT operations. Use industrial-grade security solutions designed for real-time systems, or implement application whitelisting instead of signature-based detection.
Q: How often should I patch OT systems compared to IT systems?
A: IT systems should be patched monthly or as needed. OT systems require careful change management and are typically updated during planned maintenance windows, often quarterly or annually, with thorough testing.
Q: What’s the biggest security mistake manufacturers make?
A: Treating OT systems like IT systems. Applying IT security tools and procedures directly to production systems without considering operational impact often creates more problems than it solves.
Q: How much does manufacturing downtime really cost?
A: Costs vary by industry and company size, but many manufacturers face $50,000 to $500,000 per hour of unplanned downtime when including lost production, labor costs, and recovery expenses.
Q: Should OT systems be completely isolated from the internet?
A: Critical safety systems should be air-gapped, but complete isolation isn’t practical for most modern manufacturing. Proper segmentation with controlled connectivity is usually the right approach.
Q: How do I know if my current security covers OT systems adequately?
A: Conduct an OT-specific security assessment. Traditional IT security audits often miss industrial control system vulnerabilities and operational security gaps.
Q: What’s the first step in improving OT security?
A: Start with asset discovery and network mapping. You need to understand what systems you have and how they’re connected before you can protect them effectively.
Q: Can cloud-based security solutions work for OT environments?
A: Hybrid approaches work best. Cloud-based threat intelligence and management can enhance OT security, but local monitoring and control systems ensure operations continue even with connectivity issues.
Q: How do I balance security with operational requirements?
A: Work closely with operations teams to understand critical processes and timing requirements. Implement security controls that enhance rather than hinder operational excellence.
Q: What compliance requirements apply to OT security?
A: Requirements vary by industry but may include NERC CIP for utilities, FDA regulations for pharmaceuticals, or ISO 27001 for general manufacturing. Cyber insurance increasingly requires specific OT protections.
Q: How quickly can attackers move from IT to OT systems?
A: With poor segmentation, attackers can reach OT systems within hours of initial IT compromise. Proper segmentation and monitoring can extend this to days or weeks, giving you time to respond.
Q: What’s the ROI of investing in OT security?
A: The primary ROI comes from avoiding downtime costs and maintaining operational continuity. Even preventing one major incident often justifies the entire security investment.
Conclusion
The convergence of IT and OT systems in modern manufacturing creates both tremendous opportunities and significant security challenges. While traditional IT security focuses on protecting data and business systems, operational technology security must safeguard the production equipment and industrial processes that actually manufacture your products.
The key insight is that these two domains require different approaches but coordinated strategies. Your IT systems can tolerate brief interruptions for security maintenance, but your production systems need continuous availability and real-time performance. Traditional IT security tools often fail in OT environments because they weren’t designed for industrial control systems and can actually disrupt manufacturing operations.
The threat landscape has evolved dramatically, with attackers now specifically targeting manufacturing operations to cause maximum operational damage. Ransomware attacks increasingly hit both IT and OT systems simultaneously, making recovery exponentially more complex and expensive.
Your next steps should focus on three critical areas:
Assess your current security posture across both IT and OT environments. Many manufacturers discover significant gaps when they evaluate their operational technology security for the first time. Understanding what you have and how it’s protected provides the foundation for improvement.
Implement proper network segmentation between IT and OT systems while maintaining necessary business connectivity. This creates secure boundaries that protect production systems without completely isolating them from beneficial business integration.
Develop a unified security strategy that addresses both domains with coordinated policies, monitoring, and response procedures. This doesn’t mean identical approaches – it means complementary strategies that work together effectively.
The investment in comprehensive IT and OT security protection pays for itself by preventing costly production downtime, maintaining operational excellence, and providing the peace of mind that comes from knowing your manufacturing operations are secure and resilient.
As a reliable partner in manufacturing security, AlphaCIS understands the unique challenges of protecting both business systems and production environments. Our industry expertise and personalized service approach help manufacturers implement effective security strategies without disrupting the operations that drive their success.
Ready to Take IT Off Your Plate?
Stop worrying about downtime, security risks, or endless IT frustrations. AlphaCIS is the trusted IT partner for small and mid-sized businesses in Metro Atlanta, keeping systems secure, connected, and running the way they should every day.
Whether it’s preventing costly outages, protecting your data, or giving your team unlimited support, we make sure technology helps your business grow instead of holding it back.
📅 Book Your Free Consultation
Dmitriy Teplinskiy
I have worked in the IT industry for 15+ years. During this time I have consulted clients in accounting and finance, manufacturing, automotive and boating, retail and everything in between. My background is in Networking and Cybersecurity



